Source: securelist.com – Author: Giampaolo Dedola, Vasily Berdnikov Last year, we published an article about SideWinder, a highly prolific APT group whose primary targets have been...
Month: March 2025
‘Spearwing’ RaaS Group Ruffles Feathers in Cyber-Threat Scene – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have...
SWE Diverse Podcast Ep 244: Overcoming Stress and Burnout in Engineering
Hear the stories of two women engineers who have found unique ways to navigate imposter syndrome, stress and burnout in this episode of Diverse: a SWE...
What are the cost implications of advanced NHI protection? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn What is the True Cost of Not Investing in Non-Human Identities Protection? Non-Human Identities (NHIs) are increasingly significant where automated...
How do I measure the effectiveness of our NHI security measures? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn A Perplexing Dilemma or a Solvable Query? Have you ever puzzled over how to measure the effectiveness of Non-Human Identities...
BSides Exeter 2024 – Keynote: Matt Broomhall & Richard DeVere – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Promo » Cybersecurity » BSides Exeter 2024 – Keynote: Matt Broomhall & Richard DeVere by...
How can NHI risks be reduced without compromising system performance? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Are your Non-Human Identities (NHIs) and Secrets effectively managed? NHIs and Secrets have emerged as crucial elements. However, the question...
BSides Exeter 2024 – Keynote: Flushing Away Preconceptions Of Risk – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Promo » Cybersecurity » BSides Exeter 2024 – Keynote: Flushing Away Preconceptions Of Risk by...
New AI Protection from Google Cloud Tackles AI Risks, Threats, and Compliance – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Google Cloud has announced AI Protection, a comprehensive solution to protect risk to, and threats within, the use of generative...
Cruel And Vindictive By Design – Source: securityboulevard.com
Source: securityboulevard.com – Author: hrbrmstr (This post originally published on 47 Watch) Recent administrative changes at the Social Security Administration (SSA) reveal a concerning pattern of...
Medusa Ransomware Attacks Increase – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The number of Medusa ransomware attacks has been steadily increasing over the past two years and doubled in the first...
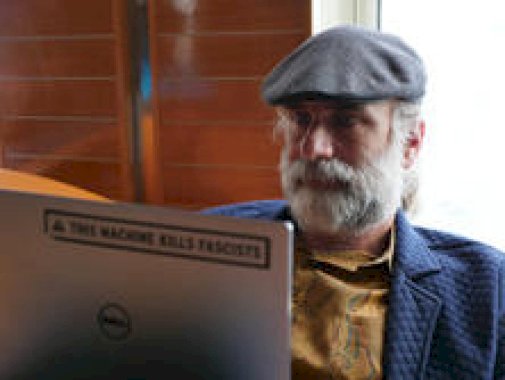
Friday Squid Blogging: Squid Loyalty Cards – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier About Bruce Schneier I am a public-interest technologist, working at the intersection of security, technology, and people. I’ve been writing...
Rayhunter: Device to Detect Cellular Surveillance – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Clive Robinson • March 7, 2025 2:39 PM @ Bruce, ALL, With regards “It runs on a $20 mobile hotspot.”...
Women Are Breaking Into Cybersecurity, But Losing Jobs Faster Than Men – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Fiona Jackson In 2024, women accounted for 22% of global security teams on average, compared to 17% in 2023, according to ISC2....
‘Spearwing’ RaaS Group Ruffles Feathers in Cyber Threat Scene – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have...
MITRE EMB3D for OT & ICS Threat Modeling Takes Flight – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...
Static Scans, Red Teams, and Frameworks Aim to Find Bad AI Models – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...
Cybercrime’s Cobalt Strike Use Plummets 80% Worldwide – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...
Zero-Days Put Tens of 1,000s of Orgs at Risk for VM Escape Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Rob Wright Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
Taylor Swift Ticket Thieves Charged in Court for Resale Operation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have...
How Cyberattacks Affect Your Staff – Source: www.darkreading.com
Source: www.darkreading.com – Author: Chris Butler Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
US Seize Garantex in Cryptocurrency Money Laundering Bust – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine The US Justice Department on Friday announced the seizure of the online infrastructure used to run Garantex, a major cryptocurrency...
In Other News: EntrySign AMD Flaw, Massive Attack Targets ISPs, ENISA Report – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News SecurityWeek’s cybersecurity news roundup provides a concise compilation of noteworthy stories that might have slipped under the radar. We provide...
Edimax Camera Zero-Day Disclosed by CISA Exploited by Botnets – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Multiple botnets are exploiting an Edimax IP camera vulnerability whose existence was disclosed this week by the cybersecurity agency CISA,...
FBI: Fake Ransomware Attack Claims Sent to US Executives via Snail Mail – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Over the past two weeks, corporate executives at various US organizations, primarily in the healthcare sector, have been targeted in...
Microsoft Says One Million Devices Impacted by Infostealer Campaign – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Newly one million devices have been impacted by a malvertising campaign redirecting users to information stealer malware hosted on GitHub,...
Cyberattack Disrupts National Presto Industries Operations – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Home appliance maker National Presto Industries is scrambling to restore operations disrupted by a cyberattack that caused a system outage....
18,000 Organizations Impacted by NTT Com Data Breach – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Japanese information and communication technology (ICT) provider NTT Communications Corporation (NTT Com) has disclosed a data breach impacting nearly 18,000...
Many Schools Report Data Breach After Retirement Services Firm Hit by Ransomware – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Dozens of school districts and thousands of individuals in the United States are impacted by a data breach resulting from...
How do I prioritize NHI risks in boardroom discussions? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Why is Risk Prioritization of Non-Human Identities Essential in Boardroom Discussions? Cybersecurity continues to command greater attention in organizational hierarchies,...