Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading 1 Min Read Source: Mohammad Aaref Barahouei via Alamy Stock Photo After a two-year investigation into the...
Author: admin
Cacti Monitoring Tool Spiked by Critical SQL Injection Vulnerability – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Nate Hovee via Shutterstock A critical vulnerability in the Cacti Web-based open source framework for monitoring network...
Turkish APT ‘Sea Turtle’ Resurfaces to Spy on Kurdish Opposition – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Marius Graf via Alamy Stock Photo A group aligned with the interests of the government of Turkey...
‘Swatting’ Becomes Latest Extortion Tactic in Ransomware Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading 1 Min Read Source: Nipiphon Na Chiangmai via Alamy Stock Photo Using a tactic known as...
Syrian Hackers Distributing Stealthy C#-Based Silver RAT to Cybercriminals – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 08, 2024NewsroomMalware / Cybercrime Threat actors operating under the name Anonymous Arabic have released a remote access trojan (RAT) called...
Secure Browser Usage Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: A web browser is an indispensable feature of every computer and, in some cases, the only truly essential feature (such as with...
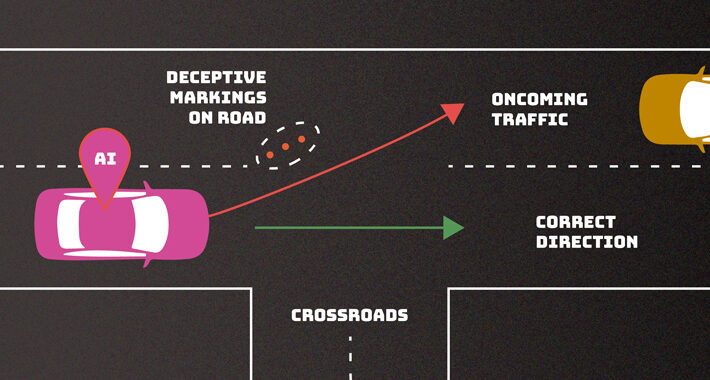
NIST Warns of Security and Privacy Risks from Rapid AI System Deployment – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 08, 2024NewsroomArtificial Intelligence / Cyber Security The U.S. National Institute of Standards and Technology (NIST) is calling attention to the...
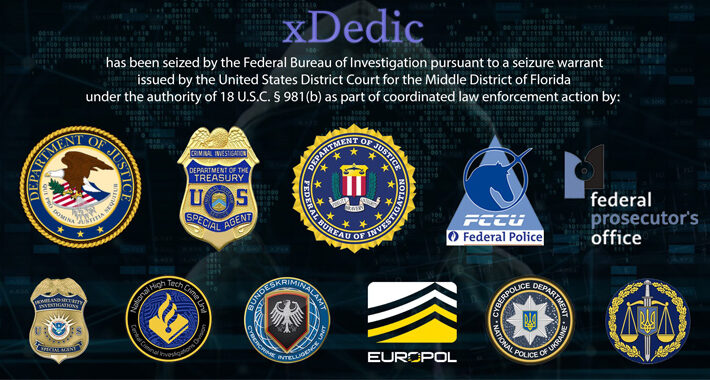
DoJ Charges 19 Worldwide in $68 Million xDedic Dark Web Marketplace Fraud – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 08, 2024NewsroomFinancial Fraud / Cybercrime The U.S. Department of Justice (DoJ) said it charged 19 individuals worldwide in connection with...
North Korea’s Cyber Heist: DPRK Hackers Stole $600 Million in Cryptocurrency in 2023 – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 08, 2024NewsroomCryptocurrency / Financial Crime Threat actors affiliated with the Democratic People’s Republic of Korea (also known as North Korea)...
Mastering the Linux CLI: Unleashing the Power of Commands – Source: securityboulevard.com
Source: securityboulevard.com – Author: CyB3rBEA$T In the ever-evolving landscape of operating systems, Linux stands out as a robust and versatile solution that has captured the hearts...
Apache ERP Zero-Day Underscores Dangers of Incomplete Patches – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Brain Light via Alamy Stock Photo Unknown groups have launched probes against a zero-day vulnerability identified in...
Airbus Looks to Acquire Atos Cybersecurity Unit for Nearly $2 Billion – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer 3 Min Read Source: Markus Mainka via Alamy Stock Photo Aerospace giant Airbus and French IT services company...
Russia Kyivstar Hack Should Alarm West, Ukraine Security Chief Warns – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading 1 Min Read Source: Skorzewiak via Alamy Stock Photo December’s cyberattack on Ukrainian telecommunications operator Kyivstar by...
Mandiant’s X (Twitter) Account Hacked to Promote Crypto Scam – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Klaus Ohlenschlaeger via Alamy Stock Photo The X (Twitter) account of Google’s cybersecurity firm Mandiant was restored...
‘Cyber Toufan’ Hacktivists Leaked 100-Plus Israeli Orgs in One Month – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Issam Elhafti via Alamy Stock Photo Since mid-November, one Iran-linked hacktivist group has managed to breach more...
Sea Turtle Cyber Espionage Campaign Targets Dutch IT and Telecom Companies – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 06, 2024NewsroomCyber Espionage / Supply Chain Attack Telecommunication, media, internet service providers (ISPs), information technology (IT)-service providers, and Kurdish websites...
Pro-Iranian Hacker Group Targeting Albania with No-Justice Wiper Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 06, 2024NewsroomMalware / Cyber Attack The recent wave of cyber attacks targeting Albanian organizations involved the use of a wiper...
How to Build a Phishing Playbook Part 2: Wireframing – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kartik Subramanian, Engineering Welcome back to our series on automating phishing investigation and response with playbooks in Smart SOAR. This is a...
Fire Sale: Zeppelin Ransomware Source Code Sells for $500 on Dark Web – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: World History Archive via Alamy Stock Photo A threat actor has sold for just $500 the source...
23andMe: ‘Negligent’ Users at Fault for Breach of 6.9M Records – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: michelmond via Alamy Stock Photo Up against an onslaught of lawsuits, 23andMe is denying liability for millions...
North Korea Debuts ‘SpectralBlur’ Malware Amid macOS Onslaught – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading 1 Min Read Source: alimdi.net via Alamy Stock Photo The prolific North Korean state-backed threat...
Syrian Threat Group Peddles Destructive SilverRAT – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer GagoDesign via Shutterstock The group behind a sophisticated remote access Trojan, SilverRAT, has links to both Turkey and...
C3 Complete Acquires Information Security Business Unit of Compliance Solutions Inc. – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE DELRAY BEACH, Fla., Jan. 4, 2024 /PRNewswire-PRWeb/ — C3 Complete, an award-winning provider of technology, telecom, and information security services, today announced that...
Driven Technologies Expands Expertise With Acquisition of ieMentor – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE NEW YORK, Jan. 3, 2024 /PRNewswire/ — Driven Acquisition Inc, DBA Driven Technologies, a NY based leading cybersecurity and cloud service provider, today announced the...
Industrial Defender Risk Signal, a Risk-Based Vulnerability Management Solution for OT Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE FOXBOROUGH, Mass. , Jan. 3, 2024 /PRNewswire/ — Industrial Defender, the leading provider of OT asset data and cybersecurity solutions for industrial organizations, is...
SpectralBlur: New macOS Backdoor Threat from North Korean Hackers – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 05, 2024NewsroomEndpoint Security / Malware Cybersecurity researchers have discovered a new Apple macOS backdoor called SpectralBlur that overlaps with a...
Exposed Secrets are Everywhere. Here’s How to Tackle Them – Source:thehackernews.com
Source: thehackernews.com – Author: . Picture this: you stumble upon a concealed secret within your company’s source code. Instantly, a wave of panic hits as you...
Orange Spain Faces BGP Traffic Hijack After RIPE Account Hacked by Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 05, 2024NewsroomNetwork Security / Malware Mobile network operator Orange Spain suffered an internet outage for several hours on January 3...
Alert: Ivanti Releases Patch for Critical Vulnerability in Endpoint Manager Solution – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 05, 2024NewsroomVulnerability / Network Security Ivanti has released security updates to address a critical flaw impacting its Endpoint Manager (EPM)...
Russian Hackers Had Covert Access to Ukraine’s Telecom Giant for Months – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 05, 2024NewsroomCyber Attack / Data Breach Ukrainian cybersecurity authorities have disclosed that the Russian state-sponsored threat actor known as Sandworm...