Source: www.govinfosecurity.com – Author: Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Social Engineering Phishing Emails Impersonating Eset Target Cybersecurity Professionals With Malware Chris...
Year: 2024
BianLian Ransomware Gang Claims Heist of Pediatric Data – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Fraud Management & Cybercrime , Healthcare , Industry Specific Boston Children’s Health Physicians Says Incident Involved Unnamed IT Vendor Marianne Kolbasuk McGee...
MacOS Safari ‘HM Surf’ Exploit Exposes Camera, Mic, Browser Data – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Delphotos via Alamy Stock Photo A security weakness in the Safari browser on macOS devices might have...
BlackBerry Cuts Cylance Spend to Focus on Profitable Areas – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Endpoint Protection Platforms (EPP) , Endpoint Security , Managed Detection & Response (MDR) Company Shifts Cyber Focus to QNX and Secure Communications...
North Korean IT Scam Workers Shift to Extortion Tactics – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Governance & Risk Management Report Reveals North Korean Workers Expanding into Intellectual...
Hacker Poses as Israeli Security Vendor to Deliver Wiper – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Social Engineering Phishing Emails Impersonating Eset Target Cybersecurity Professionals With Malware Chris...
BianLian Ransomware Gang Claims Heist of Pediatric Data – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Fraud Management & Cybercrime , Healthcare , Industry Specific Boston Children’s Health Physicians Says Incident Involved Unnamed IT Vendor Marianne Kolbasuk McGee...
Live Webinar | Old-School Awareness Training Does Not Hack It Anymore – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: CISO Trainings , Information Sharing , Leadership & Executive Communication Live Webinar | Old-School Awareness Training Does Not Hack It Anymore Presented...
Can You Fax a Check? Yes. Follow These Steps to Do it Safely – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Corry Cummings There are probably a dozen ways of sending money that are easier than faxing a check. Even so, it is...
Microsoft: Ransomware Attacks Growing More Dangerous, Complex – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse The number of attempted ransomware attacks on Microsoft customers globally have grown dramatically in the last year, according to Microsoft’s...
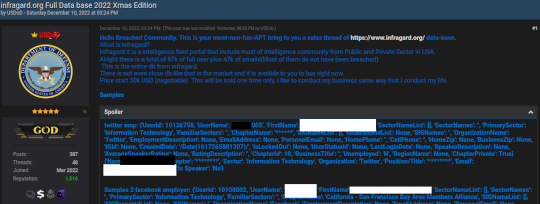
Brazil Arrests ‘USDoD,’ Hacker in FBI Infragard Breach – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs Brazilian authorities reportedly have arrested a 33-year-old man on suspicion of being “USDoD,” a prolific cybercriminal who rose to infamy in...
Get an Untrusted Security Advisor! Have Fun, Reduce Fail! – Source: securityboulevard.com
Source: securityboulevard.com – Author: Anton Chuvakin Many organizations are looking for trusted advisors, and this applies to our beloved domain of cyber/information security. If you look...
Is End-User Cybersecurity Training Useless? Spoiler Alert: It’s Not! – Source: securityboulevard.com
Source: securityboulevard.com – Author: hmeyers Chris Clements, VP of Solutions Architecture October 18, 2024 Because of the frequency of phishing attacks landing in user mailboxes and...
USENIX NSDI ’24 – MESSI: Behavioral Testing of BGP Implementations – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters:Rathin Singha, Rajdeep Mondal, Ryan Beckett, Siva Kesava Reddy Kakarla, Todd Millstein, George Varghese Our sincere thanks to USENIX, and...
AI-Generated Personas: Trust and Deception – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Michael Berry And the Ethical Dilemma of Using AI to Create Fake Online Personalities In recent years, advancements in artificial intelligence...
Daniel Stori’s Turnoff.US: ‘bash-gptl’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the inimitable Daniel Stori at Turnoff.US! Permalink *** This is a Security Bloggers Network syndicated blog from Infosecurity.US authored...
USENIX NSDI ’24 – Netcastle: Network Infrastructure Testing At Scale – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters:Rob Sherwood, Jinghao Shi, Ying Zhang, Neil Spring, Srikanth Sundaresan, Jasmeet Bagga, Prathyusha Peddi, Vineela Kukkadapu, Rashmi Shrivastava, Manikantan KR,...
The transformation of open source: Lessons from the past decade – Source: securityboulevard.com
Source: securityboulevard.com – Author: Aaron Linskens Over the past decade, the world of open source software has undergone a seismic transformation, both in terms of its...
Celebrating Excellence in Financial Services – Source: securityboulevard.com
Source: securityboulevard.com – Author: Thomas Stoesser Like most businesses, banks are facing a highly competitive future built on digital services. To succeed, they must modernize their...
Army Cloud Program to Help SMBs Meet DoD Cyber Requirements – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The U.S. Army is building a secure cloud environment that small businesses can use to meet increasingly stringent military cybersecurity...
Cybersecurity Snapshot: Tenable Report Warns About Toxic Cloud Exposures, as PwC Study Urges C-Suite Collaboration for Stronger Cyber Resilience – Source: securityboulevard.com
Source: securityboulevard.com – Author: Juan Perez Check out invaluable cloud security insights and recommendations from the “Tenable Cloud Risk Report 2024.” Plus, a PwC study says...
AI-Powered Fraud Detection Systems for Enhanced Cybersecurity – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Artificial intelligence (AI) has many applications in cybersecurity. Automated fraud detection is one of the most impactful of these use...
From Raw Data to Rough Drafts: The Entrepreneurial Journey of Two Engineers-Turned-Bestselling Authors
As part of the Entrepreneurs AG’s spotlight month, read more about the intersection of engineering and authorship. Views: 1
Friday Squid Blogging: Squid Scarf – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier About Bruce Schneier I am a public-interest technologist, working at the intersection of security, technology, and people. I’ve been writing...
Justice Department Indicts Tech CEO for Falsifying Security Certifications – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog The Wall Street Journal is reporting that the CEO of a still unnamed company has been indicted for creating...
MEDUZASTEALER Detection: Hackers Distribute Malware Masquerading the Sender as Reserve+ Technical Support via Telegram Messaging Service – Source: socprime.com
Source: socprime.com – Author: Veronika Telychko Hard on the heels of a new wave of cyber-attacks by UAC-0050 involving cyber espionage and financial thefts and relying...
Microsoft: macOS Vulnerability Potentially Exploited in Adware Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Microsoft on Thursday warned of a recently patched macOS vulnerability potentially being exploited in adware attacks. The issue, tracked as...
In Other News: China Making Big Claims, ConfusedPilot AI Attack, Microsoft Security Log Issues – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News SecurityWeek’s cybersecurity news roundup provides a concise compilation of noteworthy stories that might have slipped under the radar. We provide...
North Korean APT Exploited IE Zero-Day in Supply Chain Attack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A North Korean threat actor has exploited a recent Internet Explorer zero-day vulnerability in a supply chain attack, threat intelligence...
Rising Tides: Christien “DilDog” Rioux on Building Privacy and What Makes Hackers Unique – Source: www.securityweek.com
Source: www.securityweek.com – Author: Jennifer Leggio Few things bring me more joy than this ongoing Rising Tides column, because I get to dig into the minds...