Source: www.securityweek.com – Author: Eduard Kovacs Scans show that tens of thousands of VMware ESXi instances are affected by the vulnerabilities disclosed recently as zero-days. On...
Month: March 2025
Indictments of Chinese Cyber Spies Reveal Hacker-For-Hire Operation – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The indictments this week of 12 Chinese nationals accused of hacking into computer systems of an array of individuals and...
How can NHIs be incorporated into our overall security strategy? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Do Non-Human Identities Play a Significant Role in Our Security Strategy? Indeed, they do. Non-Human Identities (NHIs) are becoming increasingly...
What are the key security controls for NHIs at the executive level? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Why Should CISOs Consider Non-Human Identities Security Controls? Did you know NHIs represent a significant portion of all entities in...
What role do NHIs play in our organization’s security posture? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn What Essential Role Do Non-Human Identities (NHIs) Play in Our Organization’s Security Posture? When our world increasingly moves towards digitalization,...
How can I align NHI management with our digital transformation initiatives? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Why is Non-Human Identities Management Critical for Digital Transformation? Have you ever considered the sheer quantity of non-human identities (NHIs)...
What Is Data Leak Prevention? Benefits and Best Practices – Source: securityboulevard.com
Source: securityboulevard.com – Author: Legit Security Today’s organizations work with incredible quantities of data. From corporate trade secrets to customers’ and employees’ personal information, much of...
What Is an Identity Provider (IdP) and How Does It Work? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Legit Security Managing online accounts shouldn’t feel like a chore. But when so many websites and systems require credentials, it’s hard to...
Patch Management Guide: Benefits and Best Practices – Source: securityboulevard.com
Source: securityboulevard.com – Author: Legit Security Developers periodically review software and release patches to remedy any bugs. When patches happen often, they can be hard to...
DEF CON 32 – War Stories – Hacking Millions Of Modems And Investigating Who Hacked My Modem – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Home » Security Bloggers Network » DEF CON 32 – War Stories – Hacking Millions Of Modems And Investigating Who...
Votiro’s Proven Protection: Retroscan for Zero-Day Threats – Source: securityboulevard.com
Source: securityboulevard.com – Author: Votiro On any given day, a seemingly harmless file may enter your organization, sometimes via your email system, bypassing every layer of...
Who is the DOGE and X Technician Branden Spikes? – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs At 49, Branden Spikes isn’t just one of the oldest technologists who has been involved in Elon Musk’s Department of Government...
Chinese APT Silk Typhoon exploits IT supply chain weaknesses for initial access – Source: www.csoonline.com
Source: www.csoonline.com – Author: News Analysis 06 Mar 20256 mins Advanced Persistent ThreatsGovernmentHacker Groups The threat group’s tactics mark a shift from direct exploits to lateral...
Hackerangriff auf Stadtwerke Schwerte – Source: www.csoonline.com
Source: www.csoonline.com – Author: Die Stadt Schwerte ist Opfer einer Cyberattacke. Auch Bürgerdienste sind betroffen. Aufgrund einer Cyberattacke auf die Stadtwerke Schwerte sind aktuell einige Dienste...
US charges 12 Chinese hackers in major government-backed espionage campaign – Source: www.csoonline.com
Source: www.csoonline.com – Author: Justice Department unveils indictments against Silk Typhoon group members, seizes domains in escalating cybersecurity standoff. US authorities have announced criminal charges against...
Badbox Android botnet disrupted through coordinated threat hunting – Source: www.csoonline.com
Source: www.csoonline.com – Author: Human Security, in collaboration with Google, Shadowserver and others, has sinkholed C2 operations affecting 500,000 infected machines. Badbox, the notorious Android malware...
Access Management Systems sind offene Türen für Hacker – Source: www.csoonline.com
Source: www.csoonline.com – Author: Falsch konfigurierte Zugangsverwaltungssysteme stellen für Unternehmen ein hohes Sicherheitsrisiko dar. Wenn Hacker biometrische Zugangsdaten erbeuten, können Sie erhebliche Schäden anrichten. shuttertsock –...
60% of cybersecurity pros looking to change employers – Source: www.csoonline.com
Source: www.csoonline.com – Author: High salaries are not enough to discourage cybersecurity workers — including functional leaders — from keeping an eye out for better jobs...
The risks of standing down: Why halting US cyber ops against Russia erodes deterrence – Source: www.csoonline.com
Source: www.csoonline.com – Author: Opinion 06 Mar 20258 mins Advanced Persistent ThreatsCSO and CISOThreat and Vulnerability Management The threat from Russian bad actors is real; if...
Smashing Security podcast #407: HP’s hold music, and human trafficking – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Skip to content Journey with us to Myanmar’s shadowy scam factories, where trafficked workers are forced to run romance-baiting and...
DoJ Busts Alleged Global Hacking-for-Hire Network of ‘Cyber Mercenaries’ – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Fiona Jackson Image: BirgitKorber, Getty Images/iStockphoto The Justice Department has charged 12 Chinese nationals for their alleged involvement in global hacker-for-hire activities....
Save 70% on a Course Showing You How to Invest in Crypto – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Academy Published March 6, 2025 We may earn from vendors via affiliate links or sponsorships. This might affect product placement on...
Trojans disguised as AI: Cybercriminals exploit DeepSeek’s popularity – Source: securelist.com
Source: securelist.com – Author: Vladislav Tushkanov, Vasily Kolesnikov, Oleg Kupreev, Denis Sitchikhin, Alexander Kryazhev Introduction Among the most significant events in the AI world in early...
Women Faced the Brunt of Cybersecurity Cutbacks in 2024 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have...
Enterprise AI Through a Data Security Lens: Balancing Productivity With Safety – Source: www.darkreading.com
Source: www.darkreading.com – Author: Adam Strange Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
CISA Cuts: A Dangerous Gamble in a Dangerous World – Source: www.darkreading.com
Source: www.darkreading.com – Author: Steve Durbin Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
Deepfake Videos of YouTube CEO Phish Creators – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have...
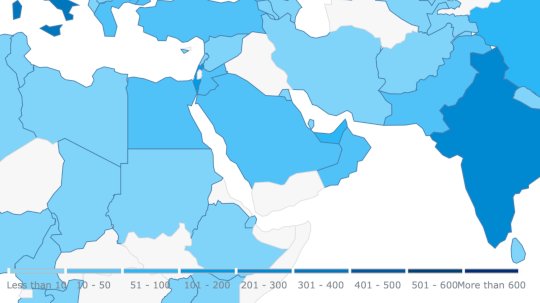
Ransomware Attacks Build Against Saudi Construction Firms – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...
Cybersecurity’s Future Is All About Governance, Not More Tools – Source: www.darkreading.com
Source: www.darkreading.com – Author: Shirley Salzman Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
Espionage Actor ‘Lotus Blossom’ Targets Southeast Asia – Source: www.darkreading.com
Source: www.darkreading.com – Author: Alexander Culafi, Senior News Writer, Dark Reading Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why...