Source: www.csoonline.com – Author: According to a recent study, many organizations still invest too little in protecting their operational technology (OT). Despite OT security increasingly becoming...
Month: April 2025
Surge in threat actors scanning Juniper, Cisco, and Palo Alto Networks devices – Source: www.csoonline.com
Source: www.csoonline.com – Author: Admins need to change default credentials promptly on Juniper SSR, patch Cisco SLU, warns SANS Institute. A surge in internet probes targeting...
GitHub upgrades tooling to help developers stop leaking secrets – Source: www.infoworld.com
Source: www.infoworld.com – Author: news Apr 03, 20253 mins Data and Information SecurityGitHubSecurity Developers get free and targeted advanced secret scanning features on GitHub to protect...
Oracle quietly admits data breach, days after lawsuit accused it of cover-up – Source: www.csoonline.com
Source: www.csoonline.com – Author: A lawsuit filed Monday accused Oracle of failing to acknowledge a recent data breach — but the company has reportedly since informed...
Hackerangriff auf Heilbronner Marketing – Source: www.csoonline.com
Source: www.csoonline.com – Author: Die Heilbronn Marketing wurde Ziel einer Ransomware-Attacke. Ob die Täter auch Daten abgegriffen haben, ist noch unklar. Hacker haben die IT-Systeme der...
Code Like a Woman: Engineering in the Age of AI
Noor Aftab outlines the importance of women in AI, the key women who have moved the industry forward, and the consequences when development teams lack diverse...
WiM and SWE Announce New Partnership to Support Women in Industry
Women in Manufacturing and the Society of Women Engineers collaborate to support women in STEM, providing enhanced membership benefits. Source Views: 1
Payment Fraud Detection and Prevention: Here’s All To Know – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Anna Lynn Dizon Key takeaways: With AI technology, payment fraud and fraud prevention have become more complex and sophisticated. Both financial data...
8 Best Enterprise Password Managers – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Franklin Okeke We may earn from vendors via affiliate links or sponsorships. This might affect product placement on our site, but not...
Major Online Platform for Child Exploitation Dismantled – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: One of the largest online platforms for child sexual exploitation has been dismantled in a major international law enforcement operation. Kidflix, which...
CrushFTP Vulnerability Exploited Following Disclosure Issues – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: Written by A critical authentication bypass vulnerability in CrushFTP, identified as CVE-2025-31161, has been actively exploited by remote attackers following a mishandled...
China-Linked Threat Group Exploits Ivanti Bug – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...
Disclosure Drama Clouds CrushFTP Vulnerability Exploitation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Rob Wright Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
Counterfeit Phones Carrying Hidden Revamped Triada Malware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have...
Runtime Ventures Launches New Fund for Seed, Pre-Seed Startups – Source: www.darkreading.com
Source: www.darkreading.com – Author: Fahmida Y. Rashid Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked?...
Social Engineering Just Got Smarter – Source: www.darkreading.com
Source: www.darkreading.com – Author: Steve Stasiukonis Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
Emerging Risks Require IT/OT Collaboration to Secure Physical Systems – Source: www.darkreading.com
Source: www.darkreading.com – Author: Arielle Waldman Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
Google Quick Share Bug Bypasses Allow Zero-Click File Transfer – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why...
UAC-0219 Attack Detection: A New Cyber-Espionage Campaign Using a PowerShell Stealer WRECKSTEEL – Source: socprime.com
Source: socprime.com – Author: Veronika Telychko In late March 2025, CERT-UA observed a surge in cyber-espionage operations targeting Ukraine, orchestrated by the UAC-0200 hacking group using...
How to Protect Your Spring Sale from Bots – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alexa Bleecker What we did for a global retailer – and how your team can do the same Seasonal sales are massive...
How DataDome Instantly Blocked a 28M-Request Flash DDoS Attack For a $3B E-Commerce Leader – Source: securityboulevard.com
Source: securityboulevard.com – Author: Florent Pajot On March 25, 2025, a global e-commerce platform that handled nearly $3 billion in transactions in 2024 was the target...
BSidesLV24 – HireGround – You Need a Jay-z and a Beyoncé: How Sponsors and Mentors Can Supercharge Your Career in Cybersecurity – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – HireGround – You Need a Jay-z and a Beyoncé: How Sponsors and...
Protecting Users: Prevent and Stop Cyberthreats Before They Start With Kaseya 365 User – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kaseya As the saying goes, “Security is only as strong as the people behind it.” With cyberthreats growing smarter and more targeted,...
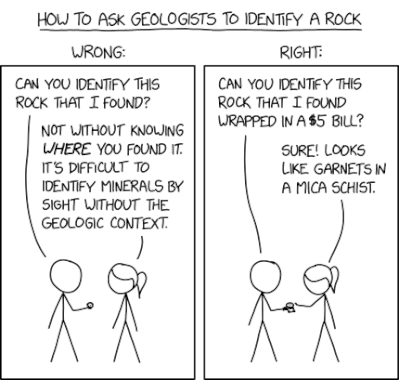
Randall Munroe’s XKCD ‘Rock Identification’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Friday, April 4, 2025 Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News...
CISO Transformation: It’s Time for a New Mental Model – Source: securityboulevard.com
Source: securityboulevard.com – Author: Steve Tout Rethinking the CISO Role Each year, respected industry leaders publish updated mind maps to help CISOs visualize the scope of...
Stopping MFA Fatigue Attacks Before They Start: Securing Your Entry Points – Source: securityboulevard.com
Source: securityboulevard.com – Author: Enzoic MFA Fatigue Attacks on the Rise Yet another challenge is undermining the effectiveness of MFA: MFA fatigue attacks. In an MFA...
Insider Threats Make the Case for Data-centric Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dan Simmons CISOs appear to be spending more on mitigating insider risk. Reports suggest 16.5% of cybersecurity budgets are now devoted to...
Securing OT Environments with Zero Trust: A Joint Approach by ColorTokens and Claroty – Source: securityboulevard.com
Source: securityboulevard.com – Author: Devasmita Das The Growing Cybersecurity Threat in OT Environments As industries undergo digital transformation, the convergence of Information Technology (IT) and Operational...
BSidesLV24 – HireGround – Behavioral Interviewee-ing: Inverting the Corporate Interview to Get You Hired – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – HireGround – Behavioral Interviewee-ing: Inverting the Corporate Interview to Get You Hired...
Chinese APT Pounces on Misdiagnosed RCE in Ivanti VPN Appliances – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Ivanti on Thursday rushed out documentation for a critical flaw in its Connect Secure VPN appliances and confirmed a related...