Source: www.csoonline.com – Author: Eine aktuelle Studie offenbart: Ohne angemessene Datensicherheitskontrollen macht generative künstliche Intelligenz (GenAI) Mitarbeiter zu unbeabsichtigten Insider-Bedrohungen. Viele Unternehmen haben nicht auf dem...
Month: March 2025
VMware plugs a high-risk vulnerability affecting its Windows-based virtualization – Source: www.csoonline.com
Source: www.csoonline.com – Author: Improper access control issues in VMware Tools for Windows could allow privilege escalation on affected virtual machines. Broadcom is warning customers of...
Identity security: A critical defense in 2025’s threat landscape – Source: securityboulevard.com
Source: securityboulevard.com – Author: Gerry Gebel Trends in identity security for 2025 Managing multiple IDPs becomes the new normal The days of relying on a single...
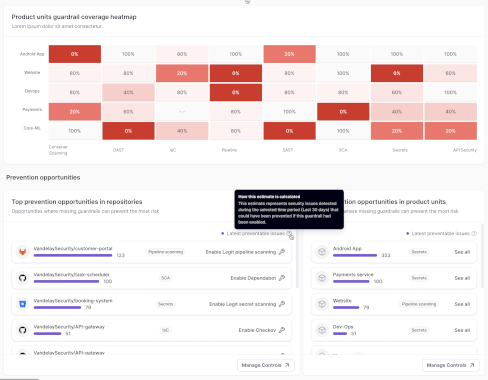
Legit Announces New Vulnerability Prevention Capabilities – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dan Mandel Get details on Legit’s new capabilities that allow AppSec teams to prevent introducing vulnerabilities.. Software development, accelerated by AI, continues...
Which frameworks assist in ensuring compliance for NHIs? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Why Compliance Frameworks are Crucial for NHIs? Could the answer to your organization’s cybersecurity woes lie in Non-Human Identities (NHIs)?...
How can I align our NHI management with GDPR and other standards? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Is Your NHI Management GDPR Compliant? It isn’t just humans who have identities, but machines as well. In-depth understanding and...
Generative AI: threat or opportunity? It depends on your adaptive speed! – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alon Yavin Now that AI reasoning capabilities are blasting and becoming accessible, folks tend to argue that generative AI will bring us...
Broadcom Extends Scope of VMware vDefend Cybersecurity Platform – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard Broadcom today updated its VMware vDefend platform to add additional security intelligence capabilities along with a streamlined ability to micro-segment...
MailChimp Under Attack: How Cybercriminals Are Exploiting Email Marketing Platforms – Source: securityboulevard.com
Source: securityboulevard.com – Author: Laura Bruck At Constella, we’ve spent years analyzing how cybercriminals execute attacks that affect organizations of all sizes, whether they’re startups, local...
BSidesLV24 – IATC – Difficult Conversations – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – IATC – Difficult Conversations Author/Presenter: Andrea M. Matwyshyn Our sincere appreciation to...
ADAMnetworks Licensed Technology Partner (LTP) Program – Source: securityboulevard.com
Source: securityboulevard.com – Author: adam_frans ADAMnetworks Licensed Technology Partner (LTP) Program Empowering MSPs, MSSPs & MDR Providers with Next-Gen Zero Trust Security In today’s threat-filled digital...
Snow White — Beware the Bad Apple in the Torrent – Source: securityboulevard.com
Source: securityboulevard.com – Author: Veriti Research As the new Snow White movie arrives in theaters with lackluster audience attendance (source), the absence of streaming options on...
Update VMware Tools for Windows Now: High-Severity Flaw Lets Hackers Bypass Authentication – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Fiona Jackson CVE-2025-22230 is described as an “authentication bypass vulnerability” by Broadcom, allowing hackers to perform high-privilege operations without the necessary credentials....
Security Expert Troy Hunt Lured in by Mailchimp Phish – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have...
Cybersecurity Gaps Leave Doors Wide Open – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...
‘Lucid’ Phishing-as-a-Service Exploits Faults in iMessage, Android RCS – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...
Beyond STIX: Next-Level Cyber-Threat Intelligence – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ryan Hohimer, Jans Aasman Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...
New Testing Framework Helps Evaluate Sandboxes – Source: www.darkreading.com
Source: www.darkreading.com – Author: Arielle Waldman Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
Google Hastily Patches Chrome Zero-Day Exploited by APT – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...
Security Tech That Can Make a Difference During an Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...
AI Data Poisoning – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Cloudflare has a new feature—available to free users as well—that uses AI to generate random pages to feed to AI...
GUEST ESSAY: The case for making real-time business continuity a frontline cybersecurity priority – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Chao Cheng-Shorland It starts with a ripple of confusion, then panic. Hospital systems freeze mid-procedure. Electronic medical records become inaccessible....
News alert: RSAC 2025 ramps up – watch Byron Acohido on Bospar’s Politely Pushy podcast – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido The annual pilgrimage to San Francisco for RSA Conference is fast approaching—and the ramp-up has officially begun....
News alert: IDT Corp., AccuKnox partner to deploy runtime security-powered CNAPP at the edge of IoT – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: cybernewswire FinTech and Communications Leader, IDT Corporation partners with AccuKnox to deploy runtime security-powered CNAPP (Cloud Native Application Protection Platform) for IoT/Edge...
Generative AI In Business: Managing Risks in The Race for Innovation – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Artificial intelligence has emerged as a game-changing force, with record amounts of funding fueling new innovations that are transforming industries...
Rethinking SAP Security Without Maintenance Contracts – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Do you rely on SAP maintenance contracts to keep vulnerabilities in check? Here’s a question: have you felt the sting...
macOS Users Warned of New Versions of ReaderUpdate Malware – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The threat actors behind the macOS malware loader known as ReaderUpdate have built new versions of the threat using the...
Critical Next.js Vulnerability in Hacker Crosshairs – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The first attempts to exploit a critical-severity vulnerability in Next.js have been observed less than a week after patches were...
Security Firms Say Evidence Seems to Confirm Oracle Cloud Hack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Oracle has categorically denied that its Cloud systems have been breached, but sample data made available by the hacker seems...
Google Patches Chrome Sandbox Escape Zero-Day Caught by Kaspersky – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Google late Tuesday rushed out a patch for a sandbox escape in its flagship Chrome browser after researchers at Kaspersky...