The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Author: admin
5G Cybersecurity by Dell
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
DOSfuscation – Exploring the Depths of Cmd.exe Obfuscation and Detection Techniques by FireEye
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Threat Intel – Threat Intelligence JSSLoader – the shellcode edition
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CISO2CISO Toolbox Series – Cyber Security Blogs / Cyber Security RSS Feeds List –
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
How to Stop Business – Email Compromise Threats – Advanced techniques for fighting financial phishing fraud by CloudFlare
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
How Much 10 Companies Paid Their Virtual CISO Service in 2022 Benchmark by Nathaniel Cole
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Using MITRE ATT&CK IN THREAT HUNTING AND DETECTION BY LogRhythm
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Coming AI Hackers – Council for the responsible use of AI by Bruce Schneier
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SANS DFIR – CHEAT SHEETS & NOTEBOOKS – The most complete reference !!!
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Turning a Cybersecurity Strategy Into Reality A Holistic Performance Management Framework by BCG & STC
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
List Of Top Penetration Testing Tools by Hacker Combat.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Digest of Cyber Organized Crime by UNODC – United Nations Office on Drugs and Crime
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ChatGPT for Cybersecurity by Joas Antonio dos Santos – malwareanalysis #reverseengineering
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity Risk Report 2023 by RiskLens
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ChatGPT Security Risks -A Guide for Cyber Security Professionals by Cybertalk.org
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Undestanding Networks Hacks – Attack and Defense with Python 2nd Edition by Bastian Ballman – Springer
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Blue Team Perspective & Red Team Tools by Black Hills Information Security – BHinfoSecurity
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Awesome OSINT(Open-Source Intelligence) – Best curated list of amazingly awesome open source intelligence tools and resources.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Best vendor agnostic SIEM for SOCs solution implementation guide by Info-Tech Research Group
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2022 Global Chief Information Security Officer (CISO) Survey by HEIDRICK & STRUGGLES – SPECIALITY PRACTICES TECHNOLOGY OFFICERS PRACTICE
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
OWASP Testing Guide 4.0 by Matteo Meucci and Andrew Muller
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Most Complete RED TEAM & PENTEST Reference and Resources Guide by @ANHKWAR
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SNORT Rule Writing Guide by Pouyan Zamani
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Operations Center Guidebook – A Practical Guide for a Successful SOC
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
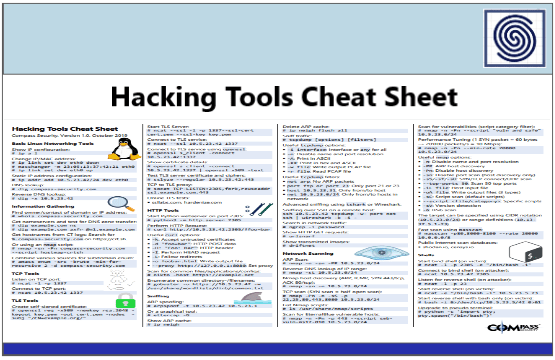
Hacking Tools Cheat Sheet by Compass Security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ENISA THREAT LANDSCAPE FOR RANSOMWARE ATTACK REPORT JULY 2022
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
State of Kubernetes Security Report 2022 by RedHat
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Advancing Supply Chain Security in Oil and Gas an Industry Analysis by World Economic Forum
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
TELECOM SECURITY INCIDENTS REPORT 2021 BY ENISA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...