Source: thehackernews.com – Author: . Jun 06, 2023Ravie LakshmananCryptocurrency / Cyber Threat A recent malware campaign has been found to leverage Satacom downloader as a conduit...
Author: admin
Over 60K Adware Apps Posing as Cracked Versions of Popular Apps Target Android Devices – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 06, 2023Ravie LakshmananMobile Security / Malvertising Thousands of adware apps for Android have been found to masquerade as cracks or...
Verizon DBIR: Social Engineering Breaches Double, Leading to Spiraling Ransomware Costs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading A full three-quarters of data breaches in the last year (74%) involved the human element,...
Researchers Spot a Different Kind of Magecart Card-Skimming Campaign – Source: www.darkreading.com
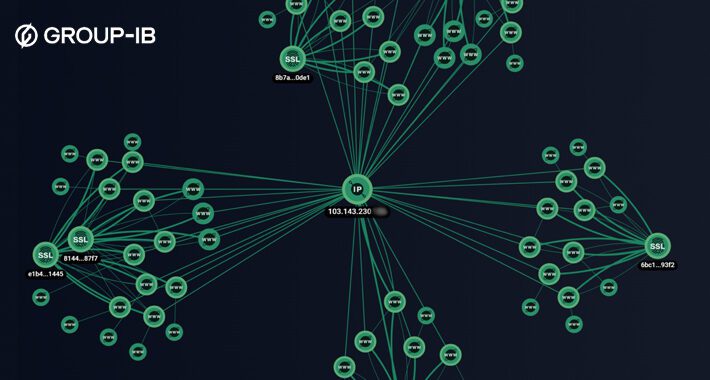
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading An attacker under the Magecart umbrella has infected an unknown number of e-commerce sites in the US,...
Microsoft Preps $425M Payment for LinkedIn GDPR Violations – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading In a disclosure released by Microsoft, the company announced that it will reserve $425 million to pay a...
US Aerospace Contractor Hacked With ‘PowerDrop’ Backdoor – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Hackers utilizing native Windows tools have managed to infect at least one US defense contractor with...
ChatGPT Hallucinations Open Developers to Supply Chain Malware Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Attackers can exploit ChatGPT’s penchant for returning false information to spread malicious code packages, researchers have found. This poses...
Only one in 10 CISOs today are board-ready, study says – Source: www.csoonline.com
Source: www.csoonline.com – Author: A report from cybersecurity firm IANS finds that more than half of public companies lack even one qualified director with cybersecurity expertise....
Lacework’s new CIEM uses ML to fish out high-risk identities – Source: www.csoonline.com
Source: www.csoonline.com – Author: The new CIEM will merge with existing threat detection capabilities to consolidate Lacework’s cloud security offering. Cloud security provider Lacework has released...
OWASP lists 10 most critical large language model vulnerabilities – Source: www.csoonline.com
Source: www.csoonline.com – Author: The list highlights the impact and prevalence of the 10 most critical vulnerabilities found in artificial intelligence applications based on LLMs. The...
Cloud misconfiguration causes massive data breach at Toyota Motor – Source: www.csoonline.com
Source: www.csoonline.com – Author: Vehicle data and customer information were exposed for over eight years due to a cloud misconfiguration at Toyota Motor that impacted over...
Department of Defense AI principles have a place in the CISO’s playbook – Source: www.csoonline.com
Source: www.csoonline.com – Author: Artificial intelligence has zoomed to the forefront of the public and professional discourse — as have expressions of fear that as AI...
Get to know CISO David Lindner | Code Patrol podcast | Contrast Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lisa Vaas, Senior Content Marketing Manager, Contrast Security There are multiple ways to cheat at ice fishing, Contrast Security CISO David Lindner...
5 Reasons Why IT Security Tools Don’t Work For OT – Source:thehackernews.com
Source: thehackernews.com – Author: . Attacks on critical infrastructure and other OT systems are on the rise as digital transformation and OT/IT convergence continue to accelerate....
Zero-Day Alert: Google Issues Patch for New Chrome Vulnerability – Update Now! – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 06, 2023Ravie LakshmananBrowser Security / Vulnerability Google on Monday released security updates to patch a high-severity flaw in its Chrome...
Cyclops Ransomware Gang Offers Go-Based Info Stealer to Cybercriminals – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 06, 2023Ravie LakshmananEndpoint Security / Data Security Threat actors associated with the Cyclops ransomware have been observed offering an information...
Chinese PostalFurious Gang Strikes UAE Users with Sneaky SMS Phishing Scheme – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 06, 2023Ravie Lakshmanan A Chinese-speaking phishing gang dubbed PostalFurious has been linked to a new SMS campaign that’s targeting users...
Zyxel Firewalls Under Attack! Urgent Patching Required – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 06, 2023Ravie LakshmananNetwork Security / Vulnerability The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday placed two recently disclosed...
Microsoft Links MOVEit Attack to Cl0p as British Airways, BBC Fall – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading As the names of the first known victims of the MOVEit zero-day exploitation started to roll...
2.5M Impacted by Enzo Biochem Data Leak After Ransomware Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading After facing a ransomware attack at the hands of hackers who breached its computer systems, Enzo Biochem...
Gigabyte Slams Backdoor Shut With Attack-Killing BIOS Update – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Gigabyte has released a BIOS update with increased security following the discovery of an inadvertent system backdoor...
Moonlighter Satellite Offers In-Orbit Target for Space Hackers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Satellite hacking is set to blast off to new frontiers when Moonlighter, billed as the “world’s first...
Don’t Overlook Twitter’s Trove of Threat Intel for Enterprise Cybersecurity – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Tagged, organized, and free for anyone who wants it, social media posts and data are an underused threat...
Mass Exploitation of Zero-Day Bug in MOVEit File Transfer Underway – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading A threat group with likely links to the financially motivated group known as FIN11 and other...
Name That Edge Toon: Spring Chickens – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist Hatch a witty cybersecurity-related caption to explain the scene above, and the most eggcellent (as deemed by our editors)...
Clop ransomware gang exploits the MOVEit Transfer vulnerability to steal data – Source: www.csoonline.com
Source: www.csoonline.com – Author: At least one organization, UK payroll provider Zellis, has confirmed a breach via the MOVEit utility. More information is coming to light...
BrandPost: How the combination of XDR and SIEM can improve SOC operations – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | When you have comprehensive security, the future is yours to build. Learn about the strategies and solutions to secure your...
Atomic Wallet hack leads to at least $35M in stolen crypto assets – Source: www.csoonline.com
Source: www.csoonline.com – Author: The biggest victim of the cryptocurrency hack on Atomic Wallet was an individual who reportedly lost $7.95 million in Tether. D. Keine...
SAFE Security claims to predict data breaches with new generative AI offering – Source: www.csoonline.com
Source: www.csoonline.com – Author: SAFE Security’s Cyber Risk Cloud of Clouds generates likelihoods for different risk scenarios based on an organization’s cybersecurity posture. AI-based cyber risk...
CISOs, IT lack confidence in executives’ cyber-defense knowledge – Source: www.csoonline.com
Source: www.csoonline.com – Author: Cybercriminals target senior executives, but IT security professionals say these executives are unprepared to defend their devices, software, and home network. By...