Source: www.infosecurity-magazine.com – Author: Automated traffic now accounts for the majority of activity on the web, with the share of bad bot traffic surging from 32%...
Month: April 2025
Organizations Found to Address Only 21% of GenAI-Related Vulnerabilities – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: Organizations remediate only 48% of all vulnerabilities with detected exploits, according to a new study by Pentesting-as-a-Service (PTaaS) firm Cobalt. This number...
LabHost Phishing Mastermind Sentenced to 8.5 Years – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: A Huddersfield man has been handed an eight-and-a-half-year sentence for masterminding what became one of the world’s largest phishing-as-a-service (PhaaS) platforms. Zak...
Insurance Firm Lemonade Says API Glitch Exposed Some Driver’s License Numbers – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Insurance firm Lemonade is notifying roughly 190,000 individuals that their driver’s license numbers were likely exposed due to a technical...
Kidney Dialysis Services Provider DaVita Hit by Ransomware – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Kidney dialysis services provider DaVita said it fell victim to a ransomware attack over the weekend that disrupted some of...
Conduent Says Names, Social Security Numbers Stolen in Cyberattack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Business services provider Conduent has notified the Securities and Exchange Commission (SEC) that personal information was stolen in a disruptive...
2.6 Million Impacted by Landmark Admin, Young Consulting Data Breaches – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire More than 2.6 million individuals were impacted by two data breaches at insurance administrator Landmark Admin and software solutions provider...
China Pursuing 3 Alleged US Operatives Over Cyberattacks During Asian Games – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press China said Tuesday it is pursuing three alleged U.S. operatives accused of carrying out cyberattacks on Chinese infrastructure during the...
Blockchain, Quantum, and IoT Firms Unite to Secure Satellite Communications Against Quantum Threats – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Three different companies from three separate continents have agreed a memorandum of understanding to advance secure communications by combining their...
NetRise Raises $10 Million to Grow Software Supply Chain Security Platform – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Software supply chain security provider NetRise has raised $10 million in a Series A funding round that brings the total...
Hertz Discloses Data Breach Linked to Cleo Hack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Car rental giant Hertz Corporation is notifying customers of the Hertz, Thrifty, and Dollar brands that their personal information was...
AI Code Tools Widely Hallucinate Packages – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...
Threat Intel Firm Offers Crypto in Exchange for Dark Web Accounts – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have...
My Take: Is Amazon’s Alexa+ a Gutenberg moment — or a corporate rerun of history’s greatest co-opt? – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido Last Friday morning, April 11, I was making my way home from NTT Research’s Upgrade 2025 innovation...
Agentic AI is both boon and bane for security pros – Source: www.csoonline.com
Source: www.csoonline.com – Author: AI agents are predicted to reduce time to exploit by half in two years, here is what you need to know to...
OT-Security: Warum der Blick auf Open Source lohnt – Source: www.csoonline.com
Source: www.csoonline.com – Author: Kommerzielle OT-Security-Lösungen können hohe Kosten verursachen. Lesen Sie, welche Alternativen es gibt. Auch im OT-Security-Bereich stellen Open-Source-Lösungen eine kostengünstige Alternative zu kommerziellen...
Kritik an OpenAI: Experten warnen vor verkürzten Sicherheitstests – Source: www.csoonline.com
Source: www.csoonline.com – Author: Tester behaupten, dass OpenAI neuere KI-Modelle mit deutlich verkürzter Testzeit auf den Markt bringt. OpenAI hat offenbar seine Sicherheitstests verkürzt. JarTee –...
Arab American Women in Engineering: Meet Amar Dabaja
Get to know Amar Dabaja, a SWE member who designs automotive crash detection and airbag control modules. Source Views: 1
Women Engineers in Tunisia: Data and Representation
Prof. Lilia Labidi and engineer Besma Wchir share the state of women engineers in Tunisia, including data, historical context, and women who are making an impact...
How to Use LastPass Password Manager – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Staff We may earn from vendors via affiliate links or sponsorships. This might affect product placement on our site, but not...
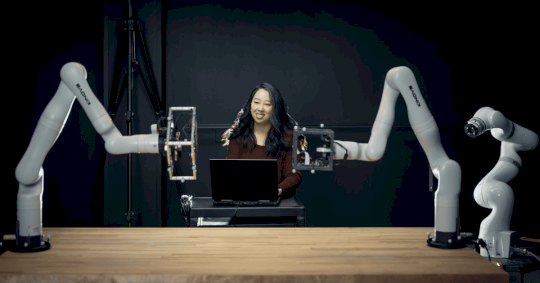
“No Education is Wasted”: How Erin Hong Did a 180 Into Aerospace Engineering
Discover how Erin Hong’s unique education and work experience shaped her engineering journey, along with her networking tips and mantra for success. Source Views: 3
Meet the GradSWE Affinity Group
Each month throughout the year, we’ll be spotlighting a SWE Affinity Group. We are excited to highlight SWE’s GradSWE Community Affinity Group! Source Views: 1
SWE Diverse Podcast Ep 224: Medical Technology Roundtable with Smith+Nephew
Learn about the medical technology field and the mentoring opportunities at Smith+Nephew in this roundtable discussion on Diverse: a SWE podcast! Source Views: 3
SWE UCLA Virtual Conference Helps Over 250 Women Break Barriers in STEM
The Program Development Grant (PDG) Committee provides opportunities for Society of Women Engineers (SWE) groups to receive money to host outreach and professional development events. Source...
SWE Weighs in With White House on Federal STEM Education Plan
SWE’s advocacy team met with leaders at the White House’s Office of Science and Technology Policy about efforts to update the Five-Year Federal STEM Education Plan....
SWE Senate Spotlight: Learn About the Senator Role
Interested in taking on a leadership role in the SWE Senate? Learn about the role of Senator in our interview with these current and past SWE...
Test SBX – Source: securityboulevard.com
Source: securityboulevard.com – Author: Greg Yarnold Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2025/04/test-sbx/?utm_source=rss&utm_medium=rss&utm_campaign=test-sbx Category & Tags: Social – X –...
test-SB3 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Greg Yarnold Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2025/04/test-sb3/?utm_source=rss&utm_medium=rss&utm_campaign=test-sb3 Category & Tags: Social – X –...
Inside IETF Bangkok: Shaping the Future of Workload Identity and Access Management – Source: securityboulevard.com
Source: securityboulevard.com – Author: Andrew McCormick The other thing that struck me was how many working groups there are and the interconnected relationships between them. I...
Beyond Schema Enforcement: Imperva’s Approach to Delivering Holistic API Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lebin Cheng API security is gaining attention, yet many organizations struggle to move from identifying risks to mitigating them effectively. In their...