Source: thehackernews.com – Author: . Generative AI will enable anyone to launch sophisticated phishing attacks that only Next-generation MFA devices can stop The least surprising headline...
Author: admin
Atomic Stealer Gets an Upgrade – Targeting Mac Users with Encrypted Payload – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 11, 2024NewsroomMalvertising / Cyber Attacks Cybersecurity researchers have identified an updated version of a macOS information stealer called Atomic (or...
Mandiant’s X Account Was Hacked Using Brute-Force Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 11, 2024NewsroomOnline Security / Cryptocurrency The compromise of Mandiant’s X (formerly Twitter) account last week was likely the result of...
Chinese Hackers Exploit Zero-Day Flaws in Ivanti Connect Secure and Policy Secure – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 11, 2024NewsroomCybersecurity / Zero-Day A pair of zero-day flaws identified in Ivanti Connect Secure (ICS) and Policy Secure have been...
Cisco Fixes High-Risk Vulnerability Impacting Unity Connection Software – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 11, 2024NewsroomVulnerability / Patch Management Cisco has released software updates to address a critical security flaw impacting Unity Connection that...
Attacker Targets Hadoop YARN, Flint Servers in Stealthy Campaign – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer 3 Min Read Source: NicoElNino via Shutterstock A threat actor is targeting a common misconfiguration in Hadoop YARN...
CES 2024: Will the Coolest New AI Gadgets Protect Your Privacy? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: GK Images via Alamy Stock Photo Phones and computers host some of the most private information about...
Has the Investment Bubble Burst in Israeli Cybersecurity? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Source: Roman Barkov via Alamy Stock Photo Funding for Israeli startups dropped by 60% in the...
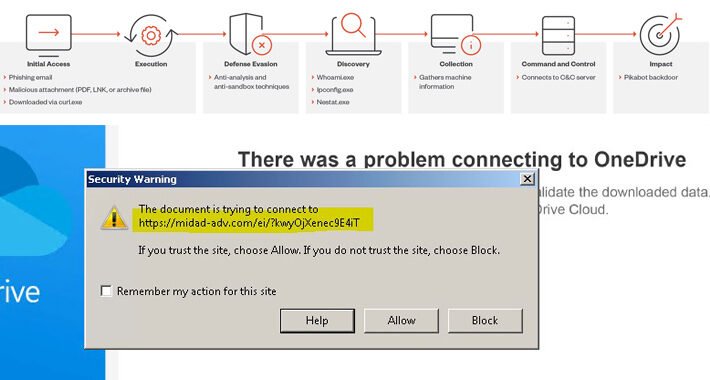
Pikabot Malware Surfaces as Qakbot Replacement for Black Basta Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Negro Elkha via Adobe Stock Photo A threat actor associated with Black Basta ransomware attacks has been...
NoaBot: Latest Mirai-Based Botnet Targeting SSH Servers for Crypto Mining – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 10, 2024NewsroomServer Security / Cryptocurrency A new Mirai-based botnet called NoaBot is being used by threat actors as part of...
Getting off the Attack Surface Hamster Wheel: Identity Can Help – Source:thehackernews.com
Source: thehackernews.com – Author: . IT professionals have developed a sophisticated understanding of the enterprise attack surface – what it is, how to quantify it and...
Patch Now: Critical Windows Kerberos Bug Bypasses Microsoft Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Soure: Andrii Yalanskyi via Shutterstock Microsoft eased enterprise security teams into 2024 with a relatively light January security...
Ukraine Claims Revenge Hack Against Moscow Internet Provider – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading 1 Min Read Source: Imaginechina Limited via Alamy Stock Photo Sources reportedly tipped off Ukraine media to...
Hospitality Hackers Target Hotels’ Booking.com Logins – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Aleksey Zotov via Alamy Stock Photo Cyberattackers are hitting the digital road, looking to...
Path Traversal Bug Besets Popular Kyocera Office Printers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer 3 Min Read Source: Piotr Adamowicz via Alamy Stock Photo A newly published path traversal vulnerability could enable...
Turkish Cyber Threat Targets MSSQL Servers With Mimic Ransomware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer Source: cryptoFX via Alamy Stock Photo A sophisticated attack campaign codenamed RE#TURGENCE by researchers has been discovered infiltrating...
Delinea Acquires Authomize to Strengthen Extended PAM – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SAN FRANCISCO, Jan. 9, 2024 /PRNewswire/ — Delinea, a leading provider of solutions that seamlessly extend Privileged Access Management (PAM), today announced it...
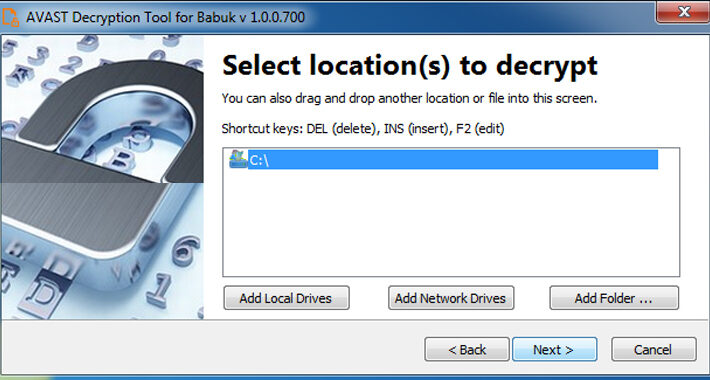
Free Decryptor Released for Black Basta and Babuk’s Tortilla Ransomware Victims – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 10, 2024NewsroomRansomware / Data Security A decryptor for the Tortilla variant of the Babuk ransomware has been released by Cisco...
FTC Bans Outlogic (X-Mode) From Selling Sensitive Location Data – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 10, 2024NewsroomPrivacy / Regulatory Compliance The U.S. Federal Trade Commission (FTC) on Tuesday prohibited data broker Outlogic, which was previously...
Microsoft’s January 2024 Windows Update Patches 48 New Vulnerabilities – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 10, 2024NewsroomVulnerability / Windows Security Microsoft has addressed a total of 48 security flaws spanning its software as part of...
CISA Flags 6 Vulnerabilities – Apple, Apache, Adobe , D-Link, Joomla Under Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 10, 2024NewsroomPatch Management / Threat Intelligence The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added six security flaws to...
Alert: Water Curupira Hackers Actively Distributing PikaBot Loader Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 09, 2024NewsroomMalware / Cyber Threat A threat actor called Water Curupira has been observed actively distributing the PikaBot loader malware...
Turkish Hackers Exploiting Poorly Secured MS SQL Servers Across the Globe – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 09, 2024NewsroomData Security / Cyber Attack Poorly secured Microsoft SQL (MS SQL) servers are being targeted in the U.S., European...
Why Public Links Expose Your SaaS Attack Surface – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 09, 2024The Hacker NewsSaaS Security / Data Security Collaboration is a powerful selling point for SaaS applications. Microsoft, Github, Miro,...
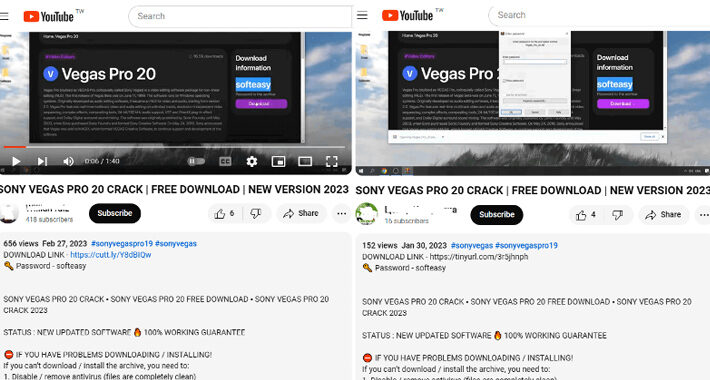
Beware Weaponized YouTube Channels Spreading Lumma Stealer – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Linaiimages via Shutterstock Attackers have been spreading a variant of the Lumma Stealer via YouTube channels that...
TitanHQ Launches PhishTitan to Combat Advanced Phishing Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE GALWAY, Ireland & SHELTON, Conn., Jan. 09, 2024 (NEWSWIRE) — TitanHQ, the leading cloud-based email security solutions provider for over...
Alert: New Vulnerabilities Discovered in QNAP and Kyocera Device Manager – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 09, 2024NewsroomNetwork Security / Data Protection A security flaw has been disclosed in Kyocera’s Device Manager product that could be...
Beware! YouTube Videos Promoting Cracked Software Distribute Lumma Stealer – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 09, 2024NewsroomMalware / Cyber Threat Threat actors are resorting to YouTube videos featuring content related to cracked software in order...
Ditch the Passwords: Discover the Magic of WebAuthn and Passkeys – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author In today’s digital age, passwords have become a necessary evil. We rely on them to...
Mastering the ‘cd’ Command: Tips and Tricks for Efficient Directory Navigation – Source: securityboulevard.com
Source: securityboulevard.com – Author: CyB3rBEA$T Navigating through directories is a fundamental aspect of working in a command-line interface, and the ‘cd’ command plays a crucial role...