Source: securityboulevard.com – Author: Natalia Kazankova As vehicles become increasingly reliant on software, secure and functional Hardware Security Modules (HSMs) are paramount. Unknown vulnerabilities in your...
Author: CISO2CISO Editor 2
Dropbox Sign Breach: Threat Actors Access User Information – Source: securityboulevard.com
Source: securityboulevard.com – Author: Wajahat Raja In a recent disclosure, cloud storage giant Dropbox revealed a breach affecting its digital signature service, Dropbox Sign (formerly HelloSign)....
Incident response analyst report 2023 – Source: securelist.com
Source: securelist.com – Author: Kaspersky GERT, Kaspersky Security Services SOC, TI and IR posts SOC, TI and IR posts 14 May 2024 minute read Incident response...
FCC Names and Shames First Robocall Threat Actor – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The US telecoms regulator has named a malicious robocall group for the first time, in a bid to help international partners...
How ‘Radical Transparency’ Can Bolster Cybersecurity – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Events , RSA Conference , RSA Conference Videos Ex-DHS Official Suzanne Spaulding and Jim Richberg of Fortinet on Critical Concepts Mathew...
Experts Warn the NVD Backlog Is Reaching a Breaking Point – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Government , Industry Specific Federal Database Nears 10,000 Unanalyzed Vulnerabilities Amid Halt in Operations Chris Riotta...
Defenders’ Dilemma: Can AI Bolster Cyber Resilience? – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Events , Next-Generation Technologies & Secure Development Visa’s Subra Kumaraswamy on Threat Detection, AI and...
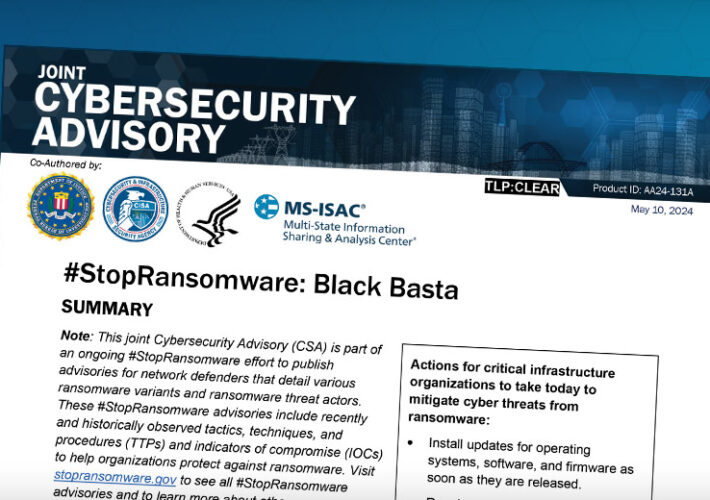
Feds, Groups Warn Health Sector of Black Basta Threats – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific Advisories Come As Black Basta Appears Responsible for Ascension Ransomware Attack Marianne...
Report: Organisations Have Endpoint Security Tools But Are Still Falling Short on the Basics – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Ben Abbott Most IT and security teams would agree that ensuring endpoint security and network access security applications are running in compliance...
Prison for cybersecurity expert selling private videos from inside 400,000 homes – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley A Korean cybersecurity expert has been sentenced to prison for illegally accessing and distributing private videos from vulnerable “wallpad” cameras...
The Next Generation of Endpoint Security Is Being Reimagined Today – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Vivek Ramachandran, CEO & Founder, SquareX Gone are the days when traditional antivirus solutions were the bulwark of endpoint...
500 Victims In, Black Basta Reinvents With Novel Vishing Strategy – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: ciaobucarest via Alamy Stock Photo A new Black Basta campaign is annoying victims into submission with onslaughts...
Ukrainian, Latvian TV Hijacked to Broadcast Russian Celebrations – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Trambler58 via Shutterstock A Ukrainian agency in charge of television and radio broadcasting reported that...
IntelBroker Nabs Europol Info; Agency Investigating – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Deco via Alamy Stock Photo A well-known hacking outfit called “IntelBroker” has put up...
Why Tokens Are Like Gold for Opportunistic Threat Actors – Source: www.darkreading.com
Source: www.darkreading.com – Author: John A. Smith John A. Smith, Founder & Chief Security Officer, Conversant Group May 13, 2024 4 Min Read Source: Leigh Prather...
LLMs’ Data-Control Path Insecurity – Source: www.schneier.com
Source: www.schneier.com – Author: B. Schneier Back in the 1960s, if you played a 2,600Hz tone into an AT&T pay phone, you could make calls without...
How Did Authorities Identify the Alleged Lockbit Boss? – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs Last week, the United States joined the U.K. and Australia in sanctioning and charging a Russian man named Dmitry Yuryevich Khoroshev...
Criminal IP and Quad9 Collaborate to Exchange Domain and IP Threat Intelligence – Source: securityboulevard.com
Source: securityboulevard.com – Author: cybernewswire Torrance, California, May 13th, 2024, CyberNewsWire Criminal IP, a renowned Cyber Threat Intelligence (CTI) search engine developed by AI SPERA, has...
CISOs Reconsider Their Roles in Response to GenAI Integration – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nathan Eddy Chief information security officers (CISOs) face mounting pressure as cyberattacks surge and complexities surrounding the implementation of GenAI and AI...
Votiro Named Market Leader in Data Security by the 2024 CDM Awards – Source: securityboulevard.com
Source: securityboulevard.com – Author: Votiro It’s been less than three months since the launch of our unified content and data security platform and we’re already being...
Veriti Extends Exposure Assessment & Remediation to the Cloud – Source: securityboulevard.com
Source: securityboulevard.com – Author: Veriti As enterprises continue to shift towards cloud-based infrastructures, the complexity of managing and securing these environments grows. Recognizing this, Veriti is...
Authorised Economic Operator: Cyber Security Requirements – Source: securityboulevard.com
Source: securityboulevard.com – Author: Leah Hopper Introduction Authorised Economic Operator (AEO) is a status that a lot of UK companies want to obtain for the sake...
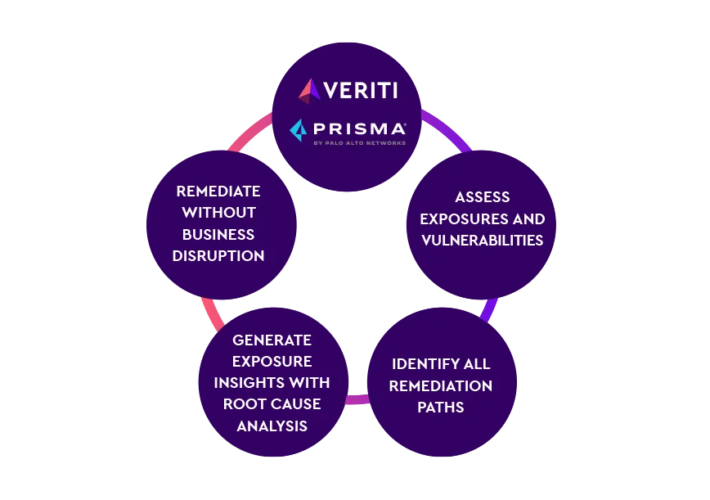
PRISMA CLOUD – Source: securityboulevard.com
Source: securityboulevard.com – Author: Veriti Veriti proactively monitors and safely remediates risk across the security infrastructure to elevate CNAPP by remediating compensating controls, without disrupting the...
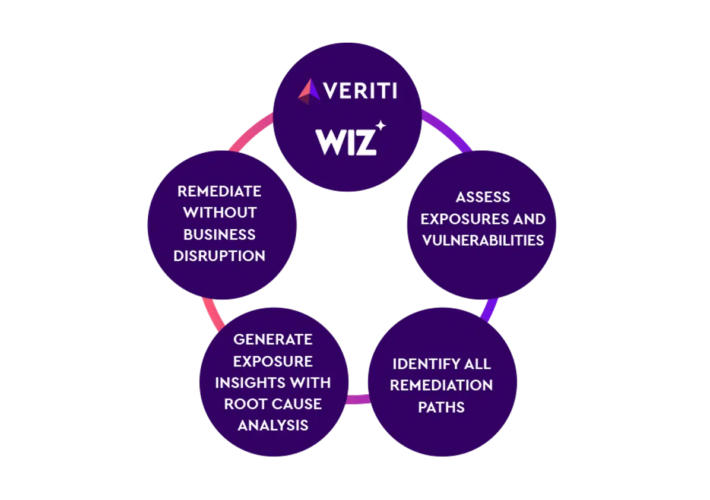
Wiz – Source: securityboulevard.com
Source: securityboulevard.com – Author: Veriti Veriti proactively monitors and safely remediates risk across the security infrastructure to elevate CNAPP by remediating compensating controls, without disrupting the...
CISA and FBI Issue Alert on Path Traversal Vulnerabilities – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rohan Timalsina The joint alert from CISA and FBI highlights the continued exploitation of path traversal vulnerabilities in critical infrastructure attacks, impacting...
Hardware Level Vulnerabilities, Revisited – Source: securityboulevard.com
Source: securityboulevard.com – Author: Joao Correia In August of last year, I examined several CPU bugs that posed serious security threats. The mitigations for these vulnerabilities...
HPE Aruba Vulnerabilities: Prevent Systems From RCE Attacks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Wajahat Raja Recently, HPE Aruba Networking, formerly known as Aruba Networks, has encountered significant security challenges. Vulnerabilities in their ArubaOS, the proprietary...
MY TAKE: RSAC 2024’s big takeaway: rules-based security is out; contextual security is taking over – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido KINGSTON, Wash. — U.S. Secretary of State Antony Blinken opened RSA Conference 2024 last week issuing a clarion call for the...
The Importance of Data Categorization In A Threat-Filled Landscape – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Dr. Pragyansmita Nayak, Chief Data Scientist, Hitachi Vantara Federal National security is amid a transformative journey driven by technological...
USENIX Security ’23 – Don’t be Dense: Efficient Keyword PIR for Sparse Databases – Distinguished Paper Award Winner – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX Security ’23 – Don’t be Dense: Efficient Keyword PIR for...