Source: thehackernews.com – Author: . Jan 05, 2024NewsroomMalware / Cyber Espionage A new variant of remote access trojan called Bandook has been observed being propagated via...
Author: admin
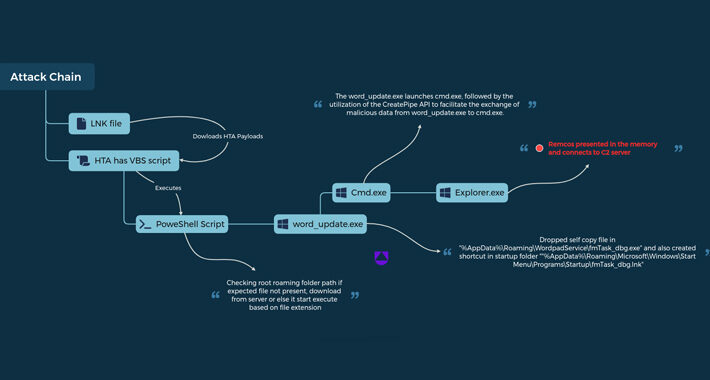
Threat Group Using Rare Data Transfer Tactic in New RemcosRAT Campaign – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer 3 Min Read Source: ozrimoz via Shutterstock A threat actor known for repeatedly targeting organizations in Ukraine with...
C3 Complete Acquires Information Security Business Unit of Compliance Solutions Inc. – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE DELRAY BEACH, Fla., Jan. 4, 2024 /PRNewswire-PRWeb/ — C3 Complete, an award-winning provider of technology, telecom, and information security services, today announced that...
Three Ways To Supercharge Your Software Supply Chain Security – Source:thehackernews.com
Source: thehackernews.com – Author: . Section four of the “Executive Order on Improving the Nation’s Cybersecurity” introduced a lot of people in tech to the concept...
Getting Started With Passkeys, One Service at a Time – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Artemis Diana via Alamy Passkeys gained momentum in 2023. In addition to the major three technology firms...
Russian Agents Hack Webcams to Guide Missile Attacks on Kyiv – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: 99Art via Shutterstock The Security Service of Ukraine (SSU) has asked owners and operators of webcams in...
SonicWall Accelerates SASE Offerings; Acquires Proven Cloud Security Provider – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE MILPITAS, Calif. — January 3, 2024 — SonicWall, a global cybersecurity leader, today announced the acquisition of Banyan Security, a leading...
SentinelOne to Expand Cloud Security Capabilities With Acquisition of PingSafe – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE MOUNTAIN VIEW, CA – January 3, 2024 – SentinelOne (NYSE: S), a global leader in AI-powered security, today announced that it has...
iFlock Security Consulting Secures Private Funding – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE WAKARUSA, Ind., Jan. 3, 2024 /PRNewswire/ — iFlock Security Consulting, a leading boutique cybersecurity company specializing in penetration testing and ancillary services,...
Cybercriminals Flood Dark Web With X (Twitter) Gold Accounts – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Pixel-shot via Alamy Stock Photo Cybercriminals are taking over verified “Gold” accounts on X,...
LastPass Hikes Password Requirements to 12 Characters – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading 2 Min Read Source: SOPA Images Limited via Alamy Stock Photo Password-manager purveyor LastPass has announced it’s...
Beware: 3 Malicious PyPI Packages Found Targeting Linux with Crypto Miners – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 04, 2024NewsroomCryptocurrency Miner / Malware Three new malicious packages have been discovered in the Python Package Index (PyPI) open-source repository...
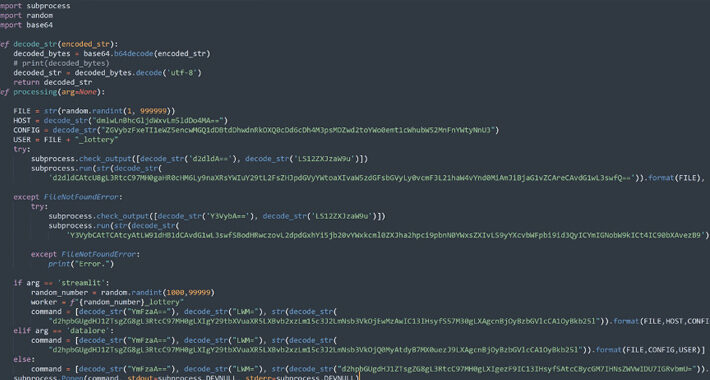
UAC-0050 Group Using New Phishing Tactics to Distribute Remcos RAT – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 04, 2024NewsroomSoftware Security / Malware The threat actor known as UAC-0050 is leveraging phishing attacks to distribute Remcos RAT using...
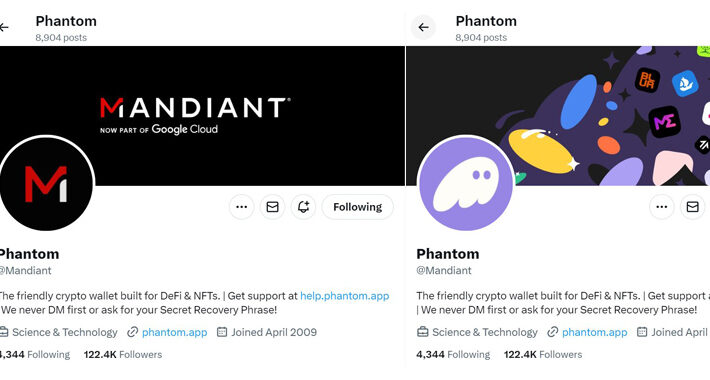
Mandiant’s Twitter Account Restored After Six-Hour Crypto Scam Hack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 04, 2024NewsroomCryptocurrency / Social Media American cybersecurity firm and Google Cloud subsidiary Mandiant had its X (formerly Twitter) account compromised...
Malware Using Google MultiLogin Exploit to Maintain Access Despite Password Reset – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 03, 2024NewsroomMalware / Data Theft Information stealing malware are actively taking advantage of an undocumented Google OAuth endpoint named MultiLogin...
‘Black Basta Buster’ Exploits Ransomware Bug for File Recovery – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Researchers have exploited a weakness in a particular strain of the Black Basta ransomware to release a decryptor...
Name That Edge Toon: Frosty the Steel Man – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist Dark Reading is part of the Informa Tech Division of Informa PLC This site is operated by a business...
5 Ways to Reduce SaaS Security Risks – Source:thehackernews.com
Source: thehackernews.com – Author: . As technology adoption has shifted to be employee-led, just in time, and from any location or device, IT and security teams...
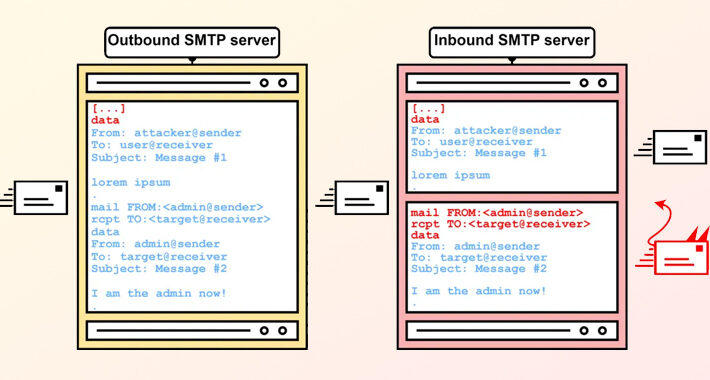
SMTP Smuggling: New Flaw Lets Attackers Bypass Security and Spoof Emails – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 03, 2024NewsroomCyber Threat / Email Security A new exploitation technique called Simple Mail Transfer Protocol (SMTP) smuggling can be weaponized...
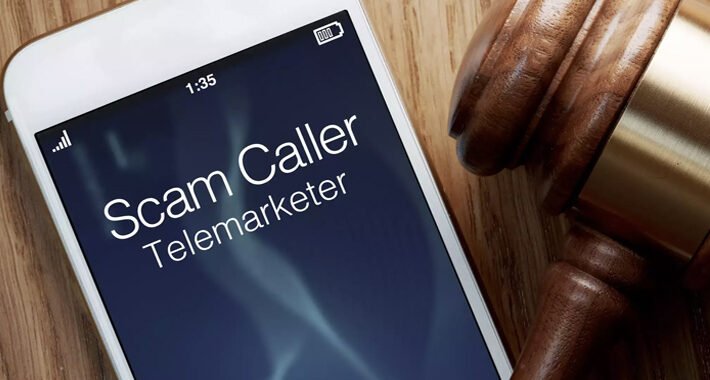
DOJ Slams XCast with $10 Million Fine Over Massive Illegal Robocall Operation – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 03, 2024NewsroomVoIP Service / Regulatory Compliance The U.S. Department of Justice (DoJ) on Tuesday said it reached a settlement with...
Cybercriminals Share Millions of Stolen Records During Holiday Break – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Anucha Cheechang via Shutterstock Cybercriminals collectively leaked some 50 million records containing sensitive personal information in the...
Google Settles Lawsuit Over Tracking ‘Incognito Mode’ Chrome Users – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Tim Walton via Alamy Stock Photo Google is settling a class-action lawsuit over how it tracks data...
Israel Battles Spike in Wartime Hacktivist, OT Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Source: Birgit Korber via Alamy Stock Photo For Israel, 2023 will be remembered as the beginning...
Attackers Abuse Google OAuth Endpoint to Hijack User Sessions – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: imageBROKER via Alamy Stock Photo Attackers have been exploiting an undocumented Google OAuth endpoint to hijack user...
10 Years After Yahoo Breach, What’s Changed? (Not Much) – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: PhotoEdit via Alamy Stock Photo In September 2016, Yahoo copped to a breach of 500 million user...
The Definitive Enterprise Browser Buyer’s Guide – Source:thehackernews.com
Source: thehackernews.com – Author: . Security stakeholders have come to realize that the prominent role the browser has in the modern corporate environment requires a re-evaluation...
Google Settles $5 Billion Privacy Lawsuit Over Tracking Users in ‘Incognito Mode’ – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 02, 2024NewsroomData Privacy / Online Tracking Google has agreed to settle a lawsuit filed in June 2020 that alleged that...
New Variant of DLL Search Order Hijacking Bypasses Windows 10 and 11 Protections – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 01, 2024NewsroomWindows Security / Vulnerability Security researchers have detailed a new variant of a dynamic link library (DLL) search order...
New Terrapin Flaw Could Let Attackers Downgrade SSH Protocol Security – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 01, 2024NewsroomEncryption / Network Security Security researchers from Ruhr University Bochum have discovered a vulnerability in the Secure Shell (SSH)...
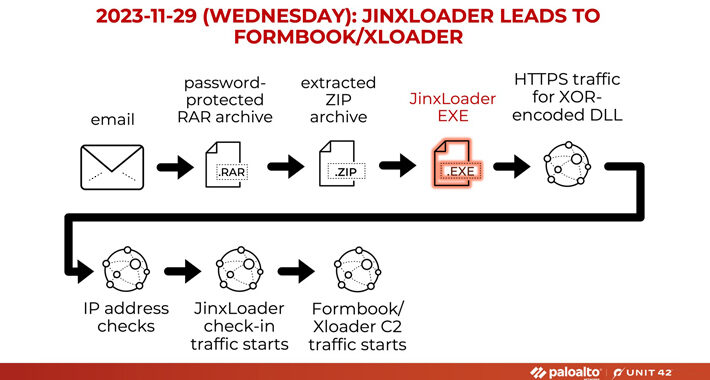
New JinxLoader Targeting Users with Formbook and XLoader Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 01, 2024NewsroomMalware / Dark Web A new Go-based malware loader called JinxLoader is being used by threat actors to deliver...