Source: thehackernews.com – Author: . May 19, 2023Ravie LakshmananArtificial Intelligence / Cyber Threat Malicious Google Search ads for generative AI services like OpenAI ChatGPT and Midjourney...
Author: admin
WebKit Under Attack: Apple Issues Emergency Patches for 3 New Zero-Day Vulnerabilities – Source:thehackernews.com
Source: thehackernews.com – Author: . May 19, 2023Ravie LakshmananZero-Day / Endpoint Security Apple on Thursday rolled out security updates to iOS, iPadOS, macOS, tvOS, watchOS, and...
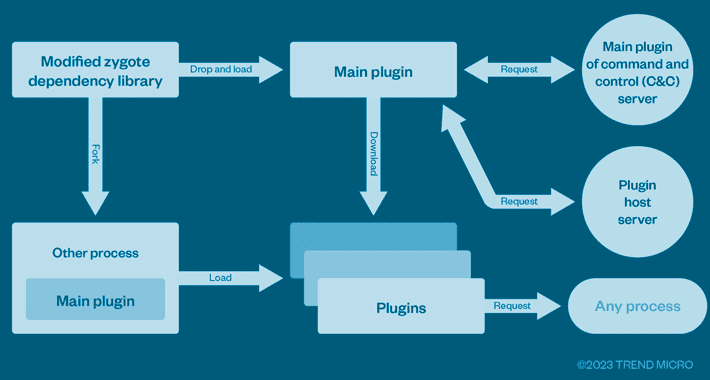
This Cybercrime Syndicate Pre-Infected Over 8.9 Million Android Phones Worldwide – Source:thehackernews.com
Source: thehackernews.com – Author: . A cybercrime enterprise known as Lemon Group is leveraging millions of pre-infected Android smartphones worldwide to carry out their malicious operations,...
Hackers hold city of Augusta hostage in a ransomware attack – Source: www.csoonline.com
Source: www.csoonline.com – Author: The ransomware group has released 10GB of sample data from the cyberattack on the US city of Augusta and claimed they have...
New phishing technique poses as a browser-based file archiver – Source: www.csoonline.com
Source: www.csoonline.com – Author: The new technique has a hacker simulate an archiving software in the web browser to trick the victim as he tries to...
Insider risk management: Where your program resides shapes its focus – Source: www.csoonline.com
Source: www.csoonline.com – Author: Choosing which department should be responsible for protecting an organization from threats from within isn’t always straightforward. There’s no getting around it,...
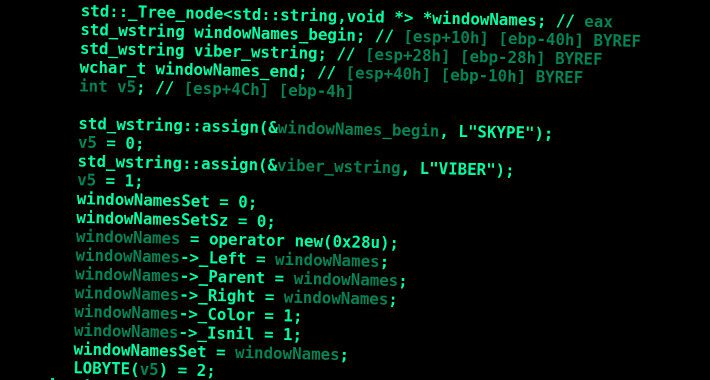
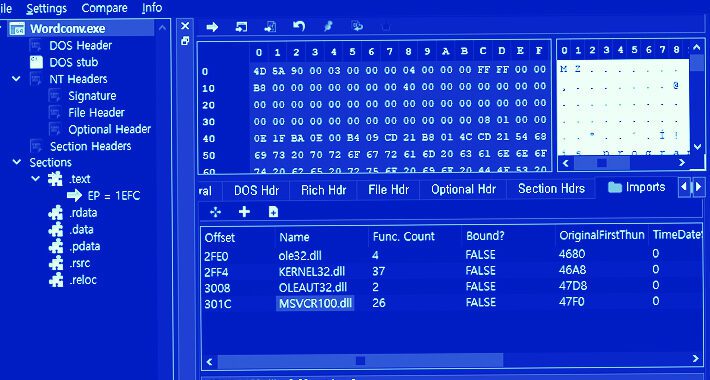
AceCryptor: Cybercriminals’ Powerful Weapon, Detected in 240K+ Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . May 29, 2023Ravie LakshmananCyber Threat / Malware A crypter (alternatively spelled cryptor) malware dubbed AceCryptor has been used to pack numerous...
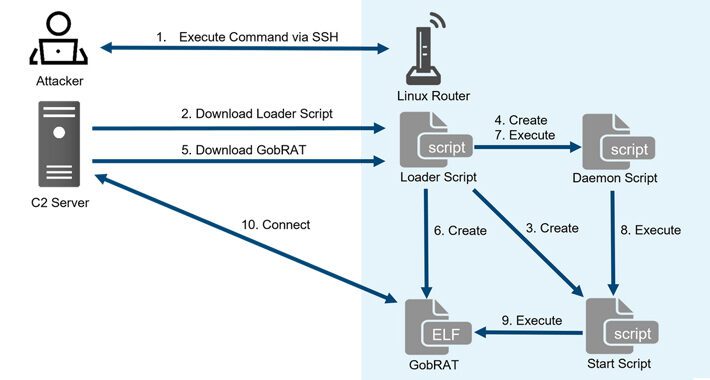
New GobRAT Remote Access Trojan Targeting Linux Routers in Japan – Source:thehackernews.com
Source: thehackernews.com – Author: . May 29, 2023Ravie LakshmananLinux / Network Security Linux routers in Japan are the target of a new Golang remote access trojan...
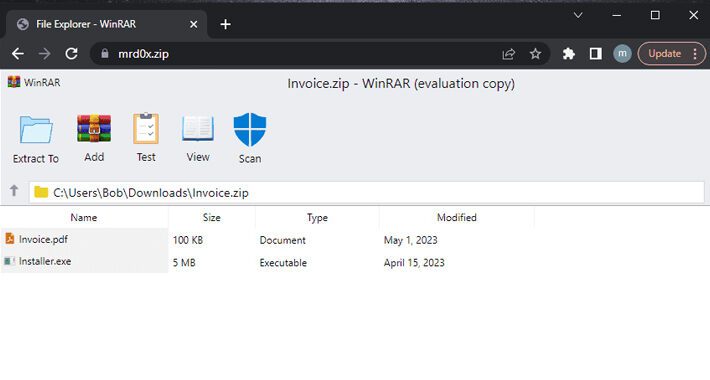
Don’t Click That ZIP File! Phishers Weaponizing .ZIP Domains to Trick Victims – Source:thehackernews.com
Source: thehackernews.com – Author: . A new phishing technique called “file archiver in the browser” can be leveraged to “emulate” a file archiver software in a...
PyPI Implements Mandatory Two-Factor Authentication for Project Owners – Source:thehackernews.com
Source: thehackernews.com – Author: . May 29, 2023Ravie LakshmananSupply Chain / Programming The Python Package Index (PyPI) announced last week that every account that maintains a...
Bad Magic’s Extended Reign in Cyber Espionage Goes Back Over a Decade – Source:thehackernews.com
Source: thehackernews.com – Author: . May 22, 2023Ravie LakshmananCyber Espionage / Malware New findings about a hacker group linked to cyber attacks targeting companies in the...
Are Your APIs Leaking Sensitive Data? – Source:thehackernews.com
Source: thehackernews.com – Author: . It’s no secret that data leaks have become a major concern for both citizens and institutions across the globe. They can...
U.K. Fraudster Behind iSpoof Scam Receives 13-Year Jail Term for Cyber Crimes – Source:thehackernews.com
Source: thehackernews.com – Author: . May 22, 2023Ravie LakshmananCyber Crime / Hacking A U.K. national responsible for his role as the administrator of the now-defunct iSpoof...
KeePass Exploit Allows Attackers to Recover Master Passwords from Memory – Source:thehackernews.com
Source: thehackernews.com – Author: . May 22, 2023Ravie LakshmananPassword Security / Exploit A proof-of-concept (PoC) has been made available for a security flaw impacting the KeePass...
PyPI Repository Under Attack: User Sign-Ups and Package Uploads Temporarily Halted – Source:thehackernews.com
Source: thehackernews.com – Author: . May 21, 2023Ravie LakshmananSoftware Security / Malware The maintainers of Python Package Index (PyPI), the official third-party software repository for the...
Meet ‘Jack’ from Romania! Mastermind Behind Golden Chickens Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . The identity of the second threat actor behind the Golden Chickens malware has been uncovered courtesy of a “fatal” operational security...
Notorious Cyber Gang FIN7 Returns With Cl0p Ransomware in New Wave of Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . May 20, 2023Ravie LakshmananCyber Crime / Ransomware The notorious cybercrime group known as FIN7 has been observed deploying Cl0p (aka Clop)...
Warning: Samsung Devices Under Attack! New Security Flaw Exposed – Source:thehackernews.com
Source: thehackernews.com – Author: . May 20, 2023Ravie LakshmananMobile Security / Cyber Attack The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has warned of active exploitation...
Privacy Sandbox Initiative: Google to Phase Out Third-Party Cookies Starting 2024 – Source:thehackernews.com
Source: thehackernews.com – Author: . May 19, 2023Ravie LakshmananOnline Privacy / Tech News Google has announced plans to officially flip the switch on its twice-delayed Privacy...
Dr. Active Directory vs. Mr. Exposed Attack Surface: Who’ll Win This Fight? – Source:thehackernews.com
Source: thehackernews.com – Author: . Active Directory (AD) is among the oldest pieces of software still used in the production environment and can be found in...
Threat Intelligence & Dark web Monitoring Tools
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Iranian Agrius Hackers Targeting Israeli Organizations with Moneybird Ransomware – Source:thehackernews.com
Source: thehackernews.com – Author: . May 25, 2023Ravie LakshmananRansomware / Endpoint Security The Iranian threat actor known as Agrius is leveraging a new ransomware strain called...
GUAC 0.1 Beta: Google’s Breakthrough Framework for Secure Software Supply Chains – Source:thehackernews.com
Source: thehackernews.com – Author: . May 25, 2023Ravie LakshmananSoftware Security / Supply Chain Google on Wednesday announced the 0.1 Beta version of GUAC (short for Graph...
Iranian Tortoiseshell Hackers Targeting Israeli Logistics Industry – Source:thehackernews.com
Source: thehackernews.com – Author: . May 24, 2023Ravie LakshmananCyber Threat / Web Security At least eight websites associated with shipping, logistics, and financial services companies in...
What to Look for When Selecting a Static Application Security Testing (SAST) Solution – Source:thehackernews.com
Source: thehackernews.com – Author: . If you’re involved in securing the applications your organization develops, there is no question that Static Application Security Testing (SAST) solutions...
Data Stealing Malware Discovered in Popular Android Screen Recorder App – Source:thehackernews.com
Source: thehackernews.com – Author: . May 24, 2023Ravie LakshmananMobile Security / Data Safety Google has removed a screen recording app named “iRecorder – Screen Recorder” from...
Legion Malware Upgraded to Target SSH Servers and AWS Credentials – Source:thehackernews.com
Source: thehackernews.com – Author: . May 24, 2023Ravie LakshmananServer Security / Malware An updated version of the commodity malware called Legion comes with expanded features to...
N. Korean Lazarus Group Targets Microsoft IIS Servers to Deploy Espionage Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . May 24, 2023Ravie LakshmananCyber Espionage / Server Security The infamous Lazarus Group actor has been targeting vulnerable versions of Microsoft Internet...
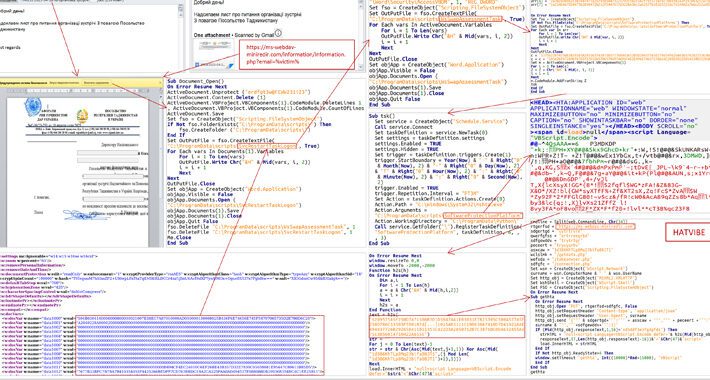
Cyber Attacks Strike Ukraine’s State Bodies in Espionage Operation – Source:thehackernews.com
Source: thehackernews.com – Author: . May 24, 2023Ravie LakshmananCyber War / Threat Intel The Computer Emergency Response Team of Ukraine (CERT-UA) has warned of cyber attacks...
GoldenJackal: New Threat Group Targeting Middle Eastern and South Asian Governments – Source:thehackernews.com
Source: thehackernews.com – Author: . May 23, 2023Ravie LakshmananCyber Threat / APT Government and diplomatic entities in the Middle East and South Asia are the target...