Source: www.techrepublic.com – Author: TechRepublic Academy Published April 5, 2024 We may earn from vendors via affiliate links or sponsorships. This might affect product placement on...
Author: CISO2CISO Editor 2
Mastering the CISO role: Navigating the leadership landscape – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Cindi Carter, Field CISO West at Check Point, and Pete Nicoletti, Field CISO East at Check Point, recently advanced the following...
Google sues crypto investment app makers over alleged massive “pig butchering” scam – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley Two China-based Android app developers are being sued by Google for an alleged scam targeting 100,000 users worldwide through fake...
New Ivanti RCE flaw may impact 16,000 exposed VPN gateways – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Approximately 16,500 Ivanti Connect Secure and Poly Secure gateways exposed on the internet are likely vulnerable to a remote code...
Microsoft fixes Windows Sysprep issue behind 0x80073cf2 errors – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft has fixed a known issue causing 0x80073cf2 errors when using the System Preparation (Sysprep) tool after installing November Windows 10...
Fake Facebook MidJourney AI page promoted malware to 1.2 million people – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Hackers are using Facebook advertisements and hijacked pages to promote fake Artificial Intelligence services, such as MidJourney, OpenAI’s SORA and...
Acuity confirms hackers stole non-sensitive govt data from GitHub repos – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Acuity, a federal contractor that works with U.S. government agencies, has confirmed that hackers breached its GitHub repositories and stole...
Panera Bread week-long IT outage caused by ransomware attack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Panera Bread’s recent week-long outage was caused by a ransomware attack, according to people familiar with the matter and emails...
Chinese Threat Actors Deploy New TTPs to Exploit Ivanti Vulnerabilities – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Chinese threat actors have developed new techniques to move laterally post-exploitation of Ivanti vulnerabilities, new research from Mandiant has revealed. Five...
Wiz Discovers Flaws in GenAI Models Enabling Customer Data Theft – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cloud security provider Wiz found two critical architecture flaws in generative AI models uploaded to Hugging Face, the leading hub for...
Maybe the Phone System Surveillance Vulnerabilities Will Be Fixed – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier It seems that the FCC might be fixing the vulnerabilities in SS7 and the Diameter protocol: On March 27 the...
Surveillance by the New Microsoft Outlook App – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier The ProtonMail people are accusing Microsoft’s new Outlook for Windows app of conducting extensive surveillance on its users. It shares...
Class-Action Lawsuit against Google’s Incognito Mode – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier The lawsuit has been settled: Google has agreed to delete “billions of data records” the company collected while users browsed...
SEXi Ransomware Desires VMware Hypervisors in Ongoing Campaign – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Don McBailey/Stockimo via Alamy Stock Photo What appears to be a fresh variant of...
Ivanti Pledges Security Overhaul the Day After 4 More Vulns Disclosed – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: garagestock via Shutterstock Ivanti CEO Jeff Abbott this week said his company will completely revamp its security...
Malicious Latrodectus Downloader Picks Up Where QBot Left Off – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading Source: Yuri Arcurs via Alamy Stock Photo At first, analysts thought the downloader was a variant...
Thousands of Australian Businesses Targeted With ‘Reliable’ Agent Tesla RAT – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Leyden, Contributing Writer Source: David Chapman via Alamy More than 11,000 Australian companies were targeted in a recent wave of cyberattacks...
Action1 Unveils ‘School Defense’ Program To Help Small Educational Institutions Thwart Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Houston, Texas, April 04, 2024 (GLOBE NEWSWIRE) — Action1 Corporation, a provider of the integrated real-time vulnerability discovery and patch...
‘Unfaking’ News: How to Counter Disinformation Campaigns in Global Elections – Source: www.darkreading.com
Source: www.darkreading.com – Author: Shamla Naidoo Shamla Naidoo, Head of Cloud Strategy & Innovation, Netskope April 3, 2024 5 Min Read Source: Feng Yu via Alamy...
Senior Tory ‘mortified’ after reportedly passing MPs’ data to dating app contact – Source: www.theguardian.com
Source: www.theguardian.com – Author: Nadeem Badshah A senior Conservative MP has reportedly admitted to giving out the personal phone numbers of colleagues to a person he...
Police launch inquiry after MPs targeted in apparent ‘spear-phishing’ attack – Source: www.theguardian.com
Source: www.theguardian.com – Author: Ben Quinn and Eleni Courea A police investigation has been launched after MPs were apparently targeted in a “spear-phishing” attack, in what...
A 5-Minute Refresher to Cryptography – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Gary (featuring Alice and Bob) by Rajvi Shroff It’s an age-old question. Alice wants to send a message to Bob. But how...
Smart Traffic Signals Security in the Era of AI and Smart Cars – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Gary Analyzing the Trade-off Between Efficiency and Security in Smart Traffic Signal Technology Integration. by Samridhi Agarwal, Masters Student, CMU Once a...
Impact of IoT Security for 5G Technology – Source: securityboulevard.com
Source: securityboulevard.com – Author: Riddika Grover 5G technology impacts not just our daily lifestyle but the Internet of Things (IoT) as well. The world of 5G...
HTTP/2 CONTINUATION Flood Vulnerability – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nadav Avital HTTP/2, a widely adopted web communication protocol, organizes data transmission through a binary framing layer, wherein all communication is divided...
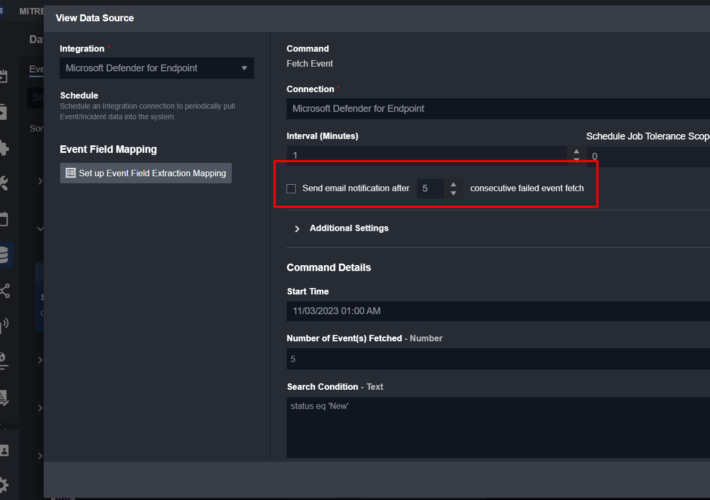
Smart SOAR’s Innovative Approach to Error-Handling Explained – Source: securityboulevard.com
Source: securityboulevard.com – Author: Shriram Sharma Our commitment to innovation is deeply rooted in the feedback we receive from those who use our Smart SOAR platform...
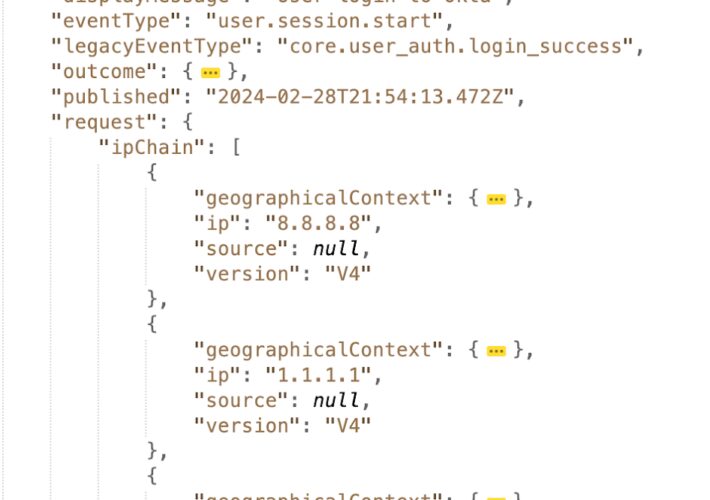
How to Correctly Use Client IP Addresses in Okta Audit Logs to Improve Identity Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Farah Iyer Being able to identify client IP addresses is essential for detecting and preventing identity-related threats. These IP addresses help establish...
Testing in Detection Engineering (Part 8) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Anton Chuvakin This blog series was written jointly with Amine Besson, Principal Cyber Engineer, Behemoth CyberDefence and one more anonymous collaborator. This...
Google Chrome Enlists Emerging DBSC Standard to Fight Cookie Theft – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Google is prototyping a new technology in Chrome that is designed to thwart the growing trend among cybercriminals of stealing...
Mastering MITRE: Enhancing Cybersecurity with Device Log Mapping – Source: securityboulevard.com
Source: securityboulevard.com – Author: Team Nuspire In the dynamic realm of cybersecurity, the MITRE ATT&CK framework has become a pivotal tool for organizations striving to fortify...