Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading A new threat group is leveraging a relatively large network of malicious servers to distribute and...
Author: admin
HD Moore’s Discovery Journey – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ericka Chickowski, Contributing Writer, Dark Reading For as long as he can remember it, HD Moore has loved discovering unexplored connections between...
Identity Theft Protection Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Help protect your employees and customers from identity theft. This policy from TechRepublic Premium outlines precautions for reducing risk, signs to watch...
Quick Glossary: Malware – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Malware is an insidious infection that will steal productivity from your enterprise and potentially wreak havoc on your network. To prevent and...
New ZenRAT Malware Targeting Windows Users via Fake Password Manager Software – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 27, 2023THNMalware / Cyber Threat A new malware strain called ZenRAT has emerged in the wild that’s distributed via bogus...
Critical libwebp Vulnerability Under Active Exploitation – Gets Maximum CVSS Score – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 27, 2023THNZero Day / Vulnerability Google has assigned a new CVE identifier for a critical security flaw in the libwebp...
Microsoft is Rolling out Support for Passkeys in Windows 11 – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 26, 2023THNEndpoint Security / Password Microsoft is officially rolling out support for passkeys in Windows 11 today as part of...
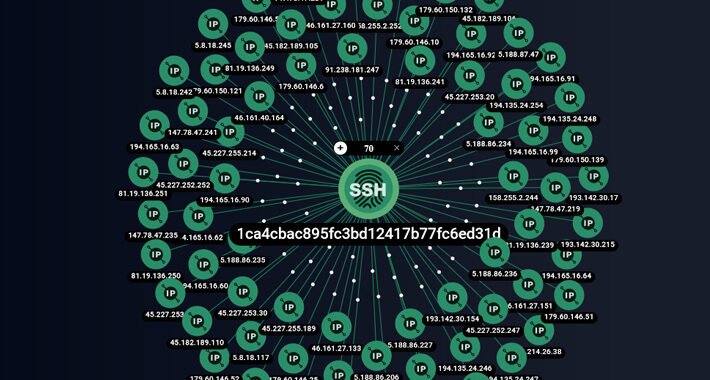
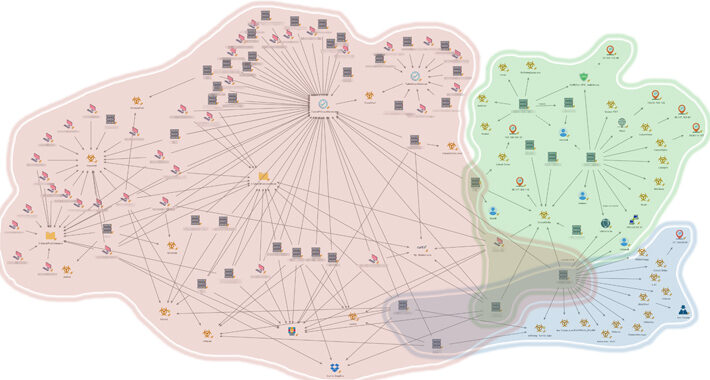
ShadowSyndicate: A New Cybercrime Group Linked to 7 Ransomware Families – Source:thehackernews.com
Source: thehackernews.com – Author: . Cybersecurity experts have shed light on a new cybercrime group known as ShadowSyndicate (formerly Infra Storm) that may have leveraged as...
Essential Guide to Cybersecurity Compliance – Source:thehackernews.com
Source: thehackernews.com – Author: . SOC 2, ISO, HIPAA, Cyber Essentials – all the security frameworks and certifications today are an acronym soup that can make...
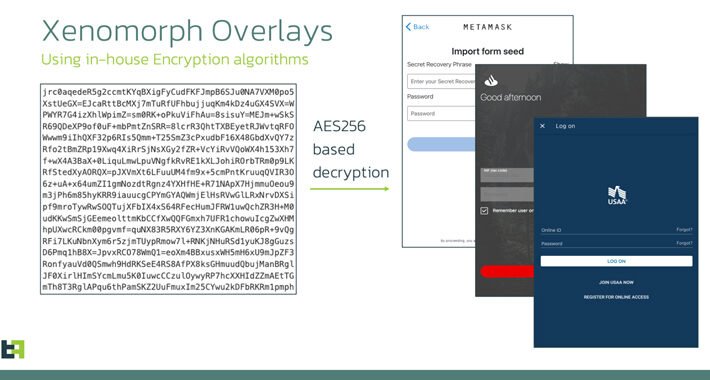
Xenomorph Banking Trojan: A New Variant Targeting 35+ U.S. Financial Institutions – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 26, 2023THNMobile Security / Malware An updated version of an Android banking trojan called Xenomorph has set its sights on...
Threat Report: The High Tech Industry Targeted the Most with 46% of NLX-Tagged Attack Traffic – Source:thehackernews.com
Source: thehackernews.com – Author: . How To Use This Report Enhance situational awareness of techniques used by threat actors Identify potential attacks targeting your industry Gain...
Chad Taps Huawei for Digital Modernization Project – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Chinese technology manufacturer Huawei has signed an agreement with Chad to build a national data center and technology...
Amidst MGM, Caesar’s Incidents, Attackers Focus on Luxury Hotels – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Even as the effects of the show-stopping cyberattacks on MGM Grand and Caesars are still being felt,...
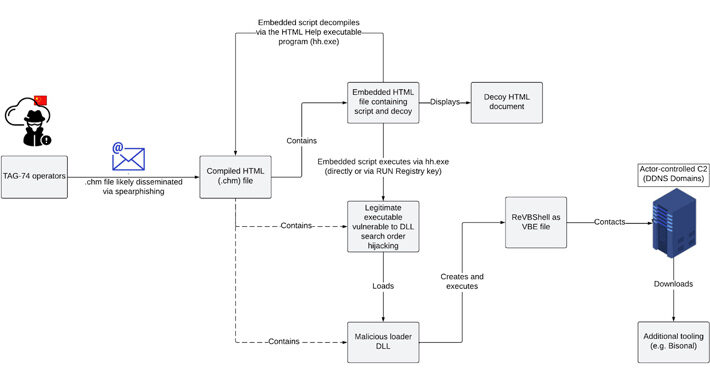
Chinese Hackers TAG-74 Targets South Korean Organizations in a Multi-Year Campaign – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 26, 2023THNCyber Espionage / Malware A “multi-year” Chinese state-sponsored cyber espionage campaign has been observed targeting South Korean academic, political,...
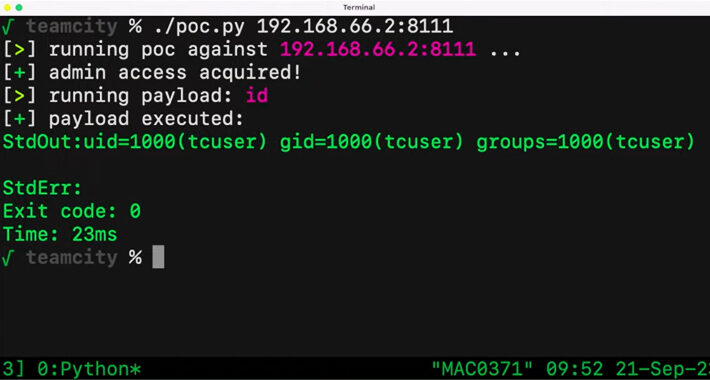
Critical JetBrains TeamCity Flaw Could Expose Source Code and Build Pipelines to Attackers – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 26, 2023THNVulnerability / Source Code A critical security vulnerability in the JetBrains TeamCity continuous integration and continuous deployment (CI/CD) software...
Takeaways for Businesses in the Rapidly Evolving Data Security and Privacy Landscape – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author As more and more businesses jump into the digital transformation bandwagon by leveraging cutting-edge tools...
When It Comes to Email Security, The Cloud You Pick Matters – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Businesses using Google Workspace are only half as likely to suffer a reportable cyberattack compared to...
Xenomorph Android Malware Targets Customers of 30 US Banks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading The cybercriminals behind a sophisticated Android banking Trojan called Xenomorph, who have been actively targeting users...
MOVEit Flaw Leads to 900 University Data Breaches – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading National Student Clearinghouse, a nonprofit that provides enrollment and other services for thousands of colleges and universities...
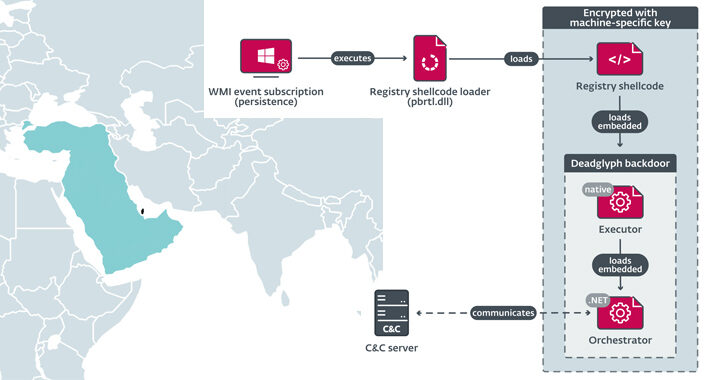
UAE-Linked ‘Stealth Falcon’ APT Mimics Microsoft in Homoglyph Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Researchers have recently discovered a sophisticated backdoor with unusual architecture, dubbed “Deadglyph,” used in a cyber-espionage attack...
Cyber Hygiene: A First Line of Defense Against Evolving Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security, Microsoft Basic security hygiene is more impactful than you may realize. While industry headlines are often dominated by emerging tech...
Ukrainian Military Targeted in Phishing Campaign Leveraging Drone Manuals – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 25, 2023THNCyber Attack / Phishing Ukrainian military entities are the target of a phishing campaign that leverages drone manuals as...
Are You Willing to Pay the High Cost of Compromised Credentials? – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 25, 2023The Hacker NewsPassword Security / Cybersecurity Weak password policies leave organizations vulnerable to attacks. But are the standard password...
Internet and Email Usage Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: This policy from TechRepublic Premium sets forth guidelines for the use of the internet, as well as internet-powered communication services, including email,...
Point of Sale Security Guide and Checklist – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: For retail businesses, the POS system is arguably their most important IT system. This TechRepublic Premium guide, and the accompanying checklist, will...
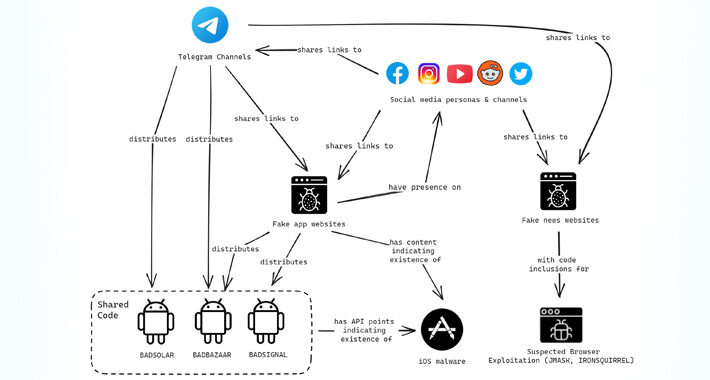
From Watering Hole to Spyware: EvilBamboo Targets Tibetans, Uyghurs, and Taiwanese – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 25, 2023THNSpyware / Cyber Espionage Tibetan, Uyghur, and Taiwanese individuals and organizations are the targets of a persistent campaign orchestrated...
New Report Uncovers 3 Distinct Clusters of China-Nexus Attacks on Southeast Asian Government – Source:thehackernews.com
Source: thehackernews.com – Author: . An unnamed Southeast Asian government has been targeted by multiple China-nexus threat actors as part of espionage campaigns targeting the region...
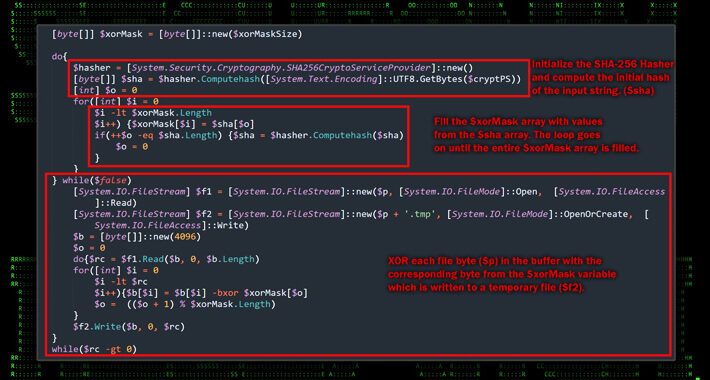
Deadglyph: New Advanced Backdoor with Distinctive Malware Tactics – Source:thehackernews.com
Source: thehackernews.com – Author: . Cybersecurity researchers have discovered a previously undocumented advanced backdoor dubbed Deadglyph employed by a threat actor known as Stealth Falcon as...
MGM, Caesars Cyberattack Responses Required Brutal Choices – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Twin cyberattacks on MGM Resorts and Caesars Entertainment have provided a singular view into what happens when...
Bot Swarm: Attacks From Middle East & Africa Are Notably Up – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading The number of reported bot attacks originating from the Middle East and Africa increased over the...