Source: thehackernews.com – Author: . Dec 30, 2023NewsroomCryptocurrency / Phishing Scam Cybersecurity researchers are warning about an increase in phishing attacks that are capable of draining...
Author: admin
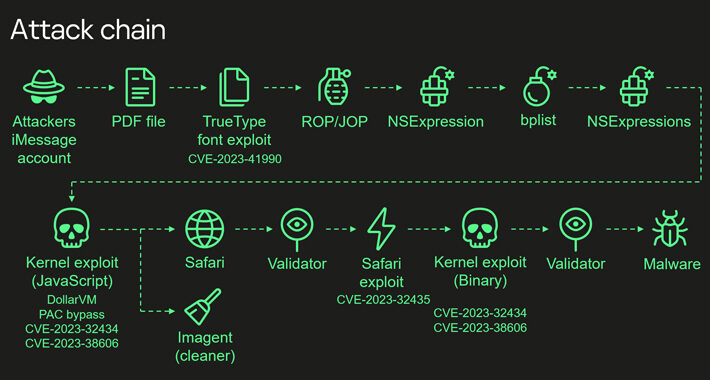
‘Operation Triangulation’ Spyware Attackers Bypass iPhone Memory Protections – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer Source: leonello calvetti via Alamy Stock Photo A previously undocumented hardware feature within Apple’s iPhone System on a...
Palo Alto Networks Closes Talon Cybersecurity Acquisition – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SANTA CLARA, Calif., Dec. 28, 2023 /PRNewswire/ — Palo Alto Networks (NASDAQ: PANW), the global cybersecurity leader, today announced that it has completed...
I Securely Resolve: CISOs, IT Security Leaders Share 2024 Resolutions – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer Source: cn0ra via Alamy Stock Photo With the aim of fortifying defenses and navigating changing risks, IT security...
Albanian Parliament and One Albania Telecom Hit by Cyber Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 29, 2023NewsroomCyber Attack / Web Security The Assembly of the Republic of Albania and telecom company One Albania have been...
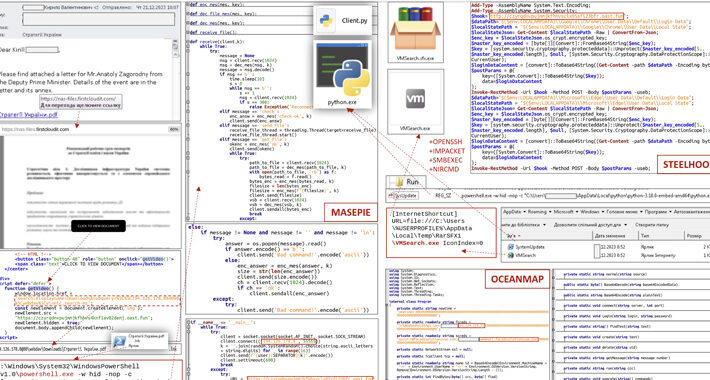
CERT-UA Uncovers New Malware Wave Distributing OCEANMAP, MASEPIE, STEELHOOK – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 29, 2023NewsroomEmail Security / Malware The Computer Emergency Response Team of Ukraine (CERT-UA) has warned of a new phishing campaign...
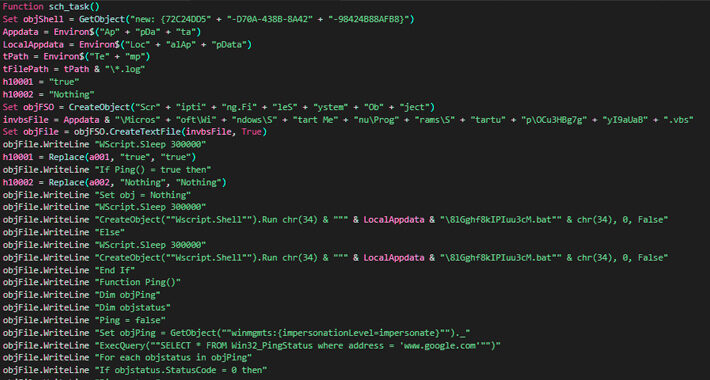
Kimsuky Hackers Deploying AppleSeed, Meterpreter, and TinyNuke in Latest Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 29, 2023NewsroomMalware / Cyber Threat Nation-state actors affiliated to North Korea have been observed using spear-phishing attacks to deliver an...
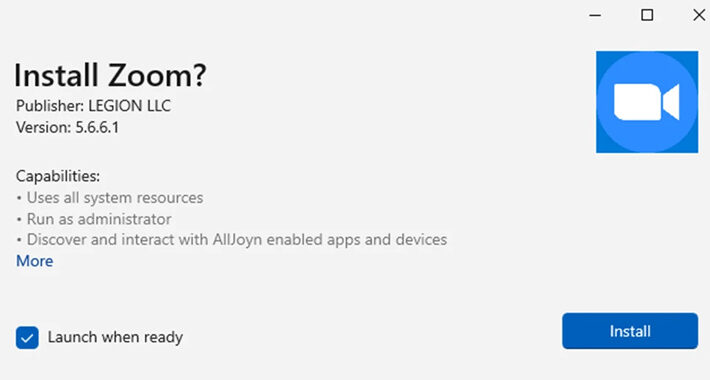
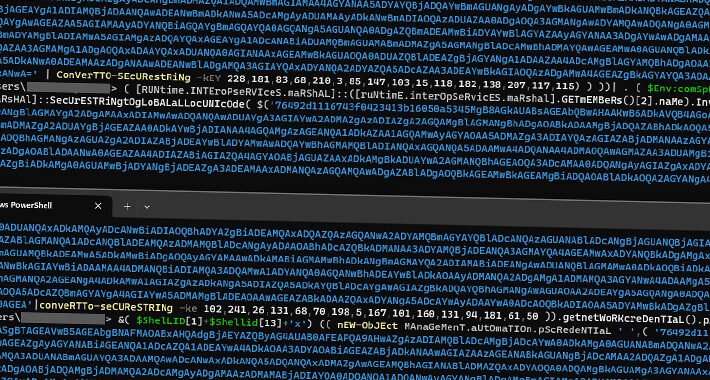
Microsoft Disables MSIX App Installer Protocol Widely Used in Malware Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 29, 2023NewsroomMalware / Endpoint Security Microsoft on Thursday said it’s once again disabling the ms-appinstaller protocol handler by default following...
Google Cloud Resolves Privilege Escalation Flaw Impacting Kubernetes Service – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 28, 2023NewsroomCloud Security / Data Protection Google Cloud has addressed a medium-severity security flaw in its platform that could be...
Most Sophisticated iPhone Hack Ever Exploited Apple’s Hidden Hardware Feature – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 28, 2023NewsroomSpyware / Hardware Security The Operation Triangulation spyware attacks targeting Apple iOS devices leveraged never-before-seen exploits that made it...
New Rugmi Malware Loader Surges with Hundreds of Daily Detections – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 28, 2023NewsroomMalware / Cyber Threat A new malware loader is being used by threat actors to deliver a wide range...
How Cybercriminals Will Sway 2024 US Elections, Or Try To – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Casimiro PT via Shutterstock Foreign interference actors, mostly operating out of Russia, Iran, and China, are ramping...
Critical Zero-Day in Apache OfBiz ERP System Exposes Businesses to Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 27, 2023NewsroomZero-Day / Vulnerability A new zero-day security flaw has been discovered in the Apache OfBiz, an open-source Enterprise Resource...
Chinese Hackers Exploited New Zero-Day in Barracuda’s ESG Appliances – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 27, 2023NewsroomZero-Day / Email Security Barracuda has revealed that Chinese threat actors exploited a new zero-day in its Email Security...
New Sneaky Xamalicious Android Malware Hits Over 327,000 Devices – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 27, 2023NewsroomPrivacy / App Security A new Android backdoor has been discovered with potent capabilities to carry out a range...
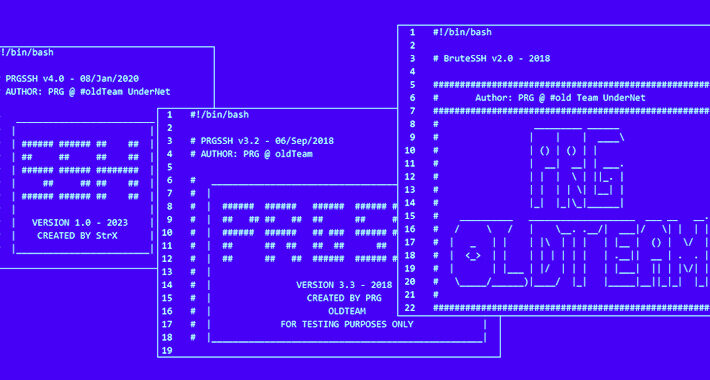
Warning: Poorly Secured Linux SSH Servers Under Attack for Cryptocurrency Mining – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 27, 2023NewsroomMalware / Server Security Poorly secured Linux SSH servers are being targeted by bad actors to install port scanners...
Europe Sees More Hacktivism, GDPR Echoes, and New Security Laws Ahead for 2024 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer Source: SOPA Images Limited via Alamy Stock Photo An evolving geopolitical landscape has impacted cybersecurity in Europe this...
Cyber Employment 2024: Sky-High Expectations Fail Businesses & Job Seekers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Puhhha via Shutterstock Well-publicized estimates of a massive shortfall in cybersecurity workers have resulted in high expectations...
African Organizations Aim to Fix Cybersecurity in 2024 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Peter Kovac via Alamy Stock Photo Faced with numerous cybersecurity threats and challenges, but lacking adequate cyber...
Carbanak Banking Malware Resurfaces with New Ransomware Tactics – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 26, 2023NewsroomMalware / Cybercrime The banking malware known as Carbanak has been observed being used in ransomware attacks with updated...
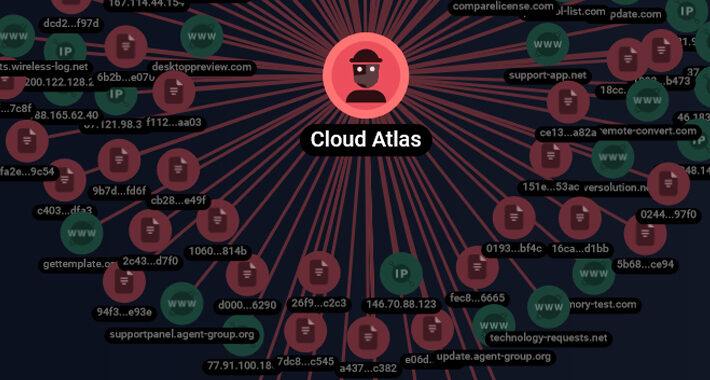
Cloud Atlas’ Spear-Phishing Attacks Target Russian Agro and Research Companies – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 25, 2023NewsroomCyber Espionage / Malware The threat actor referred to as Cloud Atlas has been linked to a set of...
British LAPSUS$ Teen Members Sentenced for High-Profile Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 24, 2023NewsroomCyber Crime / Data Breach Two British teens part of the LAPSUS$ cyber crime and extortion gang have been...
Ransomware Attackers Abuse Multiple Windows CLFS Driver Zero-Days – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: cryptoFX via Alamy Stock Photo In the last year and a half, attackers have exploited at least...
Google Releases Eighth Zero-Day Patch of 2023 for Chrome – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer Source: PREMIO STOCK via Shutterstock Google has issued an urgent update to address a recently discovered vulnerability in...
Rogue WordPress Plugin Exposes E-Commerce Sites to Credit Card Theft – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 22, 2023NewsroomSkimming / Web Security Threat hunters have discovered a rogue WordPress plugin that’s capable of creating bogus administrator users...
Operation RusticWeb: Rust-Based Malware Targets Indian Government Entities – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 22, 2023NewsroomMalware / Cyber Threat Indian government entities and the defense sector have been targeted by a phishing campaign that’s...
Decoy Microsoft Word Documents Used to Deliver Nim-Based Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 22, 2023NewsroomSocial Engineering / Malware Analysis A new phishing campaign is leveraging decoy Microsoft Word documents as bait to deliver...
How States Help Municipalities Build Their Cyber Defenses – Source: www.darkreading.com
Source: www.darkreading.com – Author: Stephen Lawton, Contributing Writer Source: Image Professionals GmbH via Alamy Stock Photo As CISO for the state of North Dakota, Michael Gregg...
Bugcrowd Announces Vulnerability Ratings for LLMs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Source: Wavebreak Media Ltd via Alamy Stock Photo Bugcrowd has updated its Vulnerability Rating Taxonomy (VRT) with a new rating system to...
UAC-0099 Using WinRAR Exploit to Target Ukrainian Firms with LONEPAGE Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 22, 2023NewsroomMalware / Cyber Attack The threat actor known as UAC-0099 has been linked to continued attacks aimed at Ukraine,...