Source: securityboulevard.com – Author: Aldo Pietropaolo In today’s digital economy, identity is more than just an authentication checkpoint—it’s the backbone of user access, security, and continuity....
Author: CISO2CISO Editor 2
Friday Squid Blogging: Japanese Divers Video Giant Squid – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments not important • May 9, 2025 6:37 PM Visit the Arctic vault holding back-ups of great works https://www.bbc.com/news/articles/c7vnyn17p57o...
160,000 Impacted by Valsoft Data Breach – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Canada-based vertical market software (VMS) firm Valsoft Corporation (dba AllTrust) is notifying over 160,000 people that their personal information was...
Malicious NPM Packages Target Cursor AI’s macOS Users – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Three malicious NPM packages posing as developer tools for the popular Cursor AI code editor were caught deploying a backdoor...
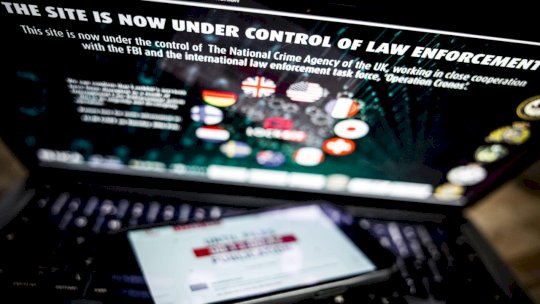
LockBit Ransomware Admin Panel Hacked, Leaks Reveal Inside Details – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Information that can be highly valuable to law enforcement and the cybersecurity community was leaked after someone hacked into an...
Rapid7 Launches Managed Detection & Response (MDR) for Enterprise – Source: www.darkreading.com
Source: www.darkreading.com – Author: Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This website is...
After Pahalgam Attack, Hacktivists Unite Under #OpIndia – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...
LockBit Ransomware Gang Hacked, Operations Data Leaked – Source: www.darkreading.com
Source: www.darkreading.com – Author: Rob Wright Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
Cyber Then & Now: Inside a 2-Decade Industry Evolution – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
Commvault: Vulnerability Patch Works as Intended – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...
Insight Partners Data Breach: Bigger Impact Than Anticipated – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have...
How Security Has Changed the Hacker Marketplace – Source: www.darkreading.com
Source: www.darkreading.com – Author: Isaac Evans Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
FBI warns that end of life devices are being actively targeted by threat actors – Source: www.csoonline.com
Source: www.csoonline.com – Author: Cybercriminals install malware on compromised devices, set up a botnet, and sell proxy services or launch coordinated attacks. The FBI is warning...
Cisco patches max-severity flaw allowing arbitrary command execution – Source: www.csoonline.com
Source: www.csoonline.com – Author: The bug can allow unauthorized, remote attackers to upload arbitrary files on devices running buggy IOS XE Software instances. Cisco (Nasdaq:CSCO) is...
Firewalls may soon need an upgrade as legacy tools fail at AI security – Source: www.csoonline.com
Source: www.csoonline.com – Author: Analysts suggest that we need to shift from traditional WAFs and API gateways to dedicated security controls for LLM and agentic AI...
DDoS-Attacken auf deutsche Städte – Source: www.csoonline.com
Source: www.csoonline.com – Author: In der vergangenen Woche waren mehrere deutsche Städte von Cyberattacken betroffen. Dahinter könnten prorussische Hacker stecken. Hacker haben die Webseiten von mehreren...
CVE funding crisis offers chance for vulnerability remediation rethink – Source: www.csoonline.com
Source: www.csoonline.com – Author: News Analysis May 9, 20256 mins Security PracticesThreat and Vulnerability Management Rising tide of vulnerabilities requires fresh approaches to risk mitigation. A...
Microsoft Listens to Security Concerns and Delays New OneDrive Sync – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matthew Rosenquist Misuse of the newly announced Microsoft OneDrive synchronization feature puts corporate security and personal privacy at serious risk in ways...
Feel Reassured with Advanced Secret Scanning – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alison Mack Are You Adequately Protecting Your Non-Human Identities? Where businesses increasingly turn to the cloud for their operations, one might wonder...
How Protected Are Your NHIs in Cloud Environments? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alison Mack Are Your Non-Human Identities Adequately Shielded in The Vast Cloud Space? Potentially, many organizations can underestimate the importance of managing...
Stay Confident with Robust Secrets Management – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alison Mack Are You Leaving Your Digital Doors Unlocked? Organizations are increasingly leaning on cloud-based solutions for convenience, scalability, and speed. However,...
OpenText Report Shines Spotlight on Malware Infection Rates – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard A 2025 cybersecurity threat report based on analysis of data collected from tens of millions of endpoints by OpenText shows...
BSidesLV24 – Proving Ground – CVSS v4 – A Better Version Of An Imperfect Solution – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – Proving Ground – CVSS v4 – A Better Version Of An Imperfect...
The 2025 State of Application Risk Report: Understanding AI Risk in Software Development – Source: securityboulevard.com
Source: securityboulevard.com – Author: Suzanne Ciccone Get details on the AI risks Legit unearthed in enterprises’ software factories. Artificial intelligence has rapidly become a double-edged sword...
The CMMC Rev 2 to Rev 3 Memo: What’s Changed? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Max Aulakh The world of cybersecurity is always changing, with rapid evolution in both threat and response creating a continual churn in...
Why You Should Segment RDP & SSH – Source: securityboulevard.com
Source: securityboulevard.com – Author: Peter Senescu Securing remote access pathways often feels like an endless battle against evolving threats. Attackers continually search for exposed protocols, especially...
ColorTokens + Nozomi Networks: A Partnership That’s Built for the Trenches of OT and IoT Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: ColorTokens Editorial Team We’re thrilled to officially announce our integration with Nozomi Networks, the recognized leader in OT and IoT cybersecurity. Get...
LockBit ransomware gang breached, secrets exposed – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley Oh dear, what a shame, never mind. Yes, it’s hard to feel too much sympathy when a group of cybercriminals...
Hackers hit deportation airline GlobalX, leak flight manifests, and leave an unsubtle message for “Donnie” Trump – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley GlobalX Airlines, a charter airline being used by the US government for deportation flights, has been attacked by hacktivists who...
Google Deploys On-Device AI to Thwart Scams on Chrome and Android – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: Google has begun integrating Gemini Nano, its on-device large language model (LLM), into the latest version of the Chrome browser to combat...