As recently as 2021, the notorious Russian APT28 was exploiting network routers running outdated versions of Cisco’s IOS and IOS XE operating system software, using them...
Author: admin
7 Sizzling Sessions to Check Out at RSA Conference 2023
Keep up with the latest cybersecurity threats, newly-discovered vulnerabilities, data breach information, and emerging trends. Delivered daily or weekly right to your email inbox. Subscribe Views:...
Gary Bowser, Former Nintendo Hacker, Released From Prison
Gary Bowser, who was indicted in 2020 and sentenced in 2021 to 40 months in prison for being a part of a hacking ring known as Team...
Popular Fitness Apps Leak Location Data Even When Users Set Privacy Zones
Fitness apps such as Strava leak sensitive location information of users, even when they’ve used in-app features to specifically set up privacy zones to hide their...
3 Flaws, 1 War Dominated Cyber-Threat Landscape in 2022
Popular attacks for a trio of critical vulnerabilities kept exploitation at the top of the list of initial-access methods in 2022, while the war between Russia...
How to Prevent 2 Common Attacks on MFA
It’s a well-known and statistically proven fact that password-only credentials pose the highest cyber-risk to people and organizations. Passwords are easily compromised through a wide variety...
NSO Group Is Back in Business With 3 New iOS Zero-Click Exploits
Israeli spyware firm NSO Group is back with at least three new iOS 15 and iOS 16 zero-click exploit chains, which were used against human rights activists...
Researchers Discover First Ever Major Ransomware Targeting macOS
The infamous LockBit ransomware gang has developed a version of their malware for macOS devices — the first ever foray into Apple’s territory by a major...
‘Goldoson’ Malware Sneaks into Google Play Apps, Racks Up 100M Downloads
Malware that can steal data and commit click fraud has hitched a ride into 60 mobile apps, via an infected third-party library. The infected apps have logged more...
As Consumer Privacy Evolves, Here’s How You Can Stay Ahead of Regulations
Proposition 24, also known as the California Privacy Rights Act (CPRA), went into effect in January. Passed by California voters in November 2020, the CPRA increases...
ZeroFox Acquires LookingGlass
On Monday, ZeroFox announced plans to acquire LookingGlass, a threat intelligence and attack surface management company, for roughly $26 million. ZeroFox provides protection against phishing and...
Global Automotive Cybersecurity Report 2022 – Automotive Cyber Threat Landscape in Light of New Regulations by Upstream
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
FIN7, Former Conti Gang Members Collaborate on ‘Domino’ Malware
Former members of the Conti ransomware group are compromising systems for follow-up exploits using malware that the financially motivated FIN7 group developed; FIN7 has used the “Domino” tool in...
Google Issues Emergency Chrome Update for Zero-Day Bug
A Google Chrome zero-day vulnerability is under active exploit in the wild, and while details are scarce, users are urged to update their Windows, Mac, and...
Pen Testers Need to Hack AI, but Also Question Its Existence
Samsung has banned some uses of ChatGPT, Ford Motor and Volkswagen shuttered their self-driving car firm, and a letter calling for a pause in training more...
How CISOs Can Craft Better Narratives for the Board
For at least a decade now, career-minded security leaders have well understood the importance of effective communication with the board and CEO. CISOs know they must...
Aloha PoS Restaurant Software Downed by Ransomware Attack
After days of outages, NCR Corp. has confirmed that its Aloha point-of-sale (PoS) software platform, used by thousands of restaurants across the US, was taken down...
Telegram – How a Messenger Turned into a Cybercrime Ecosystem by 2023 by Kela Cybercrime Intelligence
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The State of Cloud Native Security Report 2023 by Paloalto Networks
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Russian SolarWinds Culprits Launch Fresh Barrage of Espionage Cyberattacks
As part of its ongoing invasion of Ukraine, Russian intelligence has once again enlisted the services of hacker group Nobelium/APT29, this time to spy on foreign...
Software-Dependency Data Delivers Security to Developers
Developers interested in gauging the security of the open source components have an abundant number of choices, but still have to choose to use the information...
Bugs in Manarium Play-to-Earn Platform Showcase Crypto-Gaming Insecurity
A proof-of-concept (PoC) hack of the Manarium play-to-earn (P2E) gaming platform allowed researchers to arbitrarily change their scores to win daily tournaments and collect crypto tokens,...
Western Digital Hackers Demand 8-Figure Ransom Payment for Data
After stealing around 10TB of data from Western Digital Corp., the computer drive manufacturer behind digital storage brand SanDisk, hackers are now negotiating a ransom payment...
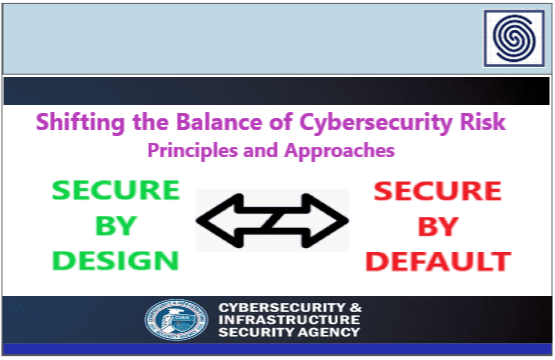
Shifting the Balance of Cybersecurity Risk – Principles and Approaches for Secure-by-Design – Secure-by-Default – CISA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
New Mirai Variant Employs Uncommon Tactics to Distribute Malware
A new version of a Mirai variant called RapperBot is the latest example of malware using relatively uncommon or previously unknown infection vectors to try and...
Money Ransomware Group Enters Double-Extortion Fray
An emerging threat group dubbed Money Ransomware has adopted the increasingly popular tactic of encrypting and exfiltrating sensitive data from organizations and threatening to leak it...
Why the US Needs Quantum-Safe Cryptography Deployed Now
While it’s not easy to predict the next breakthrough, most experts estimate quantum computers with tens of thousands of qubits that can crack current encryption will...
Remcos RAT Targets Tax Pros to Scurry Off With Workers’ Filing Info
With the April 18 tax deadline approaching, hackers have been piling onto accountants’ stress with a phishing campaign designed to deliver the Remcos remote access Trojan...
Super-Yacht Specialist Lürssen in Dry Dock After Ransomware Attack
German shipbuilder Lürssen, known for making super yachts for the exorbitantly wealthy, experienced a ransomware attack over Easter weekend that has incapacitated operations. With a high...
The Internet Reform Trilemma
In policy circles, we often hear about the need for a “free,” “open,” and “secure” Internet. This was most recently the case with the White House’s...