Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading North Korean state hackers have debuted a fresh Mac malware targeting users in the US and...
Author: admin
Azure Defenses for Ransomware Attack by Microsoft Security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Ransomware, extorsion and the cyber crime ecosystem by NCSC & NCA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Risk Mitigation , Prevention and Cutting the Kill Chain – Minimize the impact of ransomware with Akamai Guardicore Segmentation
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Countering Ransomware Financing – FATF Report March 2023
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ISACA Ransomware Incident Management Quick Reference Guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Ransomware Diaries – Volume 2 – A Ransomware Hacker Origin Story by Jon DiMaggio
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Why do we compare a SOC (Security Operations Center) with the cockpit of a commercial airplane? by Marcos Jaimovich
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Operations Center (SOC) – Tools for Operations Development by Joas Antonio
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
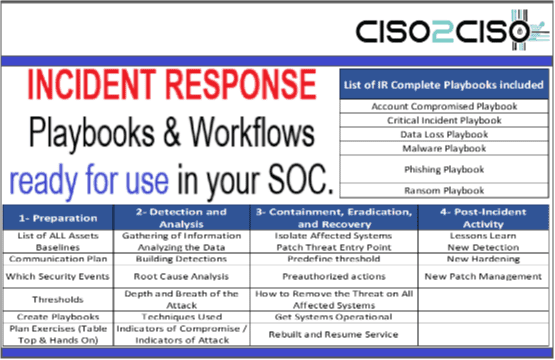
Incident Response Playbooks & Workflows Ready for use in your SOC & Redteams
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
396 Use Cases & Siem Rules Code ready for use for Mitre Attacks Events Detection in Your SOC by Logpoint
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Global Risks Report 2023 – Insight Report – 18th Edition by World Economic Forum (WEF). Economics, Environmental, Geopolitical, Societal, Technological & Cyber Risks Included in the report.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Orange Cyberdefense Security Navigator 2023 – Research-driven insights to build a safer digital society
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Adapt Or Die: XDR Is On A Collision Course With SIEM And SOAR – EDR Is Dead, Long Live XDR by Allie Mellen – Forrester
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
How to Avoid Party Chaos with the Right Application-Layer DDoS Platform whitepaper by Akamai
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A Practical Guide for OSINT Investigators to Combat Disinformation and Fake Reviews Driven by AI (ChatGPT) by ShadowDragon
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Advancing Cyber Resilience Principles and Tools for Boards by World Economic Forum (WEF)
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Global Threat Intelligence Report – Delivering Actionable and Contextualized Intel to Increase Cyber Resilience by BlackBerry Cybersecurity.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
What is Cyber Resilience and Why Your Business Needs It by Federico Hansen ?
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SANS – Cloud Security Foundations, Frameworks, and Beyond – In partnership with aws , Google Cloud and Microsoft
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Developer´s Guide to OWASP – Top 10 API Security vulnerabilities & MITRE ATT&ACK framework relation – Go Lang Edition by Farshid Mahdavipour , Kumar Chandramoulie , Joe Vadakkan
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Threat Hunting Framework by Cyborg Security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2023 Data Security Incident Response Report – Seurity Measures & Approach by BlakerHostetler
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2023 Annual Report – Cybersecurity Trends & Insights by Perception Point
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
MANDIANT – M-Trends 2023 – Mandiant Special Report
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Cost of Inaction – A CISOs guide for getting boards of directors to invest in cybersecurity by Microsoft Security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
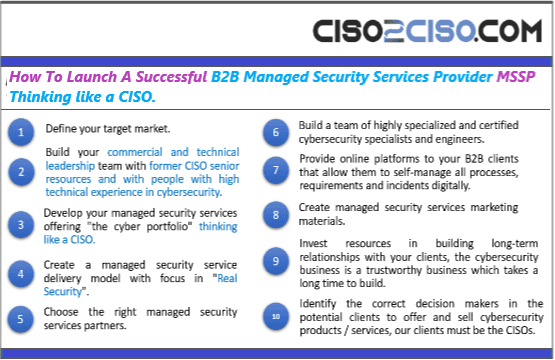
How To Launch A Successful B2B Managed Security Services Provider MSSP Thinking like a CISO
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The convergence of observability and security is critical to realizing DevSecOps potential. Dynatrace CISO report 2023
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2023 Voice of the CISO – Global Insights into CISO challenges, expectactions and priorities report by proofpoint
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A CISOs Guide to Defender Alignment by exabean
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...