Source: thehackernews.com – Author: . May 31, 2023Ravie LakshmananData protection / Cyber Threat Improperly deactivated and abandoned Salesforce Sites and Communities (aka Experience Cloud) could pose...
Author: admin
Yet Another Toyota Cloud Data Breach Jeopardizes Thousands of Customers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Toyota Motor Corp. today announced its discovery of yet another data breach — this time, two misconfigured...
Can Cloud Services Encourage Better Login Security? Netflix’s Accidental Model – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading This month, Netflix stumbled backward into a policy that may have lasting security benefits for users....
MacOS ‘Migraine’ Bug: Big Headache for Device System Integrity – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading A newly revealed macOS vulnerability appropriately dubbed “Migraine” could allow a cyberattacker with root access to work...
Ways to Help Cybersecurity’s Essential Workers Avoid Burnout – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kris Lovejoy, Global Security and Resilience Practice Leader, Kyndryl Cybersecurity professionals make our world safer and more secure every day, shouldering responsibility...
Mirai Variant Opens Tenda, Zyxel Gear to RCE, DDoS – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A variant of the Mirai botnet is leveraging four different device vulnerabilities to add popular Linux-based servers and...
Focus Security Efforts on Choke Points, Not Visibility – Source: www.darkreading.com
Source: www.darkreading.com – Author: Menachem Shafran, Senior Vice President of Product and Innovation, XM Cyber There isn’t a security leader today who doesn’t worry about resources...
Microsoft Details Critical Apple macOS Vulnerability Allowing SIP Protection Bypass – Source:thehackernews.com
Source: thehackernews.com – Author: . May 31, 2023Ravie LakshmananEndpoint Security / Vulnerability Microsoft has shared details of a now-patched flaw in Apple macOS that could be...
6 Steps to Effective Threat Hunting: Safeguard Critical Assets and Fight Cybercrime – Source:thehackernews.com
Source: thehackernews.com – Author: . Finding threat actors before they find you is key to beefing up your cyber defenses. How to do that efficiently and...
Dark Pink APT Group Leverages TelePowerBot and KamiKakaBot in Sophisticated Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . May 31, 2023Ravie LakshmananAdvanced Persistent Threat The threat actor known as Dark Pink has been linked to five new attacks aimed...
RomCom RAT Using Deceptive Web of Rogue Software Sites for Covert Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . May 31, 2023Ravie LakshmananCyber Threat / Malware The threat actors behind RomCom RAT are leveraging a network of fake websites advertising...
Alert: Hackers Exploit Barracuda Email Security Gateway 0-Day Flaw for 7 Months – Source:thehackernews.com
Source: thehackernews.com – Author: . May 31, 2023Ravie LakshmananNetwork Security / Zero Day Enterprise security firm Barracuda on Tuesday disclosed that a recently patched zero-day flaw...
What is federated Identity? How it works and its importance to enterprise security – Source: www.csoonline.com
Source: www.csoonline.com – Author: Federated identity can be hugely beneficial for creating a solid user experience and better security, but it can be more costly and...
Phishing remained the top identity abuser in 2022: IDSA report – Source: www.csoonline.com
Source: www.csoonline.com – Author: The survey revealed phishing as the most common identity-related incident in 2022, with “emails” as the most popular type. Thinkstock Phishing was...
AI-automated malware campaigns coming soon, says Mikko Hyppönen – Source: www.csoonline.com
Source: www.csoonline.com – Author: The industry pioneer also expects cybersecurity to remain a growth business for years and sees Russian hacktivists as demoralizing European infosec teams....
Frontegg launches entitlements engine to streamline access authorization – Source: www.csoonline.com
Source: www.csoonline.com – Author: The new entitlement engine will be powered by context-aware logic controls (CALC) technology to effect context-based, fine-grained authorization controls.
Screen recording Android app found to be spying on users – Source: www.csoonline.com
Source: www.csoonline.com – Author: iRecorder was a legitimate app made available on Google Play Store in September 2021. A remote access trojan AhRat was most likely...
Spotlight on 2023 Dan Kaminsky Fellow: Dr. Gus Andrews – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ericka Chickowski, Contributing Writer, Dark Reading After an inaugural year of funding intensive work scaling the way security researchers report and automate...
Human-Assisted CAPTCHA-Cracking Services Supercharge Shopper Bots – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The cyber-underground menu of criminal services now includes on-demand, human-assisted CAPTCHA-breaking functionality, researchers are warning — meaning...
421M Spyware Apps Downloaded Through Google Play – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Spyware disguised as a marketing software development kit (SDK) has been spotted making its way to 101 Android...
Undetected Attacks Against Middle East Targets Conducted Since 2020 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Businesses in the Middle East faced a series of targeted attacks over the past few years,...
9M Dental Patients Affected by LockBit Attack on MCNA – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A US government-sponsored provider of dental healthcare is warning nearly 9 million clients that their sensitive and...
Pentagon Leaks Emphasize the Need for a Trusted Workforce – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kellie Roessler, Insider Risk Advocate & Author, DTEX Insider Intelligence & Investigations (i3) Team The leak of classified Pentagon documents through a...
Hackers Win $105,000 for Reporting Critical Security Flaws in Sonos One Speakers – Source:thehackernews.com
Source: thehackernews.com – Author: . May 30, 2023Ravie LakshmananZero Day / Vulnerability Multiple security flaws uncovered in Sonos One wireless speakers could be potentially exploited to...
CAPTCHA-Breaking Services with Human Solvers Helping Cybercriminals Defeat Security – Source:thehackernews.com
Source: thehackernews.com – Author: . May 30, 2023Ravie Lakshmanan Cybersecurity researchers are warning about CAPTCHA-breaking services that are being offered for sale to bypass systems designed...
Implementing Risk-Based Vulnerability Discovery and Remediation – Source:thehackernews.com
Source: thehackernews.com – Author: . In this day and age, vulnerabilities in software and systems pose a considerable danger to businesses, which is why it is...
Sneaky DogeRAT Trojan Poses as Popular Apps, Targets Indian Android Users – Source:thehackernews.com
Source: thehackernews.com – Author: . A new open source remote access trojan (RAT) called DogeRAT targets Android users primarily located in India as part of a...
Upskilling the non-technical: finding cyber certification and training for internal hires – Source: www.csoonline.com
Source: www.csoonline.com – Author: Andrey Popov / Shutterstock Finding qualified staff to replace vacancies or build out an expanding team can be a nightmare for already...
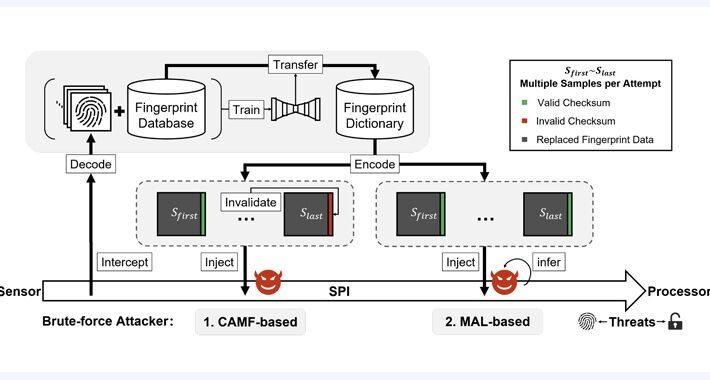
New BrutePrint Attack Lets Attackers Unlock Smartphones with Fingerprint Brute-Force – Source:thehackernews.com
Source: thehackernews.com – Author: . May 29, 2023Ravie LakshmananAuthentication / Mobile Security Researchers have discovered an inexpensive attack technique that could be leveraged to brute-force fingerprints...
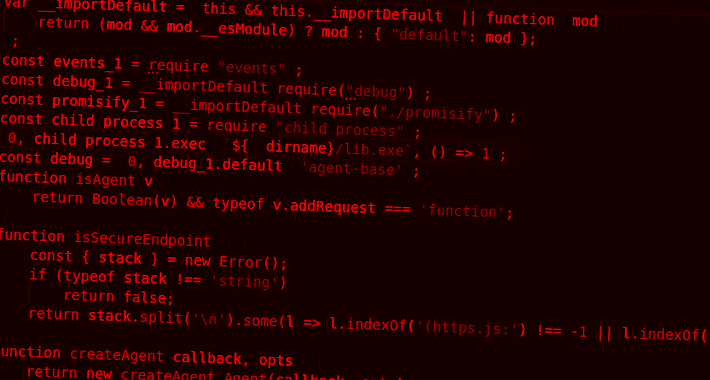
Developer Alert: NPM Packages for Node.js Hiding Dangerous TurkoRat Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Two malicious packages discovered in the npm package repository have been found to conceal an open source information stealer malware called...