Source: securityboulevard.com – Author: mykola myroniuk In the previous posts, we explored the world of web pixels, uncovering potential privacy risks and highlighting the importance of...
Year: 2024
Comic Agilé – Mikkel Noe-Nygaard, Luxshan Ratnaravi – #318 — Working for a Big Consultancy – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the respected Software Engineering expertise of Mikkel Noe-Nygaard and the lauded Software Engineering / Enterprise Agile Coaching work of Luxshan Ratnaravi at Comic Agilé! Permalink *** This is a...
Detection Engineering: A Case Study – Source: securityboulevard.com
Source: securityboulevard.com – Author: C. J. May The battles between attackers and defenders get more sophisticated every day. Both sides are locked in a constant back-and-forth...
Canvas fingerprinting in the wild – Source: securityboulevard.com
Source: securityboulevard.com – Author: Sebastian Wallin Every day, your computer renders dozens of these without you even noticing. Strange patterns, colorful shapes, and emojis—what do you...
5 books I enjoyed in 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: j4vv4d Have you ever found yourself in a bookstore, overwhelmed by the sheer number of titles and unsure of where to start?...
DEF CON 32 – Using AI Computer Vision In Your OSINT Data Analysis – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Saturday, December 28, 2024 Home » Security Bloggers Network » DEF CON 32 – Using AI Computer Vision In Your...
Cybersecurity Snapshot: What Looms on Cyberland’s Horizon? Here’s What Tenable Experts Predict for 2025 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Juan Perez Wondering what cybersecurity trends will have the most impact in 2025? Check out six predictions from Tenable experts about cyber...
Keeper Password Manager Review (2025): Features, Pros, & Cons – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares Keeper fast facts Our rating: 4.4 stars out of 5 Pricing: Starts at $2.92 per month Key features Discounts for...
Casino Players Using Hidden Cameras for Cheating – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Casino Players Using Hidden Cameras for Cheating The basic strategy is to place a device with a hidden camera...
Friday Squid Blogging: Squid on Pizza – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier About Bruce Schneier I am a public-interest technologist, working at the intersection of security, technology, and people. I’ve been writing...
Threat landscape for industrial automation systems in Q3 2024 – Source: securelist.com
Source: securelist.com – Author: Kaspersky ICS CERT Statistics across all threats In the third quarter of 2024, the percentage of ICS computers on which malicious objects...
Strela Stealer Attack Detection: New Malware Variant Now Targets Ukraine Alongside Spain, Italy, and Germany – Source: socprime.com
Source: socprime.com – Author: Veronika Telychko Security experts have uncovered a novel Strela Stealer campaign, which leverages a new iteration of email credential-stealing malware. In this...
Reducing Kafka Lag: Optimizing Kafka Performance – Source: socprime.com
Source: socprime.com – Author: Oleksii K. Apache Kafka is a powerful distributed messaging system, but like any system, it can face performance bottlenecks. One of the...
KRaft: Apache Kafka Without ZooKeeper – Source: socprime.com
Source: socprime.com – Author: Oleksii K. Apache Kafka has been a cornerstone of modern event streaming architectures, enabling reliable and scalable data pipelines for businesses worldwide....
Hackers Are Hot for Water Utilities – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kelly Jackson Higgins, Editor-in-Chief, Dark Reading Source: Vyacheslav Lopatin via Alamy Stock Photo The unprecedented wave of high-profile cyberattacks on US water...
Defining & Defying Cybersecurity Staff Burnout – Source: www.darkreading.com
Source: www.darkreading.com – Author: Karen Spiegelman, Features Editor Source: Magdalena Iordache via Alamy Stock Photo “A quarter of cybersecurity leaders want to quit,” hollered the headline...
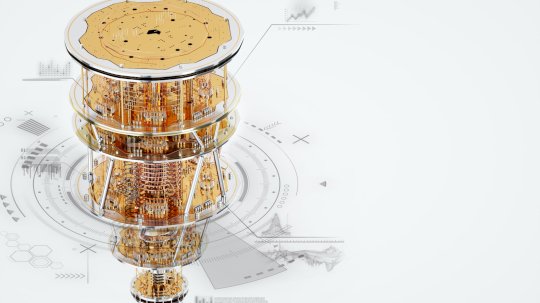
Quantum Computing Advances in 2024 Put Security In Spotlight – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Marko Aliaksandr via Shutterstock The quest to create a useful quantum computer reached a significant milestone at...
Data protection challenges abound as volumes surge and threats evolve – Source: www.csoonline.com
Source: www.csoonline.com – Author: Vast and growing data volumes and the shifting nature of threats are complicating the CISO’s job. Experts say a sound foundational risk...
Security-Awareness-Trainings – ein Ratgeber – Source: www.csoonline.com
Source: www.csoonline.com – Author: Security Awareness ist Pflicht, um Cyberrisiken zu minimieren. Lesen Sie, wie Ihre Belegschaft ein nachhaltiges Sicherheitsbewusstsein entwickelt. Wenn Ihre erste Verteidigungslinie fällt,...
Network problems delay flights at two oneworld Alliance airlines – Source: www.networkworld.com
Source: www.networkworld.com – Author: News Dec 26, 20243 mins DDoSNetworkingTransportation and Logistics Industry American Airlines flights were grounded for up to an hour on Dec. 24,...
The Intersection of AI and OSINT: Advanced Threats On The Horizon – Source: www.securityweek.com
Source: www.securityweek.com – Author: Stu Sjouwerman Intelligence operations have undergone a profound transformation. Gone are the days when intelligence gathering relied purely on information obtained from...
Defense Giant General Dynamics Says Employees Targeted in Phishing Attack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Aerospace and defense giant General Dynamics says threat actors compromised dozens of employee benefits accounts after a successful phishing campaign...
Cl0p Ransomware Group to Name Over 60 Victims of Cleo Attack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The notorious Cl0p ransomware group will soon name more than 60 organizations that were hacked recently through the exploitation of...
Japan Airlines Was Hit by a Cyberattack, Delaying Flights During the Year-End Holiday Season – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press Japan Airlines said it was hit by a cyberattack Thursday, causing delays to more than 20 domestic flights but the...
SaaS SIEM: Transforming Cybersecurity with Seceon’s Innovative ApproachSaaS SIEM – Source: securityboulevard.com
Source: securityboulevard.com – Author: karthik As organizations continue to shift toward digital-first operations, the demand for robust cybersecurity solutions has never been greater. Cyber threats are...
Best of 2024: The Best SIEM Tools To Consider in 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rebecca Kappel What is a SIEM? SIEM solutions enable enterprises to monitor and analyze security-related data from a variety of sources, such...
Achieving CISA BOD 25-01 Compliance and SCuBA Alignment – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tim Bach, SVP of Security Engineering, AppOmni The Cybersecurity and Infrastructure Security Agency’s (CISA) new Binding Operational Directive (BOD) 25-01 marks a...
A Year in Review: 2024’s Milestones That Propel Us into 2025 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Sunil Muralidhar As we close out 2024, we look back on what has truly been a banner year for ColorTokens—a year marked...
Top Cybersecurity Compliance Issues Businesses Face Today – Source: securityboulevard.com
Source: securityboulevard.com – Author: Assura Team As organizations increasingly rely on digital infrastructure, the stakes have never been higher. Cybersecurity compliance is necessary to safeguard sensitive...
Top Cyber Asset Attack Surface Management (CAASM) Tools for 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rebecca Kappel In today’s dynamic cybersecurity landscape, organizations face an ever-evolving threat environment where new vulnerabilities are continuously discovered, and attack surfaces...