Source: thehackernews.com – Author: . Jun 10, 2023Ravie LakshmananCyber Attack / Malware Vietnamese public companies have been targeted as part of an ongoing campaign that deploys...
Author: admin
How to Manage Risks Associated with Identity and Access Management? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author A robust and effective Identity and Access Management (IAM) system is necessary to guarantee the...
Passkeys See Fresh Momentum With New Pilot Programs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jeffrey Schwartz, Contributing Writer, Dark Reading New product announcements are building momentum for passkeys — digital credentials that enable passwordless authentication using...
New Critical MOVEit Transfer SQL Injection Vulnerabilities Discovered – Patch Now! – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 10, 2023Ravie LakshmananVulnerability / Cyber Threat Progress Software, the company behind the MOVEit Transfer application, has released patches to address...
Google launches Secure AI Framework to help secure AI technology – Source: www.csoonline.com
Source: www.csoonline.com – Author: The SAIF is designed to help mitigate risks specific to AI systems like model theft, training data poisoning, and malicious injections. Google...
Network Perception wants to give more visibility into OT networks – Source: www.csoonline.com
Source: www.csoonline.com – Author: Operational technology visibility and compliance vendor Network Perception has upgraded its capabilities, adding faster and more detailed analysis of OT networks.
Microsoft Uncovers Banking AitM Phishing and BEC Attacks Targeting Financial Giants – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 09, 2023Ravie LakshmananCyber Threat / Financial Security Banking and financial services organizations are the targets of a new multi-stage adversary-in-the-middle...
Asylum Ambuscade: A Cybercrime Group with Espionage Ambitions – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 09, 2023Ravie LakshmananCybercrime / APT The threat actor known as Asylum Ambuscade has been observed straddling cybercrime and cyber espionage...
DOS Attacks Dominate, but System Intrusions Cause Most Pain – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Denial-of-service attacks continued to dominate the threat landscape in 2022, but breaches — those security incidents...
Brand-New Security Bugs Affect All MOVEit Transfer Versions – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Just days after Progress Software patched a widely exploited zero-day vulnerability in its MOVEit Transfer app,...
‘Asylum Ambuscade’ Cyberattackers Blend Financial Heists & Cyber Espionage – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Researchers have linked a series of financially motivated attacks and a group of advanced persistent...
Cl0P Gang Sat on Exploit for MOVEit Flaw for Nearly 2 Years – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Turns out the Cl0p ransomware group sat on a zero-day vulnerability it discovered in Progress Software’s...
South African Female Students Offered Cyber Scholarship – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading A scholarship is to be offered to women of color in South Africa, to enable them to...
How Continuous Monitoring and Threat Intel Can Help Prevent Ransomware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security, Microsoft Given the number of cybersecurity tools available on the market today, it’s easy for security leaders to become overwhelmed....
Cybersecurity Insights with Contrast CISO David Lindner | 6/9 – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Lindner, Director, Application Security Insight #1 ” Treat AI-generated code as inaccurate and insecure from the start and make sure it...
Cybersecurity startups to watch for in 2023 – Source: www.csoonline.com
Source: www.csoonline.com – Author: These startups are jumping in where most established security vendors have yet to go. Who_I_am / Getty Images The problems cybersecurity startups...
ACT government falls victim to Barracuda’s ESG vulnerability – Source: www.csoonline.com
Source: www.csoonline.com – Author: The ACT government revealed it is responding to a security breach in the e-mail gateway system provided by Barracuda with the potential...
North Korean APT group targets email credentials in social engineering campaign – Source: www.csoonline.com
Source: www.csoonline.com – Author: The Kimsuky group is adept at building relationships at target organizations to more easily deliver malware and steal credentials. Researchers warn of...
BrandPost: Make your employees your best asset in combating cybercrime – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | CISOs today face an expanding attack surface, increasingly threats, and a cybersecurity skills gap. An integrated and automated approach to...
BrandPost: Finding harmony with innovation, ChatGPT, and security – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | See why Zscaler’s proxy-based architecture is built on an industry-leading SSE framework to deliver superior security to secure today’s modern...
Stealth Soldier: A New Custom Backdoor Targets North Africa with Espionage Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 09, 2023Ravie LakshmananCyber Espionage / APT A new custom backdoor dubbed Stealth Soldier has been deployed as part of a...
City of Dallas Still Clawing Back Weeks After Cyber Incident – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading A month after the city of Dallas experienced a ransomware attack that took down major city services,...
Cybercrooks Scrape OpenAI API Keys to Pirate GPT-4 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Yesterday, moderators of the r/ChatGPT Discord channel banned a script kiddie who was freely sharing stolen...
Cybersecurity Institute to Open in Saudi Arabia – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading An institute branch of the Global Cybersecurity Forum is to be established in Saudi Arabia. As part...
Barracuda Warns All ESG Appliances Need Urgent Rip & Replace – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Despite pushing out patches addressing vulnerabilities in its Email Security Gateway (ESG) appliances in May, today Barracuda...
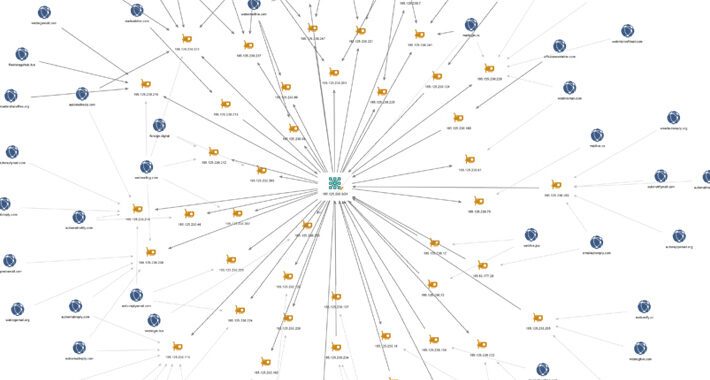
Sophisticated ‘Impulse Project’ Crypto Scam Sprawls With 1,000 Affiliate Sites – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Researchers have unraveled a web of more than a thousand scam websites that lead back to Russian-language...
Easily Exploitable Microsoft Visual Studio Bug Opens Developers to Takeover – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Security researchers are warning about a bug in Microsoft Visual Studio installer that gives cyberattackers a...
60K+ Android Apps Have Delivered Adware Undetected for Months – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading More than 60,000 malicious Android apps targeted global users worldwide for more than six months with adware...
Experts Unveil Exploit for Recent Windows Vulnerability Under Active Exploitation – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 08, 2023Ravie LakshmananEndpoint Security / Zero-Day Details have emerged about a now-patched actively exploited security flaw in Microsoft Windows that...
Clop Ransomware Gang Likely Aware of MOVEit Transfer Vulnerability Since 2021 – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 08, 2023Ravie LakshmananRansomware / Zero-Day The U.S. Cybersecurity and Infrastructure Security Agency (CISA) and Federal Bureau of Investigation (FBI) have...