Source: www.computerworld.com – Author: As generative AI revolutionizes tech, governments around the world are trying to come up with regulations that encourage its benefits while minimizing...
Author: admin
Federal cyber incidents reveal challenges of implementing US National Cybersecurity Strategy – Source: www.csoonline.com
Source: www.csoonline.com – Author: As federal government cybersecurity incidents continue to mount, the Biden administration’s National Cybersecurity Strategy should help, although experts say implementing it won’t...
10 notable critical infrastructure cybersecurity initiatives in 2023 – Source: www.csoonline.com
Source: www.csoonline.com – Author: How vendors, governments, industry bodies, and nonprofits are contributing to increasing the cyber resilience of critical national infrastructure this year. The security...
Security Recruiter Directory – Source: www.csoonline.com
Source: www.csoonline.com – Author: To find the right security job or hire the right candidate, you first need to find the right recruiter. Ready to get...
Top cybersecurity M&A deals for 2023 – Source: www.csoonline.com
Source: www.csoonline.com – Author: Shutterstock Uncertainty and instability marked the end of 2022 for many in the tech sector, a trend that bled into the beginning...
Microsoft: Lace Tempest Hackers Behind Active Exploitation of MOVEit Transfer App – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 05, 2023Ravie LakshmananZero Day / Cyber Attack Microsoft has officially linked the ongoing active exploitation of a critical flaw in...
The Annual Report: 2024 Plans and Priorities for SaaS Security – Source:thehackernews.com
Source: thehackernews.com – Author: . Over 55% of security executives report that they have experienced a SaaS security incident in the past two years — ranging...
Magento, WooCommerce, WordPress, and Shopify Exploited in Web Skimmer Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 05, 2023Ravie LakshmananWebsite Security / Magecart Cybersecurity researchers have unearthed a new ongoing Magecart-style web skimmer campaign that’s designed to...
Brazilian Cybercriminals Using LOLBaS and CMD Scripts to Drain Bank Accounts – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 05, 2023Ravie LakshmananBanking Security / Malware An unknown cybercrime threat actor has been observed targeting Spanish- and Portuguese-speaking victims to...
Alarming Surge in TrueBot Activity Revealed with New Delivery Vectors – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 05, 2023Ravie LakshmananMalware / Cyber Threat A surge in TrueBot activity was observed in May 2023, cybersecurity researchers disclosed. “TrueBot...
Why is Identity Security Awareness Becoming the Need of the Hour? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author Customer identity security is essential to running a business in the digital age. With an...
New Linux Ransomware Strain BlackSuit Shows Striking Similarities to Royal – Source:thehackernews.com
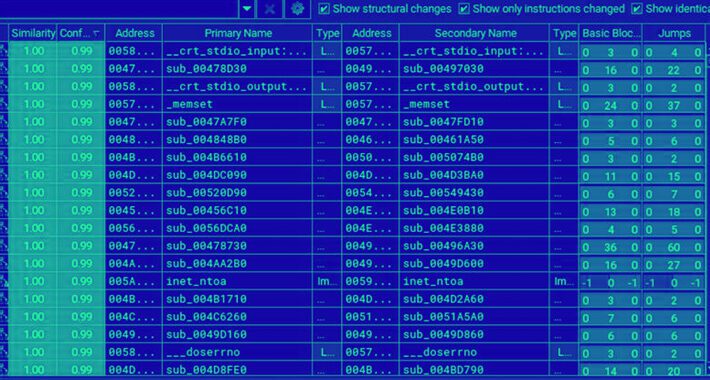
Source: thehackernews.com – Author: . Jun 03, 2023Ravie LakshmananEndpoint Security / Linux An analysis of the Linux variant of a new ransomware strain called BlackSuit has...
Cloud Security Tops Concerns for Cybersecurity Leaders: EC-Council’s Certified CISO Hall of Fame Report 2023 – Source:thehackernews.com
Source: thehackernews.com – Author: . A survey of global cybersecurity leaders through the 2023 Certified CISO Hall of Fame Report commissioned by the EC-Council identified 4...
FTC Slams Amazon with $30.8M Fine for Privacy Violations Involving Alexa and Ring – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 03, 2023Ravie LakshmananPrivacy / Technology The U.S. Federal Trade Commission (FTC) has fined Amazon a cumulative $30.8 million over a...
Russia points finger at US for iPhone exploit campaign that also hit Kaspersky Lab – Source: www.csoonline.com
Source: www.csoonline.com – Author: The Operation Triangulation surveillance campaign infects Apple iPhones without the need for user action and is difficult to detect. The Russian federal...
Attackers use Python compiled bytecode to evade detection – Source: www.csoonline.com
Source: www.csoonline.com – Author: Newly discovered campaign takes advantage of the fact that most vulnerability scanning tools don’t read compiled open-source software. Attackers who are targeting...
MOVEit Transfer vulnerability appears to be exploited widely – Source: www.csoonline.com
Source: www.csoonline.com – Author: A SQL injection vulnerability has been found in the MOVEit Transfer web application, allowing an unauthenticated attacker to gain unauthorized access to...
PyPI’s 2FA Requirements Don’t Go Far Enough, Researchers Say – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading The official open source code repository for the Python programming language, the Python Package Index...
‘PostalFurious’ SMS Attacks Target UAE Citizens for Data Theft – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Residents of the United Arab Emirates have been targeted by SMS campaigns that aim to steal payment and...
‘Picture-in-Picture’ Obfuscation Spoofs Delta, Kohl’s for Credential Harvesting – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer, Dark Reading Hackers are turning to obfuscation tactics relying on glossy advertising photos from Delta Airlines and retailer...
Streamers Ditch Netflix for Dark Web After Password Sharing Ban – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading From the outside, Netflix’s ban on password sharing may seem like a net positive for cybersecurity,...
Apple Zero-Days, iMessage Used in 4-Year, Ongoing Spying Effort – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading For at least the past four years, an advanced persistent threat (APT) actor has been covertly...
Biometric Bypass: BrutePrint Makes Short Work of Fingerprint Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Weaknesses in the biometric security architecture of Android phones could allow attackers to brute-force an encoded...
In search of the Triangulation: triangle_check utility – Source: securelist.com
Source: securelist.com – Author: Igor Kuznetsov, Valentin Pashkov, Leonid Bezvershenko, Georgy Kucherin Software Software 02 Jun 2023 minute read In our initial blogpost about “Operation Triangulation”,...
Checklist: Network and systems security – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Cybersecurity demands and the stakes of failing to properly secure systems and networks are high. While every organization’s specific security needs form...
Modern Applications Require Modern Application Security – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Application security is one of the most important components of an overall security program, yet some organizations struggle to identify and address...
New Botnet Malware ‘Horabot’ Targets Spanish-Speaking Users in Latin America – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 02, 2023Ravie LakshmananBotnet / Malware Spanish-speaking users in Latin America have been at the receiving end of a new botnet...
Camaro Dragon Strikes with New TinyNote Backdoor for Intelligence Gathering – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 02, 2023Ravie LakshmananMalware / Cyber Threat The Chinese nation-stage group known as Camaro Dragon has been linked to yet another...
North Korea’s Kimsuky Group Mimics Key Figures in Targeted Cyber Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 02, 2023Ravie LakshmananCyber Espionage / APT U.S. and South Korean intelligence agencies have issued a new alert warning of North...
MOVEit Transfer Under Attack: Zero-Day Vulnerability Actively Being Exploited – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 02, 2023Ravie Lakshmanan Zero-Day / Vulnerability A critical flaw in Progress Software’s in MOVEit Transfer managed file transfer application has...