Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Source: Kristoffer Tripplaar via Alamy Stock Photo NEWS BRIEF Cisco has released a patch for a...
Author: CISO2CISO Editor 2
3 Use Cases for Third-Party API Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dionisio Zumerle Source: Elena Uve via Alamy Stock Photo COMMENTARY API security often involves third-party, rather than first-party, APIs, and each use...
Strengthening Our National Security in the AI Era – Source: www.darkreading.com
Source: www.darkreading.com – Author: Mike Arrowsmith Source: Vladimir Stanisic via Alamy Stock Photo COMMENTARY The federal government is often slow moving when it comes to various...
The Age of Unseen Truths And Deceptive Lies – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Julio Padilha Volkswagen | Audi South America January 24, 2025 From the moment we’re born, we are surrounded by a...
Tagged Files as a Road to Insider Threats – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Milica D. Djekic January 24, 2025 The insider threat is any individual within community who does something against such surrounding...
The Cybersecurity Vault Podcast 2024 Recap – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matthew Rosenquist My deepest appreciation to all the incredible cybersecurity luminaries who joined The Cybersecurity Vault podcast last year! Your insights, expertise,...
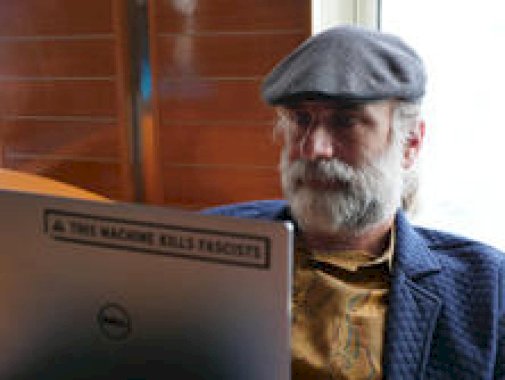
DEF CON 32 – Anyone Can Hack IoT- Beginner’s Guide To Hacking Your First IoT Device – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Home » Security Bloggers Network » DEF CON 32 – Anyone Can Hack IoT- Beginner’s Guide To Hacking Your First...
Cyber Lingo: What is GRC in cybersecurity? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ryan Healey-Ogden What is GRC in cybersecurity, and why does it matter? GRC stands for Governance, Risk, and Compliance, a helpful framework...
Randall Munroe’s XKCD ‘Unit Circle’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Friday, January 24, 2025 Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News...
Continuous Monitoring Guide: FedRAMP Meets Zero Trust – Source: securityboulevard.com
Source: securityboulevard.com – Author: Max Aulakh Security isn’t something you implement once and leave alone. It’s a mindset, an operation, and an ongoing policy. Security frameworks...
How to Choose the Right Cybersecurity Software: A Comprehensive Guide – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author Imagine walking into your office one morning to find that all your company’s data has...
How bots and fraudsters exploit video games with credential stuffing – Source: securityboulevard.com
Source: securityboulevard.com – Author: Sebastian Wallin If you spend time on video game forums, you might have noticed posts from users discussing their accounts being hacked...
Solving WAFs biggest challenge | Impart Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Impart Security Blog What’s the biggest challenge with WAF? It’s not a bypass. It’s all the operational details around getting a WAF operational in...
DEF CON 32 – Building A Secure Resilient Nationwide EV Charging Network – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Home » Security Bloggers Network » DEF CON 32 – Building A Secure Resilient Nationwide EV Charging Network Authors/Presenters: Harry...
Unveiling the Dark Web: Myths, Realities, and Risks You Didn’t Know About – Source: securityboulevard.com
Source: securityboulevard.com – Author: Devasmita Das The internet is vast. While most of us spend our days browsing the surface web—Facebook, Google, Instagram, Netflix—there’s another world lurking...
Subaru Starlink Vulnerability Exposed Cars to Remote Hacking – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A vulnerability in Subaru’s Starlink connected vehicle service provided unrestricted access to the accounts of customers in the US, Canada,...
North Korean Fake IT Workers More Aggressively Extorting Enterprises – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The individuals involved in North Korean fake IT worker schemes are extorting the organizations that employ them and are increasingly...
In Other News: VPN Supply Chain Attack, PayPal $2M Settlement, RAT Builder Hacks Script Kiddies – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News SecurityWeek’s cybersecurity news roundup provides a concise compilation of noteworthy stories that might have slipped under the radar. We provide...
US Charges Five People Over North Korean IT Worker Scheme – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The US Department of Justice on Thursday announced charges against five individuals for their involvement in a North Korean IT...
CISA Warns of Old jQuery Vulnerability Linked to Chinese APT – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The US cybersecurity agency CISA on Thursday added an old jQuery flaw tracked as CVE-2020-11023 to its Known Exploited Vulnerabilities...
Millions Impacted by PowerSchool Data Breach – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire School districts in the US and Canada say hackers stole all their historical data from a compromised PowerSchool service in...
Cyber Insights 2025: Social Engineering Gets AI Wings – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Cyber Insights 2025 examines expert opinions on the expected evolution of more than a dozen areas of cybersecurity interest over...
Hackers Earn $886,000 at Pwn2Own Automotive 2025 for Charger, OS, Infotainment Exploits – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The Pwn2Own Automotive 2025 hacking competition organized this week by Trend Micro’s Zero Day Initiative (ZDI) in Tokyo, Japan, has...
Friday Squid Blogging: Beaked Whales Feed on Squid – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier About Bruce Schneier I am a public-interest technologist, working at the intersection of security, technology, and people. I’ve been writing...
Be careful what you say about data leaks in Turkey, new law could mean prison for reporting hacks – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley The Turkish government is proposing a controversial new cybersecurity law that could make it a criminal act to report on...
CISOs rücken näher an den Vorstand – Source: www.csoonline.com
Source: www.csoonline.com – Author: Eine aktuelle Studie zeigt: Angesichts der zunehmenden Bedeutung von Cybersicherheit gewinnen CISOs immer mehr Einfluss im Vorstand. Ein gutes Verhältnis zwischen CISO...
SonicWall’s Secure Mobile Access appliance faces zero-day attacks – Source: www.csoonline.com
Source: www.csoonline.com – Author: The bug affectq the management interfaces of SMA1000 Secure Mobile Access appliances, allowing the execution of arbitrary OS commands. A critical bug...
Grohe AG von Ransomware-Attacke betroffen – Source: www.csoonline.com
Source: www.csoonline.com – Author: Die Cyber-Bande Ransomhub erpresst die Grohe AG mit gestohlenen Daten. Die Ransomware-Bande Ransomhub will 100 Gigabyte Daten von der Grohe AG erbeutet...
Tricking the bad guys: realism and robustness are crucial to deception operations – Source: www.csoonline.com
Source: www.csoonline.com – Author: The tactic of luring bad actors into digital traps goes beyond honeypots, requiring robust infrastructure and highly realistic lures to gather intelligence...
GDPR fines hit €1.2 billion in 2024 on 8.3% more breach reports – Source: www.csoonline.com
Source: www.csoonline.com – Author: Corporation violations of GDPR rules resulted in total fines of €1.2 billion in 2024, according to a report from international law firm...