Source: securityboulevard.com – Author: Tejas Ranade While AI has created exciting new opportunities for business, it has created urgent questions around ethics, responsible use, development, and...
Author: CISO2CISO Editor 2
PIPEDA Compliance with Accutive Data Discovery and Masking: Understanding and protecting your Canadian sensitive data – Source: securityboulevard.com
Source: securityboulevard.com – Author: Accutive Security What is PIPEDA, Canada’s Personal Information Protection and Electronic Documents Act? PIPEDA, or the Personal Information Protection and Electronic Documents...
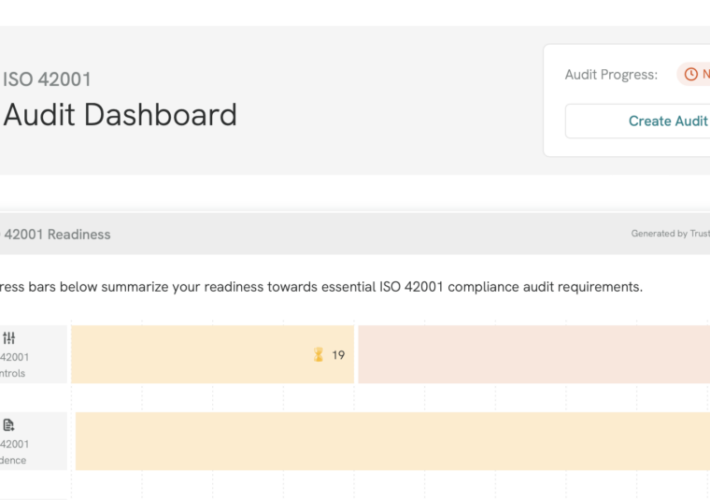
TrustCloud Product Updates: April 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tejas Ranade You know us: Every month we’re cooking up something new! Here are the updates that hit TrustCloud this month. TrustShare...
News alert: Cybersixgill unveils ‘Third-Party Intelligence’ to deliver vendor-specific threat intel – Source: securityboulevard.com
Source: securityboulevard.com – Author: bacohido Tel Aviv, Israel – April 30, 2024 – Cybersixgill, the global cyber threat intelligence data provider, broke new ground today by introducing its Third-Party Intelligence module....
April Recap: New AWS Services and Sensitive Permissions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tally Shea Amazon Web Services (AWS) has over 200 cloud services available to help organizations innovate, build business, and secure their data....
AI Voice Scam – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments Clive Robinson • May 1, 2024 8:28 AM @ Bruce, ALL, In a world that is moving rapidly...
WhatsApp in India – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments numberri • April 30, 2024 7:42 AM I know another case earlier this year is when India threatened...
Island Gets $175M Series D Funding, Doubles Valuation to $3B – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Endpoint Security Investments in Island Led by Coatue and Sequoia Support Global Expansion, R&D, M&A Michael Novinson (MichaelNovinson) • April 30,...
How Personal Branding Can Elevate Your Tech Career – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Training & Security Leadership Your Personal Brand Is as Crucial as Any Skill in Your Tech Toolkit Brandy Harris • April...
DHS: AI-Enhanced Nuclear and Chemical Threats Are Risk to US – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development New Report Says Global Threat Actors May Use AI to...
Defining a Detection & Response Strategy – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Verizon Breach Report: Vulnerability Hacks Tripled in 2023 – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Video , Vulnerability Assessment & Penetration Testing (VA/PT) Data Breach Report Lead Author Alex Pinto Discusses...
Patched Deserialization Flaw in Siemens Product Allows RCE – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Critical Infrastructure Security The Siemens Simatic Energy Manager Used an Unsafe BinaryFormatter Method Prajeet Nair (@prajeetspeaks) • April 30, 2024 ...
Attackers Planted Millions of Imageless Repositories on Docker Hub – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Tada Images via Shutterstock Docker has removed nearly 3 million public repositories from Docker Hub after researchers...
Canadian Drug Chain in Temporary Lockdown Mode After Cyber Incident – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: ton koene via Alamy Stock Photo London Drugs, a Canadian pharmacy chain, has closed its...
To Damage OT Systems, Hackers Tap USBs, Old Bugs & Malware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Mohammad Aaref Barahouei via Alamy Stock Photo Industrial cyberattackers are increasingly using removable media to penetrate operational...
Wireless Carriers Face $200M FCC Fine As Data Privacy Waters Roil – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Wavebreak Media ltd via Alamy Stock Photo The Federal Communications Commission (FCC) has fined the top US...
The 6 Data Security Sessions You Shouldn’t Miss at RSAC 2024 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Liat Hayun Liat Hayun, Co-Founder & CEO, Eureka Security April 30, 2024 3 Min Read Source: Aleksandr Matveev via Alamy Stock Photo...
New Research Suggests Africa Is Being Used As a ‘Testing Ground’ for Nation State Cyber Warfare – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE London, UK. 24th April 2024: Performanta, the multinational cybersecurity firm specialising in helping companies move beyond security to achieve cyber safety, has...
MITRE’s Cyber Resiliency Engineering Framework Aligns With DoD Cyber Maturity Model Cert – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE McLean, Va. & Bedford, Mass., April 25, 2024 — MITRE’s Cyber Resiliency Engineering Framework (CREF) NavigatorTM now incorporates the US...
How AI can benefit zero trust – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: The zero trust framework is a cornerstone of modern cyber security threat prevention and defense architectures. At its core,...
Say goodbye to standard security for smartphones (you need this instead) – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau By Zahier Madhar, Lead Security Engineer and Office of the CTO, Check Point. Smartphones play a pivotal role in all of...
Ransomware attack causes city street lights to “misbehave” – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: In England, Leicester City is experiencing persistent problems with its street light system due to a recent cyber attack....
The evolution from BEC to BCC – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau David Meister is a valued technology expert with over 15 years of experience in technical and consultancy roles across a range...
Top 10 things CISOs should know about AI security tools – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: As reported by executives, the top tangible benefit of AI is cyber security and risk management optimization. Right now,...
Secure out-of-band console and power management for Check Point security gateways – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Contributed by WTI as part of Check Point’s CPX silver-level partner sponsorship opportunity. WTI is an industry leader in out-of-band network...
The MSSP perspective: CISO insights into stronger security – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Gary Landau has been leading IT and information security teams for over 25 years as part of startups as well as...
News alert: Cybersixgill unveils ‘Third-Party Intelligence’ to deliver vendor-specific threat intel – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido Tel Aviv, Israel – April 30, 2024 – Cybersixgill, the global cyber threat intelligence data provider, broke new ground today by introducing its Third-Party Intelligence module....
GUEST ESSAY: Recalibrating critical infrastructure security in the wake of evolving threats – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Joseph Bell For all the discussion around the sophisticated technology, strategies, and tactics hackers use to infiltrate networks, sometimes the...
RSAC Fireside Chat: Secure, flexible web browsers finally available, thanks to open-source code – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido At the end of 2000, I was hired by USA Today to cover Microsoft, which at the...