Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading RSA CONFERENCE 2023 – San Francisco – The coalition behind the Data Security Maturity Model...
Author: admin
HiddenLayer Nabs Most Innovative Startup Crown at RSAC – Source: www.darkreading.com
Source: www.darkreading.com – Author: Karen Spiegelman, Features Editor RSA CONFERENCE 2023 – San Francisco – CEO Chris Sestito started his three-minute pitch at Innovation Sandbox on...
Building a Better SBOM – Source: www.darkreading.com
Source: www.darkreading.com – Author: Anita D’Amico, VP of Cross-Portfolio Solutions and Strategy, Synopsys Software Integrity Group Software is an important part of every business in 2023....
AI Experts: Account for AI/ML Resilience & Risk While There’s Still Time – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ericka Chickowski, Contributing Writer, Dark Reading RSA CONFERENCE 2023 – San Francisco – As enterprises and government agencies increasingly weave artificial intelligence (AI)...
‘Educated Manticore’ Targets Israeli Victims in Improved Phishing Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading An Iranian threat actor, under the name of Educated Manticore, has been the cause of targeted phishing...
‘Good’ AI Is the Only Path to True Zero-Trust Architecture – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Threat actors armed with artificial intelligence (AI) tools like ChatGPT can pass the bar exam, ace an...
Attackers Abuse PaperCut RCE Flaws to Take Over Enterprise Print Servers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Security researchers have revealed new details about how attackers are exploiting two flaws in the PaperCut enterprise...
DDoS, Not Ransomware, Is Top Business Concern for Edge Networks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer, Dark Reading Distributed denial-of-service (DDoS) is the attack method businesses are most concerned about, believing it will have...
Mobile device security policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: PURPOSE This Mobile Device Security Policy from TechRepublic Premium provides guidelines for mobile device security needs in order to protect businesses and...
Incident response policy
PURPOSE Every enterprise needs to establish a plan of action to assess and then recover from unauthorized access to its network. This policy from TechRepublic Premium...
Millions of Artifacts, Misconfigured Enterprise Software Registries Are Ripe for Pwning
Many organizations, including some of the world’s largest companies, are at heightened risk of compromise and data theft from misconfigured and poorly secured software registries and...
Tangled Up: ‘Tomiris’ APT Uses Turla Malware, Confusing Researchers
Certain campaigns previously connected to the Russian advanced persistent threat (APT) Turla were actually conducted by what appears to be an entirely separate group researchers have...
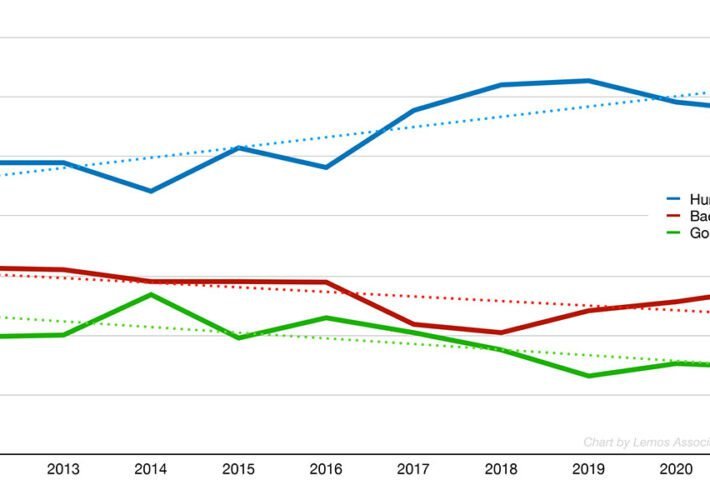
Bot Management Aims to Tame Attacker Automation
Attackers are increasingly automated, with credential stuffing and automated application attacks surging, making the ability to detect, manage and mitigate bot-based requests increasing important. The sector...
Critical Infrastructure Organizations Further Affected in 3CX Breach
Just a month after the North Korea-linked APT hacker group known as Lazarus targeted 3CX in a supply chain attack, Symantec’s researchers have found that two infrastructure...
Qwiet AI Builds a Neural Net to Catch Coding Vulnerabilities
RSA CONFERENCE 2023 – San Francisco – Application security company Qwiet AI announced a new threat intelligence feed for its real-time code security analysis tool PreZero...
North Korea’s Kimsuky APT Keeps Growing, Despite Public Outing
Globally, interest has surged around North Korea’s Kimsuky advanced persistent threat group (a.k.a. APT43) and its hallmarks. Still, the group is showing no signs of slowing...
North Korea’s Kimsuky APT Keeps Growing, Despite Public Outing
Globally, interest has surged around North Korea’s Kimsuky advanced persistent threat group (a.k.a. APT43) and its hallmarks. Still, the group is showing no signs of slowing...
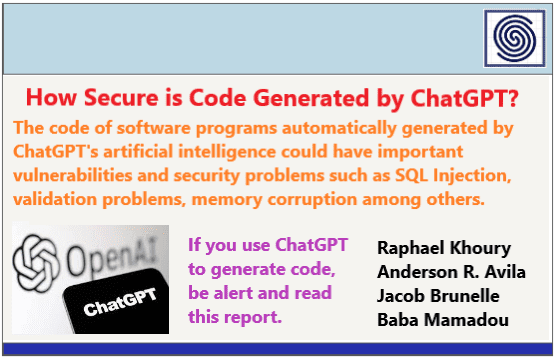
How Secure is Code Generated by ChatGPT ? by Khoury-Avila-Brunelle-Mamadou
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Shields Health Breach Exposes 2.3M Users’ Data
An unauthorized actor gained access to the systems of Shields Health Care Group (SHCG) in March, exposing driver’s license numbers as well as other identification information...
North Korea’s Kimsuky APT Keeps Growing, Despite Public Outing
Globally, interest has surged around North Korea’s Kimsuky advanced persistent threat group (a.k.a. APT43) and its hallmarks. Still, the group is showing no signs of slowing...
North Korea’s Kimsuky APT Keeps Growing, Despite Public Outing
Globally, interest has surged around North Korea’s Kimsuky advanced persistent threat group (a.k.a. APT43) and its hallmarks. Still, the group is showing no signs of slowing...
Introduction to Tabletop Exercises (TTX) – A practical Guidebook for Organizations by Capgemini for GFCE – Global Forum on Cyber Expertise
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
‘GhostToken’ Opens Google Accounts to Permanent Infection
A security vulnerability in Google’s Cloud Platform (GCP) could have allowed cyberattackers to hide an unremovable, malicious application inside a victim’s Google account, dooming the account...
3CX Supply Chain Attack Tied to Financial Trading App Breach
Turns out 3CX was not the original target in a recent supply chain compromise affecting customers of the video conferencing software maker: The attack came via...
Major US CFPB Data Breach Caused by Employee
The Consumer Financial Protection Bureau (CFPB), an agency of the US government that protects consumers in the financial sector, announced that an employee committed a major...
Trigona Ransomware Trolling for ‘Poorly Managed’ MS-SQL Servers
The Trigona ransomware threat actors are waging a campaign against Microsoft SQL database servers because many of them have external connections and weak passwords, leaving them open...
Expert Insight: Dangers of Using Large Language Models Before They Are Baked
The Berryville Institute of Machine Learning (BIML) recently attended Calypso AI’s Accelerate AI 2023 conference in Washington, DC. The meeting included practitioners from both government and...
‘AuKill’ Malware Hunts & Kills EDR Processes
The “AuKill” cybercrime tool has emerged, which threat actors are using to disable endpoint detection and response (EDR) defenses used by enterprises before deploying ransomware. It makes use of...
Incident Response Cheatsheet Windows & Linux by Hackingarticles.in – Ignite Technologies
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Killnet Boss Exposes Rival Leader in Kremlin Hacktivist Beef
There’s drama brewing between various Kremlin-backed hacktivist groups, which percolated into public view this week with the move by Killnet group leader “Killmilk” to expose the identity...