Source: securityboulevard.com – Author: Nathan Eddy Identity and credential misconfigurations pose a major security risk to organizations, with companies in energy, manufacturing and financial services particularly...
Author: CISO2CISO Editor 2
Tracking CVE-2024-2876: Why does the latest WordPress exploit compromise over 90,000 websites? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nikhil Menon A highly concerning security loophole was recently discovered in a WordPress plugin called “Email Subscribers by Icegram Express,” a popular...
Got Your Eyes on Cyber Essentials Plus? We’ve Got You Covered! – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mor Avni, Product Manager, Scytale With data breaches and hacking attacks in the headlines way too often, strengthening digital defenses has become...
Understanding GitGuardian’s Self-Hosted Solution – Source: securityboulevard.com
Source: securityboulevard.com – Author: Greg Bulmash At GitGuardian, as cybersecurity experts, we understand there are a variety of reasons our customers might not want a cloud-based...
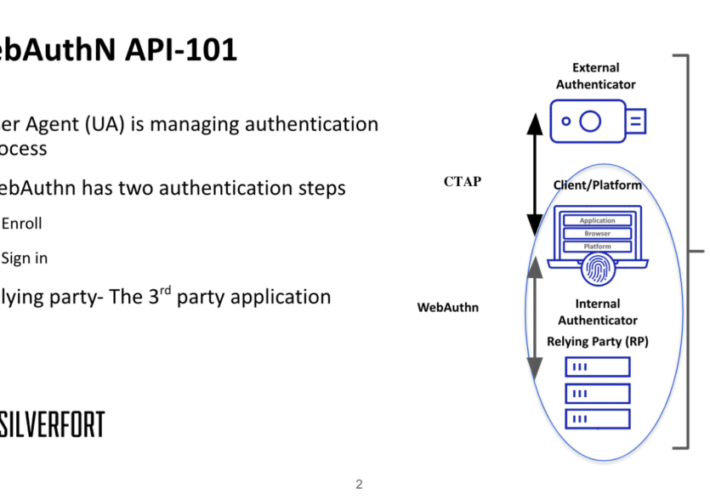
Using MITM to bypass FIDO2 phishing-resistant protection – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dor Segal FIDO2 is a modern authentication group term for passwordless authentication. The Fast Identity Online (FIDO) Alliance developed it to replace the...
USENIX Security ’23 – A Bug’s Life: Analyzing the Lifecycle and Mitigation Process of Content Security Policy Bugs – Distinguished Paper Award Winner – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Home » Security Bloggers Network » USENIX Security ’23 – A Bug’s Life: Analyzing the Lifecycle and Mitigation Process of...
Financial cyberthreats in 2023 – Source: securelist.com
Source: securelist.com – Author: Kaspersky Money is what always attracts cybercriminals. A significant share of scam, phishing and malware attacks is about money. With trillions of...
Amnesty International Cites Indonesia as a Spyware Hub – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Rawf8 via Alamy Stock Photo New research from Amnesty International’s Security Lab identifies Indonesia as...
Celebrating our 12th Anniversary at RSA conference 2024 – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Gary It’s been an amazing journey and we are so thankful to the team at the RSA Conference for working with us...
Offensive Awakening: The 2024 Shift from Defensive to Proactive Security – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Adversarial Cyber Exercises Are The New Mandate By Stephen Gates, Principal SME, Horizon3.ai After observing the cyber threat landscape in...
Navigating the Digital Age: AI’s Crucial Role in Cybersecurity Reinforcement – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Harnessing the Power of AI for Advanced Cyber Threat Intelligence and Prevention By Bryan Kissinger, Senior Vice President of Security...
GenAI Continues to Dominate CIO and CISO Conversations – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lohrmann on Cybersecurity The NASCIO Midyear Conference this past week highlighted the good, the bad and the scary of generative AI, as...
RSAC 2024 Innovation Sandbox | Reality Defender: Deepfake Detection Platform – Source: securityboulevard.com
Source: securityboulevard.com – Author: NSFOCUS The RSA Conference 2024 will kick off on May 6. Known as the “Oscars of Cybersecurity,” the RSAC Innovation Sandbox has...
USENIX Security ’23 – Silent Bugs Matter: A Study of Compiler-Introduced Security Bugs – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters: Jianhao Xu, Kangjie Lu, Zhengjie Du, Zhu Ding, Linke Li Qiushi Wu, Mathias Payer, Bing Mao Many thanks to...
RSAC 2024 Innovation Sandbox | Dropzone AI: Automated Investigation and Security Operations – Source: securityboulevard.com
Source: securityboulevard.com – Author: NSFOCUS The RSA Conference 2024 will kick off on May 6. Known as the “Oscars of Cybersecurity,” the RSAC Innovation Sandbox has...
DD2345 Military Critical Technical Data Agreement and CMMC – Source: securityboulevard.com
Source: securityboulevard.com – Author: Max Aulakh What is the government if not an organization dedicated to the creation of paperwork? All of that paperwork means something,...
Navigating the API Security Landscape: A CEO’s Perspective on Embedding Zero Trust Principles – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Stevin By Jyoti Bansal, CEO and Co-Founder, Traceable AI In the dynamic world of digital transformation, I’ve observed a paradigm shift that...
Friday Squid Blogging: Squid Purses – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments ResearcherZero • May 3, 2024 8:53 PM Journalist killings are at their highest levels in almost a decade....
Mimic Launches With New Ransomware Defense Platform – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Ihor Sveitukha via Alamy Stock Photo The number of ransomware and associated extortion attacks is...
The Real Risk is Not Knowing Your Real Risk: Perspectives from Asia Pacific Tour with EY – Source: securityboulevard.com
Source: securityboulevard.com – Author: Arun Dhamija Recently, I wrapped up my first work trip with Balbix—a whirlwind tour of customer roundtables in Singapore, Melbourne and Sydney....
Airsoft Data Breach Exposes Data of 75,000 Players – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nathan Eddy Failure to properly configure authentication led to malicious actors exploiting the database backups of Airsoftc3.com, a popular Airsoft enthusiast community...
Get SOAR Savvy Before RSAC 2024: 5 Reads to Level Up Your SOC – Source: securityboulevard.com
Source: securityboulevard.com – Author: Shriram Sharma For security leaders heading to RSAC 2024 in need of a refresher on all things SOAR (Security Automation, Orchestration and...
Cloud Monitor Automation Thwarts Phishing & Malware Emails – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alexa Sander We recently hosted Michael Tapia, Chief Technology Director at Clint ISD in Texas, and Kobe Brummet, Cybersecurity Technician at Hawkins...
MY TAKE: Is Satya Nadella’s ‘Secure Future Initiative’ a deja vu of ‘Trustworthy Computing?’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: bacohido By Byron V. Acohido SAN FRANCISCO — On the eve of what promises to be a news-packed RSA Conference 2024, opening...
Palo Alto Networks Extends SASE Reach to Unmanaged Devices – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard Palo Alto Networks this week extended its secure access service edge (SASE) platform to make it possible to apply cybersecurity...
USENIX Security ’23 – Cryptographic Deniability: A Multi-perspective Study of User Perceptions and Expectations – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX Security ’23 – Cryptographic Deniability: A Multi-perspective Study of User...
The impact of automating open source dependency management – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jamie Coleman Recently, I chatted with developers from a customer in a heavily regulated industry. They were manually updating their open source...
Unlocking SMB Cybersecurity: The Rise of Virtual CISOs in 2024 and Beyond – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matthew Rosenquist This year, virtual CISOs must begin making a difference in our industry. For the longest time, small and medium businesses...
Vulnerability of the Month – Controversy of the JetBrains TeamCity CVE-2024-27198 & CVE-2024-27199 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mackenzie Jackson In this blog series, we look at a new CVE each month and discuss its impact, discovery, and remediation. This...
How Intel 471’s Buy of Cyborg Is Reshaping Threat Hunting – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Next-Generation Technologies & Secure Development , Threat Hunting , Threat Intelligence Why Customers Benefit From Bringing Threat Hunting and Threat Intelligence...