Source: www.techrepublic.com – Author: TechRepublic Academy Published March 6, 2025 We may earn from vendors via affiliate links or sponsorships. This might affect product placement on...
Author: CISO2CISO Editor 2
Trojans disguised as AI: Cybercriminals exploit DeepSeek’s popularity – Source: securelist.com
Source: securelist.com – Author: Vladislav Tushkanov, Vasily Kolesnikov, Oleg Kupreev, Denis Sitchikhin, Alexander Kryazhev Introduction Among the most significant events in the AI world in early...
Women Faced the Brunt of Cybersecurity Cutbacks in 2024 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have...
Enterprise AI Through a Data Security Lens: Balancing Productivity With Safety – Source: www.darkreading.com
Source: www.darkreading.com – Author: Adam Strange Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
CISA Cuts: A Dangerous Gamble in a Dangerous World – Source: www.darkreading.com
Source: www.darkreading.com – Author: Steve Durbin Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
Deepfake Videos of YouTube CEO Phish Creators – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have...
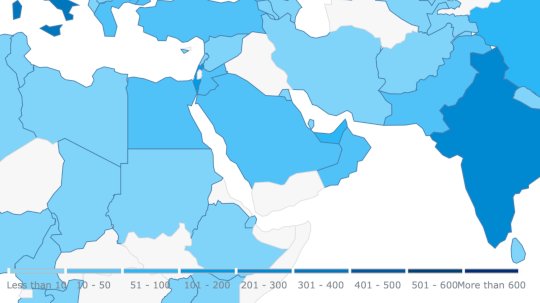
Ransomware Attacks Build Against Saudi Construction Firms – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...
Cybersecurity’s Future Is All About Governance, Not More Tools – Source: www.darkreading.com
Source: www.darkreading.com – Author: Shirley Salzman Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
Espionage Actor ‘Lotus Blossom’ Targets Southeast Asia – Source: www.darkreading.com
Source: www.darkreading.com – Author: Alexander Culafi, Senior News Writer, Dark Reading Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why...
Aryon Security Launches to Tackle Cloud Misconfigurations – Source: www.darkreading.com
Source: www.darkreading.com – Author: Arielle Waldman Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
Uncoder: Private Non-Agentic AI for Threat-Informed Detection Engineering – Source: socprime.com
Source: socprime.com – Author: Veronika Telychko SOC Prime is excited to announce a major upgrade to Uncoder AI—an industry-first integrated development environment (IDE) and co-pilot for...
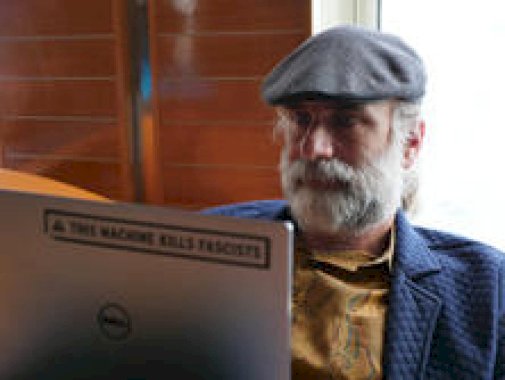
The Combined Cipher Machine – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier About Bruce Schneier I am a public-interest technologist, working at the intersection of security, technology, and people. I’ve been writing...
CISA Identifies Five New Vulnerabilities Currently Being Exploited – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments Bob • March 5, 2025 5:40 PM Don’t worry. We’ll gut CISA to the point of impotence, then...
US Indicts China’s iSoon ‘Hackers-for-Hire’ Operatives – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine The US Justice Department on Wednesday unsealed indictments charging employees of a Chinese cybersecurity firm known as i-Soon (Anxun Information...
Organizations Still Not Patching OT Due to Disruption Concerns: Survey – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Many organizations are still concerned that patching operational technology (OT) systems can lead to equipment downtime and operational disruptions, and...
SpecterOps Scores $75M Series B to Scale BloodHound Enterprise Platform – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine SpecterOps, a security startup selling technology to secure Microsoft’s Active Directory (AD) and Azure AD deployments, has raised an unusually...
China Hackers Behind US Treasury Breach Caught Targeting IT Supply Chain – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Microsoft threat hunters warned Wednesday of a significant shift in tactics by Silk Typhoon, a Chinese government espionage group linked...
Iranian Hackers Target UAE Firms With Polyglot Files – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Proofpoint warns of a highly targeted campaign targeting several United Arab Emirates organizations across multiple sectors with a new backdoor....
North Korean Fake IT Workers Pose as Blockchain Developers on GitHub – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A network of North Korean fake IT workers has been creating personas on GitHub to obtain remote engineering and full-stack...
Two Venezuelans Arrested in US for ATM Jackpotting – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The US Justice Department announced on Tuesday that two Venezuelan nationals were arrested and charged recently over their role in...
Ransomware Group Claims Attack on Tata Technologies – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A ransomware gang has claimed responsibility for an attack on Indian engineering firm Tata Technologies, threatening to leak 1.4 terabytes...
How Unified SSO reduces complexity and enhances security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Aldo Pietropaolo Large enterprises operate complex IT environments, balancing legacy on-premises applications with modern cloud services. Over time, they have accumulated multiple...
What are the latest trends in NHI protection for CIOs? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Are CIOs Prepared for the Rising NHI Trends? When the cloud environment evolves to deliver seamless business solutions, it brings...
What are the risks of unmanaged NHIs in enterprise environments? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Are Unmanaged Non-Human Identities (NHIs) Jeopardizing Your Enterprise Environment? With cloud-native applications, AI technologies, and IoT devices permeating modern enterprises,...
How can executive teams ensure NHI compliance with industry standards? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Why is Compliance Crucial for Non-Human Identities? Executive teams often face an array of complex challenges. One such challenge concerns...
Ransomware Attack Ends a 150 Year Company – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matthew Rosenquist Knights of Old, a 150-year-old UK company, is gone – due to a cyberattack! This terribly unfortunate event is a...
DEF CON 32 – War Stories – Stranger In A Changed Land – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » DEF CON 32 – War Stories – Stranger In A Changed...
Apple vs. UK — ADP E2EE Back Door Faceoff – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings End-to-end encryption battle continues, but Tim still Shtum. Apple has appealed against a United Kingdom government order to create a back door in...
Randall Munroe’s XKCD ‘RNA’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Wednesday, March 5, 2025 Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News...
Anti-detect browser analysis: How to detect the Undetectable browser? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Antoine Vastel This is the second article of our series about anti-detect browsers. In the first article, we gave an overview of...