Source: www.csoonline.com – Author: The recent breaches of sovereign telecom networks in the United States, underscores how highly connected but fragmented public networks are increasingly vulnerable...
Author: CISO2CISO Editor 2
Cloud Access Security Broker – ein Kaufratgeber – Source: www.csoonline.com
Source: www.csoonline.com – Author: Bevor Sie in einen Cloud Access Security Broker investieren, sollten Sie diesen Artikel lesen. Lesen Sie, worauf es bei der Wahl eines...
Xiaomi Security Center Welcomes Security Research with HackerOne Partnership – Source:www.hackerone.com
Source: www.hackerone.com – Author: johnk. Please welcome the Xiaomi Security Center (MiSRC) to HackerOne! Xiaomi, one of the world’s largest consumer electronics manufacturers, is launching a...
Navigating HIPAA Compliance When Using Tracking Technologies on Websites – Source: securityboulevard.com
Source: securityboulevard.com – Author: mykola myroniuk Websites have become indispensable tools for healthcare organizations to connect with patients, streamline operations, and enhance service delivery. Modern websites...
Empower Your SOC Teams with Cloud-Native Security Solutions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Can Cloud-Native Security Be a Game-Changer for Your SOC Teams? In today’s complex digital landscape, organizations are increasingly challenged to...
Proactively Securing Machine Identities to Prevent Attacks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Why Should Proactive Security Management of Machine Identities Be a Priority? With the rise of digitalization across various sectors, organizations...
Empower Your Security with Cloud Compliance Innovations – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn As we continue to leverage cloud services for our businesses, one cannot ignore the escalating complexity of cybersecurity. Non-Human Identities...
Build Your Confidence in Secrets Sprawl Management – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Can You Truly Be Confident in Your Approach to Secrets Management? Cybersecurity is a crucial element in today’s digital landscape,...
DEF CON 32 – Fireside Chat – The Dark Tangent and National Cyber Director Harry Coker, Jr – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » DEF CON 32 – Fireside Chat – The Dark Tangent and...
Product Updates and Enhancements – Source:www.hackerone.com
Source: www.hackerone.com – Author: johnk. Please find below a list of Feature updates/releases that happened in our first quarter! You can find more details about each...
Beyond Encryption: Advancing Data-in-Use Protection – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team In the ever-evolving landscape of cryptography, traditional encryption methods safeguarding data at rest and in transit remain foundational to cybersecurity...
Hacking Dropbox Live in the Heart of Singapore at h1-65 – Source:www.hackerone.com
Source: www.hackerone.com – Author: johnk. HackerOne’s first live hacking event in Southeast Asia, h1-65, kicked off during Black Hat Asia in Singapore! As one of the...
Upcoming Speaking Events – Source: www.schneier.com
Source: www.schneier.com – Author: B. Schneier HomeBlog Upcoming Speaking Events This is a current list of where and when I am scheduled to speak: I’m speaking...
Innovating with Secure Secrets Rotation Techniques – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn With the rapid expansion of digitized environments, the demand for effective and secure identity management has surged. Organizations are increasingly...
Proactive Approaches to Identity and Access Management – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Why is Proactive Security Crucial in IAM? Have you ever weighed the impact of security breaches and data leaks on...
Navigating Cloud Security for Future Proofing Your Assets – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Why is Cloud Security Imperative for Asset Protection? As businesses increasingly migrate their operations to the cloud, the demand for...
Gaining Confidence Through Effective Secrets Vaulting – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Why is Secrets Vaulting Crucial in Today’s Cybersecurity Landscape? In a world increasingly dependent on cloud-based services, how do organizations...
DEF CON 32 – MobileMesh RF Network Exploitation Getting the Tea from goTenna – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Saturday, December 14, 2024 Home » Security Bloggers Network » DEF CON 32 – MobileMesh RF Network Exploitation Getting the...
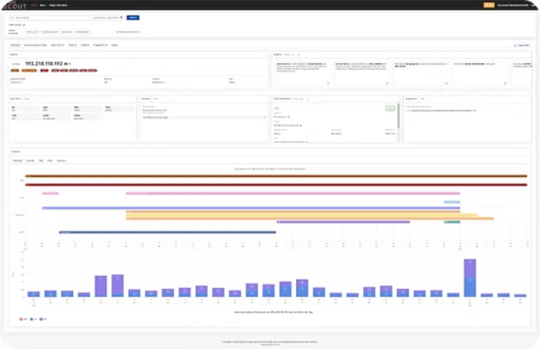
2024 Year in Review: Features and Improvements in Pure Signal™ Scout – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Monnier Team Cymru is excited to share our accomplishments in delivering new features and improvements in Pure Signal™ Scout. Thank you...
Feeling Reassured with Top-Tier API Security Measures – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Are You Maximizing Your API Security Measures? If you’re a CISO or a cybersecurity professional, you understand the importance of...
How Can Strong Secrets Management Prevent Data Breaches – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Is Your Secrets Management Strong Enough to Prevent Data Breaches? In an increasingly connected digital world, secrets management has emerged...
Scaling Your Cyber Defense with Advanced IAM Solutions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn How Crucial is the Role of Advanced IAM in Scaling Your Cyber Defense? With the rise in cyber threats, businesses...
Living in the Age of AI: Reflections from a Year at the Helm of Cybersecurity – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: When I joined Proofpoint a year ago, I was humbled by the opportunity to lead a company at the forefront of cybersecurity....
How Proofpoint Is Redefining Cyber Threat Defense – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: Proofpoint CEO Sumit Dhawan shares his vision for a safer digital future. getty When Sumit Dhawan stepped into the role of CEO...
The New Boardroom Mandate: Data Security As A Strategic Priority – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: Ravi Ithal, GVP and CTO, Proofpoint DSPM Group. Ravi was also a cofounder of Netskope. getty It will come as no surprise...
Benefits of Network Monitoring Systems – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Maintaining a resilient, secure, and efficient network infrastructure is more important than ever. Network monitoring systems, which encompass both hardware...
The HackerOne Top 10 Most Impactful and Rewarded Vulnerability Types – Source:www.hackerone.com
Source: www.hackerone.com – Author: HackerOne. HackerOne customers have received more than 120,000 (and counting!) valid security vulnerabilities across more than 1,400 programs of all sizes. Combined,...
Fake IT Workers Funneled Millions to North Korea, DOJ Says – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine The US Justice Department on Thursday announced indictments against 14 North Korean nationals for their involvement in a multi-year scheme...
Phishing: The Silent Precursor to Data Breaches – Source: www.securityweek.com
Source: www.securityweek.com – Author: Torsten George Phishing is one of the most prevalent tactics, techniques, and procedures (TTPs) in today’s cyber threat landscape. It often serves...
SAP systems increasingly targeted by cyber attackers – Source: www.csoonline.com
Source: www.csoonline.com – Author: News 13 Dec 20244 mins Black HatPayment SystemsSoftware Providers Long viewed as an opaque black box, attackers are increasingly focused upon hacking...