Source: www.cyberdefensemagazine.com – Author: News team What if the smart thermostat in your home decides that winter is the perfect time for you to experience tropical...
Month: March 2025
Fast 1 Million Geschäfts- und Privat-PCs kompromittiert – Source: www.csoonline.com
Source: www.csoonline.com – Author: Privat illegale Streams anzuschauen gefährdet auch Unternehmen. Häufig nutzen Hacker Werbebanner, um verschiedenste Devices mit Malware zu infizieren. Ein Bericht von Microsoft...
The most notorious and damaging ransomware of all time – Source: www.csoonline.com
Source: www.csoonline.com – Author: Ransomware has a long history, dating back to the late 1980s. This past year, it generated $811 millions in payments to the criminal...
CIOs and CISOs take on NIS2: Key challenges, security opportunities – Source: www.csoonline.com
Source: www.csoonline.com – Author: Between complexity, bureaucracy, and costs, NIS2 compliance has been a challenging journey for many IT leaders — and one that isn’t over....
KI-gestützte Angriffe machen deutschen Betrieben zu schaffen – Source: www.csoonline.com
Source: www.csoonline.com – Author: Während Hacker bereits auf breiter Front KI-gestützte Angriffe fahren, tun sich viele Unternehmen schwer, den neuen Gefahren zu begegnen. Während Hacker KI...
Australian financial firm hit with lawsuit after massive data breach – Source: www.csoonline.com
Source: www.csoonline.com – Author: News 13 Mar 20253 mins Data BreachRegulationSecurity Practices The industry regulator alleges that FIIG Securities failed to maintain adequate cybersecurity measures for...
GitHub to unbundle Advanced Security – Source: www.infoworld.com
Source: www.infoworld.com – Author: GitHub announced plans to unbundle its GitHub Advanced Security (GHAS) product, breaking it up into two standalone products: GitHub Secret Protection and...
OBSCURE#BAT Malware Highlights Risks of API Hooking – Source: www.darkreading.com
Source: www.darkreading.com – Author: Rob Wright Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
FBI, CISA Raise Alarms As Medusa Ransomware Attacks Grow – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have...
Car Exploit Allows You to Spy on Drivers in Real Time – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...
Salt Typhoon: A Wake-up Call for Critical Infrastructure – Source: www.darkreading.com
Source: www.darkreading.com – Author: Gabrielle Hempel Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
Speedify VPN Review 2025: Features, Security, and Performance – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares Speedify VPN fast facts Our rating: 3.1 stars out of 5.00 Pricing: Starts at $7.49 per month Key features: Dedicated...
News alert: Aptori’s AI-driven platform reduces risk, ensures compliance — now on Google Marketplace – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: cybernewswire San Jose, Calif., Mar. 12, 2025, CyberNewswire — Aptori, a leader in AI-driven application security, today announced the launch of its...
What role do APIs play in automating NHI management? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Could API Automation Be The Missing Piece In Your NHI Management? One critical question stands out: Could the underutilized potential...
What security considerations should I keep in mind for NHI automation? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Why are Security Considerations Essential for Non-Human Identities Automation? The age of automation has dawned upon us. Automation carries the...
How can I integrate automated NHI auditing into our pipeline? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn How Can Automated NHI Auditing Enhance Your Cybersecurity Strategy? Is your organization struggling with managing the ever-increasing volume of Non-Human...
5 Ways to Prepare Your Data Estate for Copilot Adoption and Agentic AI – Source: securityboulevard.com
Source: securityboulevard.com – Author: Claude Mandy AI Copilots and Agentic AI (those capable of independently taking actions to achieve specified goals) remain the talk of the...
Response to CISA Advisory (AA25-071A): #StopRansomware: Medusa Ransomware – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ayelen Torello On March 12, 2025, The Federal Bureau of Investigation (FBI), Cybersecurity and Infrastructure Security Agency (CISA), and the Multi-State Information...
BSides Exeter 2024 – Blue Track – DFIR – Are We There Yet? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Promo » Cybersecurity » BSides Exeter 2024 – Blue Track – DFIR – Are We...
SafeBreach Coverage for US CERT AA25-071A (Medusa Ransomware) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tova Dvorin On March 12, 2025, the Cybersecurity and Infrastructure Security Agency (CISA), in collaboration with the Federal Bureau of Investigation (FBI)...
AD Lite Password Auditor Report: Key Insights and Data – Source: securityboulevard.com
Source: securityboulevard.com – Author: Enzoic 2024 Enzoic AD Lite Password Auditor Report In an era where cyber threats continue to evolve, password security remains one of...
Randall Munroe’s XKCD ‘Water Damage’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Friday, March 14, 2025 Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News...
Silk Typhoon Targeting IT Supply Chains and Network Devices, Microsoft Reports – Source: securityboulevard.com
Source: securityboulevard.com – Author: Chris Garland Microsoft Threat Intelligence has issued new reporting about tactics being used by Silk Typhoon (also called APT27 or HAFNIUM by...
Unpatched Edimax Camera Flaw Exploited Since at Least May 2024 – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs A recently disclosed zero-day affecting Edimax devices has been exploited in the wild since at least May 2024, according to...
FreeType Zero-Day Being Exploited in the Wild – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Meta’s Facebook security team has raised an alarm after spotting live exploitation of a zero-day vulnerability in the widely used...
Cisco Patches 10 Vulnerabilities in IOS XR – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Cisco on Wednesday announced patches for 10 vulnerabilities in IOS XR, including five that could be exploited to cause denial-of-service...
Grafana Flaws Likely Targeted in Broad SSRF Exploitation Campaign – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Grafana path traversal vulnerabilities have been exploited prior to a broad campaign targeting server-side request forgery (SSRF) bugs in multiple...
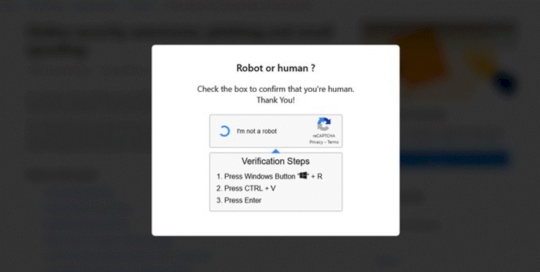
Microsoft Warns of Hospitality Sector Attacks Involving ClickFix – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs A cybercrime group has been targeting organizations in the hospitality sector in attacks involving fake Booking.com emails and the use...
DeepSeek’s Malware-Generation Capabilities Put to Test – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Researchers at security firm Tenable have analyzed the ability of the Chinese gen-AI DeepSeek to develop malware such as keyloggers...
North Korean Hackers Distributed Android Spyware via Google Play – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A North Korean APT actor has been targeting Korean and English-speaking users with an Android surveillance tool distributed via Google...