Source: www.csoonline.com – Author: About | When you have comprehensive security, the future is yours to build. Learn about the strategies and solutions to secure your...
Author: admin
MOVEit Transfer developer patches more critical flaws after security audit – Source: www.csoonline.com
Source: www.csoonline.com – Author: A third-party audit reveals new MOVEit vulnerabilities, for which Progress Software has issued patches. The developer of the recently exploited MOVEit Transfer...
Okta aims to unify IAM for Windows, macOS devices in hybrid work environments – Source: www.csoonline.com
Source: www.csoonline.com – Author: Okta Device Access aims to simpllfy and unify identity and access management (IAM) for corporate devices within hybrid workforces with customizable multifactor...
AI and tech innovation, economic pressures increase identity attack surface – Source: www.csoonline.com
Source: www.csoonline.com – Author: Identity-centric security cracks are beginning to show in organizations as investment in digital and cloud technology outpaces cybersecurity spend. shutterstock Tension between...
Artificial intelligence is coming to Windows: Are your security policy settings ready? – Source: www.csoonline.com
Source: www.csoonline.com – Author: AI seems to be getting embedded in everything these days, and it’s coming to Microsoft Windows. It’s time now to ensure your...
Beware: New DoubleFinger Loader Targets Cryptocurrency Wallets with Stealer – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 13, 2023Ravie LakshmananCrimeware / Cryptocurrency A novel multi-stage loader called DoubleFinger has been observed delivering a cryptocurrency stealer dubbed GreetingGhoul...
Over Half of Security Leaders Lack Confidence in Protecting App Secrets, Study Reveals – Source:thehackernews.com
Source: thehackernews.com – Author: . It might come as a surprise, but secrets management has become the elephant in the AppSec room. While security vulnerabilities like...
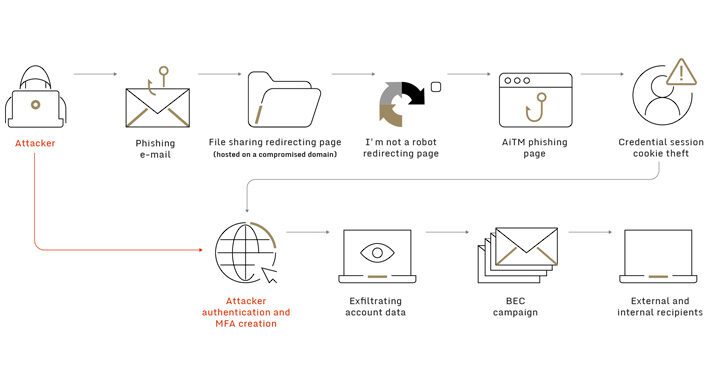
Adversary-in-the-Middle Attack Campaign Hits Dozens of Global Organizations – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 13, 2023Ravie LakshmananPhishing Attacks / BEC “Dozens” of organizations across the world have been targeted as part of a broad...
Researchers Report First Instance of Automated SaaS Ransomware Extortion – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading The 0mega ransomware group has successfully pulled off an extortion attack against a company’s SharePoint Online...
New Loader Delivering Spyware via Image Steals Cryptocurrency Info – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading A sophisticated attack by Russian-language actors is using a novel loader and malware-laced PNG image file...
Equipment reassignment checklist – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: © 2023 TechnologyAdvice. All Rights Reserved. Payment Information Address Line 1 Address Line 2 (Optional) Country Enter Promo Code (Optional) Your total...
Webinar – Mastering API Security: Understanding Your True Attack Surface – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 13, 2023The Hacker NewsAPI Security / Webinar Believe it or not, your attack surface is expanding faster than you realize....
Two Russian Nationals Charged for Masterminding Mt. Gox Crypto Exchange Hack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 13, 2023Ravie LakshmananCyber Crime / Cryptocurrency The U.S. Department of Justice (DoJ) has charged two Russian nationals in connection with...
Critical FortiOS and FortiProxy Vulnerability Likely Exploited – Patch Now! – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 13, 2023Ravie LakshmananNetwork Security / Vulnerability Fortinet on Monday disclosed that a newly patched critical flaw impacting FortiOS and FortiProxy...
Business email compromise scams take new dimension with multi-stage attacks – Source: www.csoonline.com
Source: www.csoonline.com – Author: A new attack group leverages trusted relationships between partner organizations to bypass multifactor authentication. In a campaign that exploits the relationships between...
To solve the cybersecurity worker gap, forget the job title and search for the skills you need – Source: www.csoonline.com
Source: www.csoonline.com – Author: CISOs who focus on identifying job candidates with the skills they need are finding talent from other fields and functions to help...
Cycode’s free CI/CD monitoring tool offers new DevOps visibility – Source: www.csoonline.com
Source: www.csoonline.com – Author: An eBPF-based tool for code monitoring provides new visibility into the software pipeline, aiming to forestall further SolarWinds- or Codecov-style attacks. Anterovium...
Threat intelligence programs poised for growth – Source: www.csoonline.com
Source: www.csoonline.com – Author: Enterprise organizations will increase spending, investing in areas like threat intelligence distribution, digital risk management, and security technology integration. Flamingo Images /...
BrandPost: Closing coverage gaps: exploring three cloud-centric security approaches – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | When you have comprehensive security, the future is yours to build. Learn about the strategies and solutions to secure your...
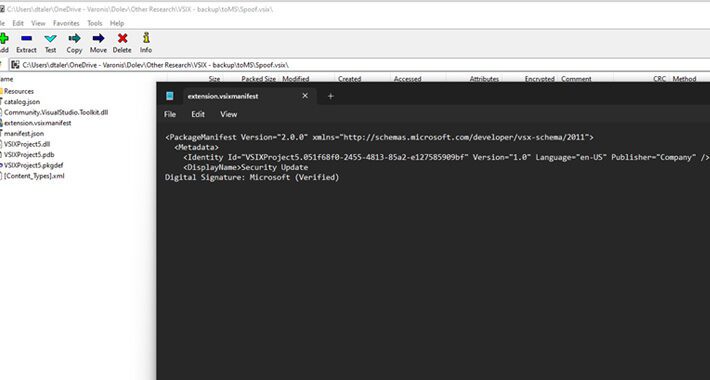
Researchers Uncover Publisher Spoofing Bug in Microsoft Visual Studio Installer – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 12, 2023Ravie LakshmananVulnerability / Software Security researchers have warned about an “easily exploitable” flaw in the Microsoft Visual Studio installer...
RomCom Threat Actor Targets Ukrainian Politicians, US Healthcare – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer, Dark Reading The threat actor known as RomCom has returned to the scene, targeting Ukrainian politicians and a...
10 Important Security Tasks You Shouldn’t Skip – Source: www.darkreading.com
Source: www.darkreading.com – Author: Joshua Goldfarb, Security and Fraud Architect, F5 Most of us have benefited from the mistakes of others. While this may sound like...
‘Stealth Soldier’ Attacks Target Libyan Government Entities With Surveillance Malware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading A wave of advanced persistent threat (APT) attacks aimed at Libyans has been detected, using malware that...
Supply Chain Attack Defense Demands Mature Threat Hunting – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading The headlines have become a steady occurrence … Kaseya, SolarWinds, 3CX, MOVEit, and there are sure to...
Doing Less With Less: Focusing on Value – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ben Johnson, Co-Founder and CTO, Obsidian Security The first half of this two-part article is here: “Cyber Essentialism & ‘Doing Less With...
Cybercriminals Using Powerful BatCloak Engine to Make Malware Fully Undetectable – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 12, 2023Ravie LakshmananEndpoint Security / Malware A fully undetectable (FUD) malware obfuscation engine named BatCloak is being used to deploy...
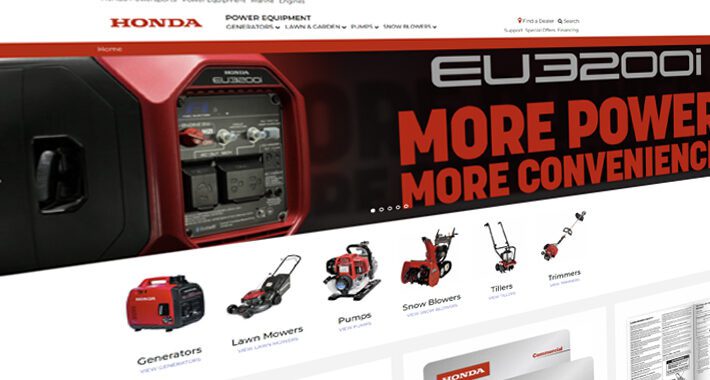
Password Reset Hack Exposed in Honda’s E-Commerce Platform, Dealers Data at Risk – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 12, 2023Ravie LakshmananData Safety / Hacking Security vulnerabilities discovered in Honda’s e-commerce platform could have been exploited to gain unrestricted...
Beware: 1,000+ Fake Cryptocurrency Sites Trap Users in Bogus Rewards Scheme – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 12, 2023Ravie LakshmananCryptocurrency / A previously undetected cryptocurrency scam has leveraged a constellation of over 1,000 fraudulent websites to ensnare...
Critical RCE Flaw Discovered in Fortinet FortiGate Firewalls – Patch Now! – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 12, 2023Ravie LakshmananVulnerability / Network Security Fortinet has released patches to address a critical security flaw in its FortiGate firewalls...
Apple’s Safari Private Browsing Now Automatically Removes Tracking Parameters in URLs – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 12, 2023Ravie LakshmananPrivacy / Tech News Apple is introducing major updates to Safari Private Browsing, offering users better protections against...