Source: thehackernews.com – Author: . May 23, 2023Ravie LakshmananCyber Threat / Malware The North Korean advanced persistent threat (APT) group known as Kimsuky has been observed...
Author: admin
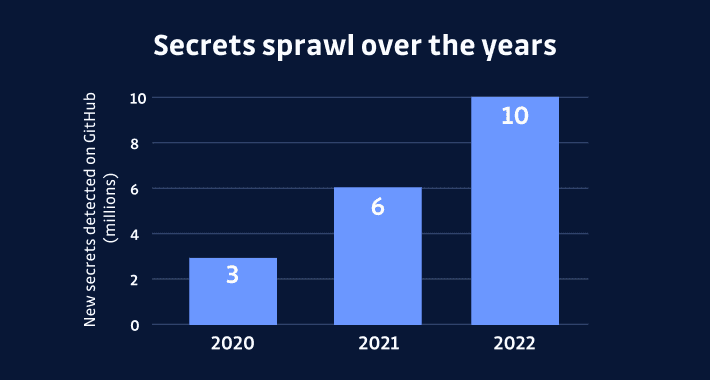
The Rising Threat of Secrets Sprawl and the Need for Action – Source:thehackernews.com
Source: thehackernews.com – Author: . The most precious asset in today’s information age is the secret safeguarded under lock and key. Regrettably, maintaining secrets has become...
New WinTapix.sys Malware Engages in Multi-Stage Attack Across Middle East – Source:thehackernews.com
Source: thehackernews.com – Author: . May 23, 2023Ravie LakshmananEndpoint Security/ Malware An unknown threat actor has been observed leveraging a malicious Windows kernel driver in attacks...
China Bans U.S. Chip Giant Micron, Citing “Serious Cybersecurity Problems” – Source:thehackernews.com
Source: thehackernews.com – Author: . May 23, 2023Ravie LakshmananNational Security / Hardware China has banned U.S. chip maker Micron from selling its products to Chinese companies...
E.U. Regulators Hit Meta with Record $1.3 Billion Fine for Data Transfer Violations – Source:thehackernews.com
Source: thehackernews.com – Author: . May 22, 2023Ravie LakshmananData Protection / Privacy Facebook’s parent company Meta has been fined a record $1.3 billion by European Union...
Indonesian Cybercriminals Exploit AWS for Profitable Crypto Mining Operations – Source:thehackernews.com
Source: thehackernews.com – Author: . May 22, 2023Ravie LakshmananCryptocurrency / Cloud Security A financially motivated threat actor of Indonesian origin has been observed leveraging Amazon Web...
The Ultimate Guide to CYBER THREAT Profiling by TIDAL CYBER
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
New Stealthy Bandit Stealer Targeting Web Browsers and Cryptocurrency Wallets – Source:thehackernews.com
Source: thehackernews.com – Author: . A new stealthy information stealer malware called Bandit Stealer has caught the attention of cybersecurity researchers for its ability to target...
Critical OAuth Vulnerability in Expo Framework Allows Account Hijacking – Source:thehackernews.com
Source: thehackernews.com – Author: . May 27, 2023Ravie LakshmananAPI Security / Vulnerability A critical security vulnerability has been disclosed in the Open Authorization (OAuth) implementation of...
Severe Flaw in Google Cloud’s Cloud SQL Service Exposed Confidential Data – Source:thehackernews.com
Source: thehackernews.com – Author: . May 26, 2023Ravie LakshmananData Safety / Cloud Security A new security flaw has been disclosed in the Google Cloud Platform’s (GCP)...
Predator Android Spyware: Researchers Uncover New Data Theft Capabilities – Source:thehackernews.com
Source: thehackernews.com – Author: . Security researchers have detailed the inner workings of the commercial Android spyware called Predator, which is marketed by the Israeli company...
5 Must-Know Facts about 5G Network Security and Its Cloud Benefits – Source:thehackernews.com
Source: thehackernews.com – Author: . 5G is a game changer for mobile connectivity, including mobile connectivity to the cloud. The technology provides high speed and low...
New COSMICENERGY Malware Exploits ICS Protocol to Sabotage Power Grids – Source:thehackernews.com
Source: thehackernews.com – Author: . May 26, 2023Ravie LakshmananICS/SCADA Security A new strain of malicious software that’s engineered to penetrate and disrupt critical systems in industrial...
Barracuda Warns of Zero-Day Exploited to Breach Email Security Gateway Appliances – Source:thehackernews.com
Source: thehackernews.com – Author: . May 26, 2023Ravie LakshmananEmail Security / Zero-Day Email protection and network security services provider Barracuda is warning users about a zero-day...
Dark Frost Botnet Launches Devastating DDoS Attacks on Gaming Industry – Source:thehackernews.com
Source: thehackernews.com – Author: . May 25, 2023Ravie LakshmananGaming / Server Security A new botnet called Dark Frost has been observed launching distributed denial-of-service (DDoS) attacks...
Zyxel Issues Critical Security Patches for Firewall and VPN Products – Source:thehackernews.com
Source: thehackernews.com – Author: . May 25, 2023Ravie LakshmananNetwork Security / Vulnerability Zyxel has released software updates to address two critical security flaws affecting select firewall...
Cynet Protects Hospital From Lethal Infection – Source:thehackernews.com
Source: thehackernews.com – Author: . May 25, 2023The Hacker NewsIncident Response A hospital with 2,000 employees in the E.U. deployed Cynet protections across its environment. The...
New PowerExchange Backdoor Used in Iranian Cyber Attack on UAE Government – Source:thehackernews.com
Source: thehackernews.com – Author: . May 25, 2023Ravie LakshmananEmail Security / Exploit An unnamed government entity associated with the United Arab Emirates (U.A.E.) was targeted by...
Alert: Brazilian Hackers Targeting Users of Over 30 Portuguese Banks – Source:thehackernews.com
Source: thehackernews.com – Author: . May 25, 2023Ravie LakshmananFinancial Security / Cyber Threat A Brazilian threat actor is targeting more than 30 Portuguese financial institutions with...
Webinar with Guest Forrester: Browser Security New Approaches – Source:thehackernews.com
Source: thehackernews.com – Author: . May 25, 2023The Hacker NewsBrowser Security / Tech In today’s digital landscape, browser security has become an increasingly pressing issue, making...
Buhti Ransomware Gang Switches Tactics, Utilizes Leaked LockBit and Babuk Code – Source:thehackernews.com
Source: thehackernews.com – Author: . May 25, 2023Ravie LakshmananEndpoint Security / Cyber Threat The threat actors behind the nascent Buhti ransomware have eschewed their custom payload...
China’s Stealthy Hackers Infiltrate U.S. and Guam Critical Infrastructure Undetected – Source:thehackernews.com
Source: thehackernews.com – Author: . May 25, 2023Ravie LakshmananCyber Threat / Espionage A stealthy China-based group managed to establish a persistent foothold into critical infrastructure organizations...
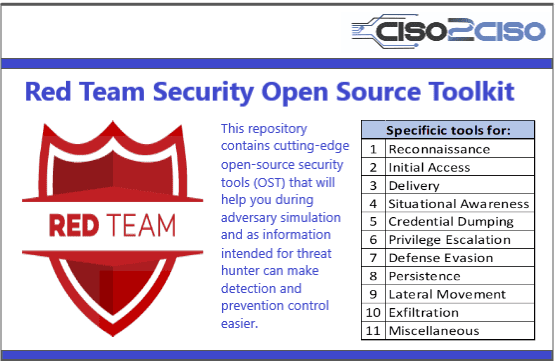
Red Team Security Open Source Toolkit
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Developer’s Guide to Mobile Authentication – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author Mobile app developers must ensure that the mobile app is effortless while protecting internal information....
2 Lenses for Examining the Safety of Open Source Software – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Open source repositories — such as Python’s PyPI, the Maven Java repository, and the Node Package...
Tesla Whistleblower Leaks 100GB of Data, Revealing Safety Complaints – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading German newspaper Handelsbatt reported today that it received 100GB of data from informants at Tesla, containing information...
Travel-Themed Phishing, BEC Campaigns Get Smarter as Summer Season Arrives – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer, Dark Reading As the summer holiday season draws near, phishing scams with travel-themed lures have been gaining momentum,...
Augmenting Your Microsoft 365 EOP and MDO Email Security Infrastructure – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: In today’s cloud-first approach to managing corporate infrastructure and running applications, more than 56% of global organizations use Microsoft for email. Whether...
From CEO Fraud to Vendor Fraud: The Shift to Financial Supply Chain Compromise – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Since its initial identification in 2013, business email compromise (BEC) has been dominated by executive impersonation. But over the past few years,...
CISO Guide to Business Email Compromise – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Business email compromise (BEC) is the most significant cybersecurity threat to enterprise organizations, with $2.7 billion lost in 2022 alone. This type...