Source: www.csoonline.com – Author: Attackers re-register abandoned AWS S3 buckets filled with malicious files that are executed by applications looking for these buckets. Code references to...
Author: CISO2CISO Editor 2
Cybersecurity M&A Roundup: 45 Deals Announced in January 2025 – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Forty-five cybersecurity-related merger and acquisition (M&A) deals were announced in January 2025. SecurityWeek tracked more than 400 M&A deals in...
Riot Raises $30 Million for Employee Cybersecurity Solution – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Employee-focused cyber-protection startup Riot this week announced raising $30 million in a Series B funding round that brings the total...
Abandoned Amazon S3 Buckets Enabled Attacks Against Governments, Big Firms – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Cybersecurity company WatchTowr has identified many abandoned Amazon S3 buckets that could have been leveraged by threat actors to deliver...
Russian Hackers Exploited 7-Zip Zero-Day Against Ukraine – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Russian threat groups have conducted cyberespionage campaigns against government entities in Ukraine exploiting a zero-day vulnerability in the 7-Zip archiver...
Chrome 133, Firefox 135 Patch High-Severity Vulnerabilities – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Google and Mozilla on Tuesday announced the rollout of updates for the Chrome and Firefox browsers that address multiple high-severity...
Webinar Today: Defenders on the Frontline – Incident Response and Threat Intel Under the Microscope – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News SecurityWeek will host the second session of the CISO Forum 2025 Outlook webinar series on Tuesday, February 5th at 1PM...
CISA Issues Exploitation Warning for .NET Vulnerability – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The US cybersecurity agency CISA on Tuesday added several flaws to its Known Exploited Vulnerabilities (KEV) catalog, including a .NET...
Zyxel Issues ‘No Patch’ Warning for Exploited Zero-Days – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Taiwanese networking equipment maker Zyxel on Tuesday advised that two exploited zero-days in multiple legacy DSL CPE products will not...
How to Add Fingerprint Authentication to Your Windows 11 Computer – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares If you’ve recently purchased or received a Windows 11 computer, one of the first things I recommend you do is...
Sophos Acquires Secureworks for $859 Million – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Fiona Jackson Sophos has completed its $859 million acquisition of managed cyber security services provider Secureworks in an all-cash transaction. It now...
U.K. Announces ‘World-First’ Cyber Code of Practice for Companies Developing AI – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Fiona Jackson The U.K. government has introduced its “world-first” AI Cyber Code of Practice for companies developing AI systems. The voluntary framework...
The Top 5 Cloud Security Risks: How Hacker-Powered Security Can Help – Source:www.hackerone.com
Source: www.hackerone.com – Author: jkanevsky@hackerone.com. Widespread digital transformation means increased cloud security risk. Learn how human intelligence—hacker-powered security—can help your organization defend against new attack vectors,...
Investors, Trump and the Illuminati: What the “Nigerian prince” scams became in 2024 – Source: securelist.com
Source: securelist.com – Author: Anna Lazaricheva Spam and phishing Spam and phishing 05 Feb 2025 minute read “Nigerian” spam is a collective term for messages designed...
Take my money: OCR crypto stealers in Google Play and App Store – Source: securelist.com
Source: securelist.com – Author: Dmitry Kalinin, Sergey Puzan In March 2023, researchers at ESET discovered malware implants embedded into various messaging app mods. Some of these...
Credential Theft Becomes Cybercriminals’ Favorite Target – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Source: Artur Marciniec via Alamy Stock Photo NEWS BRIEF After analyzing more than a million pieces...
Ferret Malware Added to ‘Contagious Interview’ Campaign – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Source: imageBROKER.com GmbH & Co. KG via Alamy Stock Photo NEWS BRIEF In a new patch...
Cybercriminals Court Traitorous Insiders via Ransom Notes – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Source: Mayam studio via Shutterstock Ransomware actors are utilizing a previously unseen tactic in their ransomware...
Chinese ‘Infrastructure Laundering’ Abuses AWS, Microsoft Cloud – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Aleksia via Alamy Stock Photo Researchers have linked the China-based Funnull content delivery network (CDN) to a...
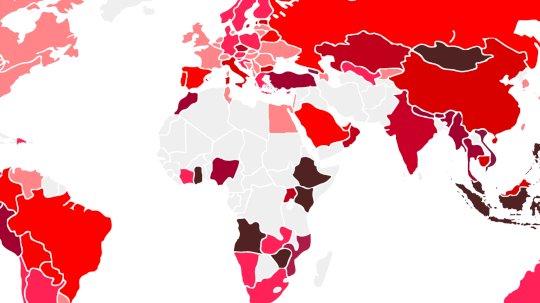
Nigeria Touts Cyber Success, Even as Cybercrime Rises in Africa – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Threat Index global mapSource: Check Point Software Technologies Nigeria’s government has taken a tougher stance against financial fraud...
Black Hat USA – Source: www.darkreading.com
Source: www.darkreading.com – Author: TechTarget and Informa Tech’s Digital Business Combine.TechTarget and Informa TechTarget and Informa Tech’s Digital Business Combine. Together, we power an unparalleled network...
Deepfakes and the 2024 US Election – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Interesting analysis: We analyzed every instance of AI use in elections collected by the WIRED AI Elections Project (source for...
How Imperva Infused AI Throughout Research and Development – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Holmes The Age of AI Is Upon Us The current pace of technological change beggars’ belief. Generative Artificial Intelligence (GenAI), released...
Secure by Design and Secure by Default: Why you need both for AppSec – Source: securityboulevard.com
Source: securityboulevard.com – Author: John P. Mello Jr. The relationship between the two software security initiatives promoted by the U.S. Cybersecurity and Infrastructure Security Agency (CISA)...
DEF CON 32 – Hacker Vs. AI Perspectives From An Ex-Spy – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Tuesday, February 4, 2025 Home » Security Bloggers Network » DEF CON 32 – Hacker Vs. AI Perspectives From An...
Cyberhaven: A Wake-Up Call for Consent Phishing Risks | Grip – Source: securityboulevard.com
Source: securityboulevard.com – Author: Grip Security Blog The Cyberhaven breach is more than just an isolated incident—it’s a wake-up call for organizations everywhere. Attackers targeted extension...
Randall Munroe’s XKCD ‘Stromatolites’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic humor & dry wit of Randall Munroe, creator of XKCD Permalink *** This is a Security Bloggers...
Survey Sees Organizations Being Overwhelmed by Remediation Challenges – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard A survey of 150 security decision makers in the U.S., published today, finds that close to two thirds of cybersecurity...
Anomalies are not Enough – Source: securityboulevard.com
Source: securityboulevard.com – Author: Evan Powell Mitre Att&ck as Context Introduction: A common theme of science fiction authors, and these days policymakers and think tanks, is how...
AttackIQ Bolsters Cyber Defenses with DeepSurface’s Risk-Analysis Tech – Source: securityboulevard.com
Source: securityboulevard.com – Author: George V. Hulme This week, AttackIQ acquired DeepSurface to broaden its vulnerability and attack path management capabilities to help enterprises identify and...