Source: www.govinfosecurity.com – Author: Endpoint Security , Internet of Things Security Flaw in Embedded Device Operating System Allowed Hackers to Bypass Integrity Check Anviksha More (AnvikshaMore)...
Year: 2024
Hospital Notifies 316,000 of Breach in Christmas 2023 Hack – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Breach Notification , Fraud Management & Cybercrime , Healthcare Cybercriminal Gang ‘Money Message’ Claims Credit, Publishes Stolen Records Marianne Kolbasuk McGee (HealthInfoSec)...
More Than Bounty: Beating Burnout with Hacker-Powered Security – Source:www.hackerone.com
Source: www.hackerone.com – Author: johnk. A career in security is hardly dull or static. Nor would those attracted to the industry want it to be. On...
“CP3O” pleads guilty to multi-million dollar cryptomining scheme – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley A man faces up to 20 years in prison after pleading guilty to charges related to an illegal cryptomining operation...
3AM ransomware: what you need to know – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley What is 3AM? 3AM (also known as ThreeAM) is a ransomware group that first emerged in late 2023. Like other...
The AI Fix #28: Robot dogs with bombs, and who is David Mayer? – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Skip to content In episode 28 of The AI Fix, the new version of ChatGPT does a surprisingly good job...
AI-Driven Business Intelligence Solutions for Women Engineers
Jayashree Raja shares how women in engineering can find their place at the forefront of the AI revolution. Source Views: 1
SWE Diverse Podcast Ep 292: Becoming a Better Ally: Insights From Men in Engineering
Dive into allyship and learn actionable tips to support women in engineering at the professional and collegiate levels with members of the HeForSWE Affinity Group! Source...
Actively Exploited Zero-Day, Critical RCEs Lead Microsoft Patch Tuesday – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Zoonar GmbH via Alamy Stock Photo A Windows zero-day security vulnerability under active exploit...
‘Termite’ Ransomware Likely Behind Cleo Zero-Day Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: znakki via Shutteratock Ransomware group “Termite” — which recently claimed supply chain vendor Blue Yonder as a...
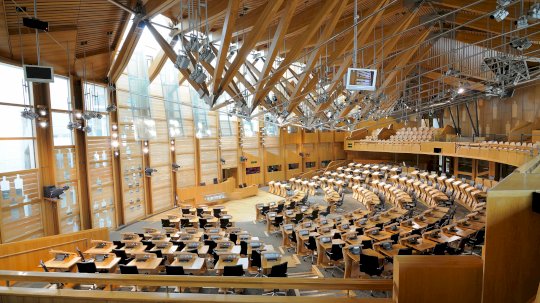
Scottish Parliament TV at Risk From Deepfakes – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Source: Norman Pogson via Alamy Stock Photo NEWS BRIEF Deepfakes are becoming a threat to recordings...
Cybercrime Gangs Abscond With Thousands of AWS Credentials – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: GK Images via Alamy Stock Photo Cybercriminal gangs have exploited vulnerabilities in public websites to steal Amazon...
Lessons From the Largest Software Supply Chain Incidents – Source: www.darkreading.com
Source: www.darkreading.com – Author: Eldan Ben-Haim Source: Zoonar GmbH via Alamy Stock Photo COMMENTARY In 2011, Marc Andreessen coined a phrase we’re now all familiar with:...
Google Launches Open Source Patch Validation Tool – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jennifer Lawinski Source: Art of Food via Alamy Stock Photo NEWS BRIEF Security updates in the Android ecosystem is a complex, multistage...
Staying Ahead: The Role of NHIDR in Modern Cybersecurity – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Why is NHIDR Crucial in Modern Cybersecurity? For organizations to stay ahead in this dynamic cybersecurity landscape, it’s imperative to...
Post-Quantum Cryptography: The Implications of Google’s Willow and Other Quantum Computers for Cybersecurity – Source: securityboulevard.com
Source: securityboulevard.com – Author: Paul Horn Quantum computing was long considered to be part of a distant future. However, it is quickly becoming a reality. Google’s...
Why software composition analysis is essential for open source security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Aaron Linskens Open source software security and dependency management have never been more critical, as organizations strive to protect their software supply...
Scam Kit Maker Rebuilding Business After Telegram Channel Shut Down – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt A prolific threat group that has been selling phishing scam kits that target more than 300 brands globally is working...
DEF CON 32 – Changing Global Threat Landscape – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Tuesday, December 10, 2024 Home » Security Bloggers Network » DEF CON 32 – Changing Global Threat Landscape Authors/Presenters: Rob...
Auguria Streamlines Management of Security Log Data – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard Auguria today at the Black Hat Europe conference, in addition to providing five additional integrations with other platforms, revealed it...
Comic Agilé – Mikkel Noe-Nygaard, Luxshan Ratnaravi – #315 – Stickies – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the respected Software Engineering expertise of Mikkel Noe-Nygaard and the lauded Software Engineering / Enterprise Agile Coaching work of Luxshan Ratnaravi at Comic Agilé! *** This is a Security...
Anton’s Security Blog Quarterly Q4 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Anton Chuvakin Amazingly, Medium has fixed the stats so my blog/podcast quarterly is back to life. As before, this covers both Anton...
GitGuardian Extends Reach to Manage Non-Human Identities – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard GitGuardian today extended the reach of its ability to manage applications secrets into the realm of non-human identities (NHI) associated...
Microsoft Challenge Will Test LLM Defenses Against Prompt Injections – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Microsoft is inviting teams of researchers to try to hack into a simulated large language model (LLM) integrated email client...
How to Enable and Manage AWS WAF Logging with CloudWatch Logs – Source: socprime.com
Source: socprime.com – Author: Comrade H. WRITTEN BY Comrade H. WAF Engineer [post-views] December 10, 2024 · 2 min read AWS WAF allows you to log...
Optimizing Elasticsearch Master Node for Cluster Stability – Source: socprime.com
Source: socprime.com – Author: Oleksandr L The master node is responsible for lightweight cluster-wide actions such as creating or deleting an index, tracking which nodes are...
Standard Logstash Template for Event Processing (Gold Template) – Source: socprime.com
Source: socprime.com – Author: Oleksandr L [post-views] December 10, 2024 · 3 min read This standard template for configuring Logstash pipelines, commonly referred to as a...
Configuring Disk Allocation Thresholds in Elasticsearch and OpenSearch – Source: socprime.com
Source: socprime.com – Author: Oleksii K. WRITTEN BY Oleksii K. DevOps Engineer [post-views] December 10, 2024 · 3 min read When running an Elasticsearch or OpenSearch...
Understanding index.mapping.total_fields.limit in OpenSearch/ElasticSearch – Source: socprime.com
Source: socprime.com – Author: Oleh P. WRITTEN BY Oleh P. SOC Engineer [post-views] December 10, 2024 · 2 min read Sometimes, you can get the associated...
Full-Face Masks to Frustrate Identification – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments Matthias Urlichs • December 10, 2024 7:20 AM They don’t survive in-person scrutinity, but video cameras? no contest....