The document provides guidance on implementing the ISO/IEC 27001 standard, which outlines requirements for an Information Security Management System (ISMS). It suggests merging certain documents within...
Year: 2024
India Repatriates Citizens Duped Into Forced Cyber Fraud Labor in Cambodia – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: sezer ozger via Alamy Stock Photo India’s embassy in Cambodia is working with officials there...
Collaboration Needed to Fight Ransomware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Brian Neuhaus 4 Min Read Source: Wavebreakmedia Ltd IFE-210813 via Alamy Stock Photo COMMENTARY The dramatic imagery of law enforcement “kicking down...
Africa Tackles Online Disinformation Campaigns During Major Election Year – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: CG Alex via Shutterstock A dramatic increase in online disinformation attacks against African nations and international agencies...
UN Adopts Resolution for ‘Secure, Trustworthy’ AI – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: imageBROKER.com GmbH & Co. KG via Alamy Stock Photo The United Nations on Thursday adopted a resolution...
Chinese State-Sponsored Hackers Charged, Sanctions Levied by US – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading Source: Rokas Tenys via Alamy Stock Photo The Department of Justice this week charged seven Chinese...
It’s Time to Stop Measuring Security in Absolutes – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Huber Robert Huber, Chief Security Officer at Tenable March 25, 2024 3 Min Read Source: Dzmitry Skazau via Alamy Stock Photo...
A Database-Oriented Operating System Wants to Shake Up Cloud Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: James Thew via Alamy Stock Photo Is it possible to replace Linux as the heart of serverless...
ISO/IEC 27001:2022 Self-assessment questionnaire
The document focuses on assessing readiness for ISO/IEC 27001:2022 Information Security Management System (ISMS) certification. It outlines key aspects such as determining external and internal issues...
IoT Security Architecture and Policy for the Home – a Hub Based Approach
Home IoT devices and systems need to manage security with minimal – and potentially no – consumer intervention, and without the consumer having any specialist knowledge...
INTELIGENCIA ARTIFICIAL Y CIBERSEGURIDAD
The guide on “AI and Cybersecurity” provides comprehensive insights into the factors influencing the effectiveness of AI components, defining the requirements for human operators supervising and...
Cybersecurity and resiliency of Europe’s communications infrastructures and networks
The document provides a comprehensive analysis of threats, vulnerabilities, and risk scenarios in the telecommunications sector, focusing on public electronic communications networks and core Internet infrastructure....
INFORMATION SECURITY TRAINING AWARENESS DECK
The document covers various aspects of information security, starting with the agenda which includes topics like Incident Response, Safe Practices, Data Classification, Information Security, Pillars of...
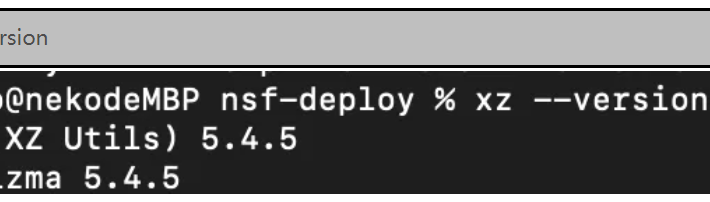
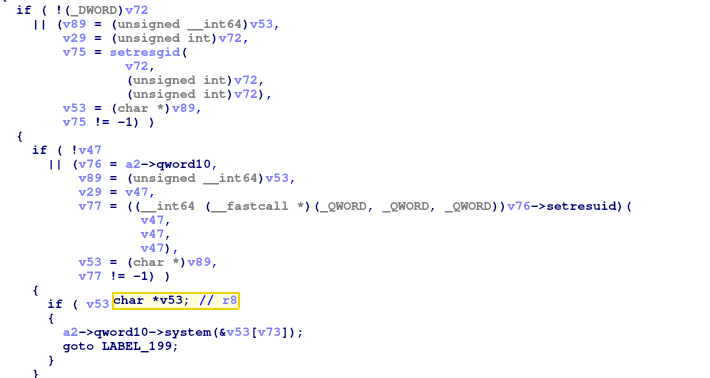
XZ Utils Backdoor Vulnerability (CVE-2024-3094) Advisory – Source: securityboulevard.com
Source: securityboulevard.com – Author: NSFOCUS Overview NSFOCUS CERT recently detected that a backdoor vulnerability in XZ Utils (CVE-2024-3094) was disclosed from the security community, with a...
Bombshell in SSH servers! What CVE-2024-3094 means for Kubernetes users – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amit Schendel On March 29, 2024, Red Hat disclosed CVE-2024-3094, scoring a critical CVSS rating of 10. Stemming from a supply chain...
Critical Backdoor Found in XZ Utils (CVE-2024-3094) Enables SSH Compromise – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tom Abai A critical vulnerability (CVE-2024-3094) was discovered in the XZ Utils library on March 29th, 2024. This severe flaw allows attackers...
Cybersecurity Tabletop Exercises: How Far Should You Go? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lohrmann on Cybersecurity With global cyber threats and other international tensions growing, what scenarios should state and local governments consider when conducting...
Poland launches inquiry into previous government’s spyware use – Source: www.theguardian.com
Source: www.theguardian.com – Author: Shaun Walker in Warsaw Poland has launched an investigation into its previous government’s use of the controversial spyware Pegasus, with a parliamentary...
Ross Anderson – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Ross Anderson Ross Anderson unexpectedly passed away Thursday night in, I believe, his home in Cambridge. I can’t remember when...
DinodasRAT malware targets Linux servers in espionage campaign – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Security researchers have observed Red Hat and Ubuntu systems being attacked by a Linux version of the DinodasRAT (also known...
It’s surprisingly difficult for AI to create just a plain white image – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ax Sharma Image credit: Siyuan via Unsplash. Not AI. Generative AI services like Midjourney and OpenAI’s DALL-E can deliver the unimaginable when it comes to...
Protecting Data in The Final Stretch of The Supply Chain – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Building a Secure Last Mile for Global Commerce By Dan O’Toole, Chairman & CEO, Arrive Navigating the Last Mile: Securing...
Passwords In the Air – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Gautam Hazari, Chief Technology Officer, Sekura.id Imagine, you are sitting in a café, sipping the skillfully crafted coffee by...
Zero-Day Bonanza Drives More Exploits Against Enterprises – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading Source: Sondem via Alamy Stock Photo The escalating cybersecurity arms race between adversaries and enterprises is...
‘Darcula’ Phishing-as-a-Service Operation Bleeds Victims Worldwide – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Leyden, Contributing Writer Source: Cristian Mircea Balate via Alamy Stock Photo Phishing-as-a-service has come of age with what’s being billed as...
Worldwide Agenda Ransomware Wave Targets VMware ESXi Servers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Igor Golovnov via Alamy Stock Photo The Agenda ransomware group has been ramping up infections worldwide, thanks...
Apple Security Bug Opens iPhone, iPad to RCE – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Apple finally has released more details on the mysterious updates the company silently pushed last week for iOS...
Patch Now: Critical Fortinet RCE Bug Under Active Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Postmodern Studio via Shutterstock As expected, cyberattackers have pounced on a critical remote code execution (RCE) vulnerability...
How New-Age Hackers Are Ditching Old Ethics – Source: www.darkreading.com
Source: www.darkreading.com – Author: Adam Darrah Adam Darrah, Senior Director of Dark Ops, ZeroFox March 26, 2024 4 Min Read Source: Anthony Spratt via Alamy Stock...
Abstract Security Brings AI to Next-Gen SIEM – Source: www.darkreading.com
Source: www.darkreading.com – Author: Fahmida Y. Rashid, Managing Editor, Features, Dark Reading Source: YAY Media AS via Alamy Stock Photo Abstract Security has emerged from stealth...