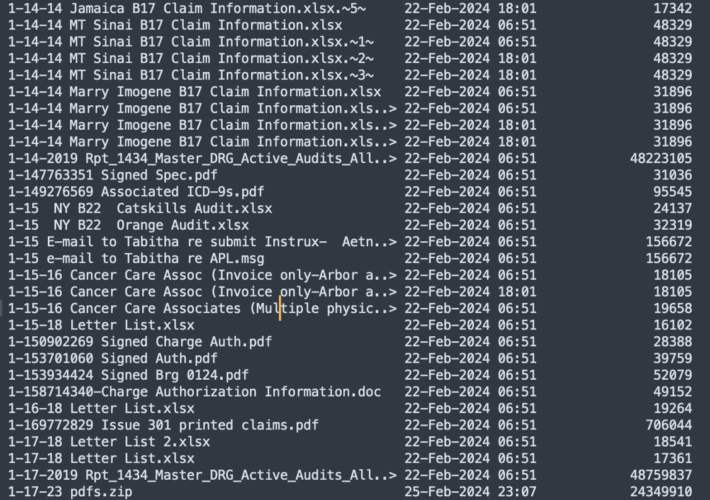
Source: securityboulevard.com – Author: Veriti Research In recent research by Veriti, a significant cyber security breach at Change Healthcare highlighted severe vulnerabilities in healthcare data security,...
Year: 2024
RSAC Fireside Chat: Qwiet AI leverages graph-database technology to reduce AppSec noise – Source: securityboulevard.com
Source: securityboulevard.com – Author: bacohido By Byron V. Acohido AppSec has never been more challenging. By the same token, AppSec technology is advancing apace to help...
BTS #30 – Systems Of Trust – Robert Martin – Source: securityboulevard.com
Source: securityboulevard.com – Author: Chris Garland Bob Martin comes on the show to discuss systems of trust, supply chain security and more! Show Notes Watch Subscribe...
Human Error and AI Emerge as Key Challenges in Survey of CISOs – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tony Bradley The 2024 Proofpoint “Voice of the CISO” report is a useful barometer for understanding the current cybersecurity landscape, providing valuable...
Prompt Injection Threats Highlight GenAI Risks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nathan Eddy Prompt injection attacks, where individuals input specific instructions to trick chatbots into revealing sensitive information, are a growing risk as...
Responsible AI Licenses (RAIL): Here’s What You Need to Know – Source: securityboulevard.com
Source: securityboulevard.com – Author: AJ Starita Responsible AI Licenses (RAIL) are a class of licenses created with the intention of preventing harmful or unethical uses of...
USENIX Security ’23 – PET: Prevent Discovered Errors from Being Triggered in the Linux Kernel – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX Security ’23 – PET: Prevent Discovered Errors from Being Triggered...
Security Compliance 101: What It Is and How to Master It – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matt Kelly Talk to any compliance officer today, and they will all agree that modern security compliance — fulfilling your organization’s regulatory...
CFO Deepfake Redux — Arup Lost $26M via Video – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings Construction giant Arup Group revealed as victim of January theft: 10% of net profit lost. A poor peon in the finance...
A journey into forgotten Null Session and MS-RPC interfaces – Source: securelist.com
Source: securelist.com – Author: Haidar Kabibo A journey into forgotten Null Session and MS-RPC interfaces (PDF) It has been almost 24 years since the null session...
Webinar | Level Up Your Security Stack: EDR vs Endpoint Privilege Management – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Chip Gandy Lead Endpoint Engineer, Cox Communications Chip Gandy is the Lead Endpoint Engineer for Cox Communications. He has been in...
Live Webinar | Adversary Analysis of Ransomware Trends – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Ray Umerley Field CISO, Coveware Ray Umerley is the Field CISO for Coveware. With more than 20+ years of experience in...
OpenText Boosts MDR Offering for MSPs With Pillr Acquisition – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Managed Detection & Response (MDR) , Managed Security Service Provider (MSSP) Purchase Fills Gap in OpenText’s...
Secure Your Applications: Learn How to Prevent AI Generated Code Risks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Webinar | Mythbusting MDR – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Rockwell Automation Urges Disconnection of ICS from the Internet – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Critical Infrastructure Security , Governance & Risk Management , Operational Technology (OT) Advisory Says Disconnecting ICS Reduces Exposure to Malicious Cyber...
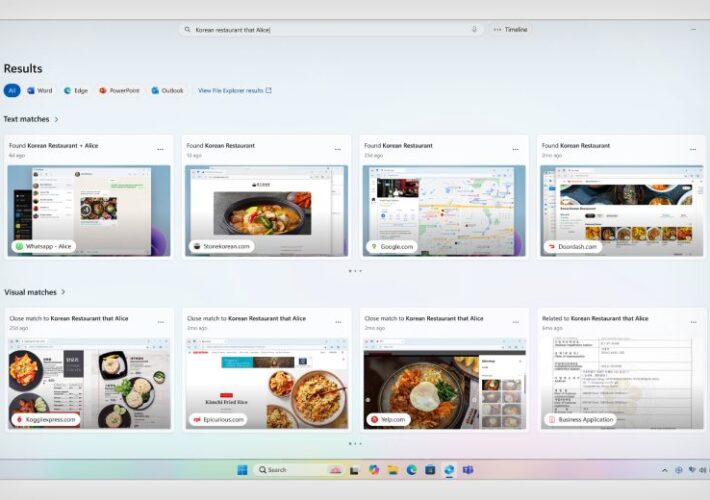
Microsoft’s Recall Stokes Security and Privacy Concerns – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Privacy UK Privacy Watchdog Launches Probe Into Microsoft Screenshot Storage Feature Akshaya Asokan (asokan_akshaya) • May...
Microsoft Build 2024: Copilot AI Will Gain ‘Personal Assistant’ and Custom Agent Capabilities – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse Following the announcements of Copilot+ enabled AI PCs at the Microsoft Build developer event on May 20, Microsoft released new...
How to Change Your VPN Location (A Step-by-Step Guide) – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Ray Fernandez We may earn from vendors via affiliate links or sponsorships. This might affect product placement on our site, but not...
Must-know insights when navigating the CISO career path – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: The CISO career path is as exciting as it is fraught with perils. Modern CISOs exist at the intersection...
News analysis Q&A: Shake up of the SIEM, UEBA markets continues as LogRhythm-Exabeam merge – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido It’s easy to compile a checklist on why the announced merger of LogRhythm and Exabeam could potentially...
News alert: AI SPERA integrates its ‘Criminal IP’ threat intelligence tool into AWS Marketplace – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: cybernewswire Torrance,Calif., May 22, 2024, CyberNewsWire — AI SPERA, a leader in Cyber Threat Intelligence (CTI) solutions, announced today that its proprietary...
US Pumps $50M Into Better Healthcare Cyber Resilience – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 2 Min Read Source: Olekcii Mach via Alamy Stock Photo The Advanced Research Projects Agency for Health (ARPA-H) pledged...
GitHub Authentication Bypass Opens Enterprise Server to Attackers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Igor Golovnov via Alamy Stock Photo A max-critical security vulnerability in GitHub’s Enterprise Server could...
Trends at the 2024 RSA Startup Competition – Source: www.darkreading.com
Source: www.darkreading.com – Author: Paul Shomo 5 Min Read Source: Aleksia via Alamy Stock Photo COMMENTARY Artificial intelligence (AI) security, automation’s nonhuman identity problem, and the...
Snowflake's Anvilogic Investment Signals Changes in SIEM Market – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Data service provider Snowflake deepened its strategic partnership with cybersecurity-analytics provider Anvilogic this week with a joint offering...
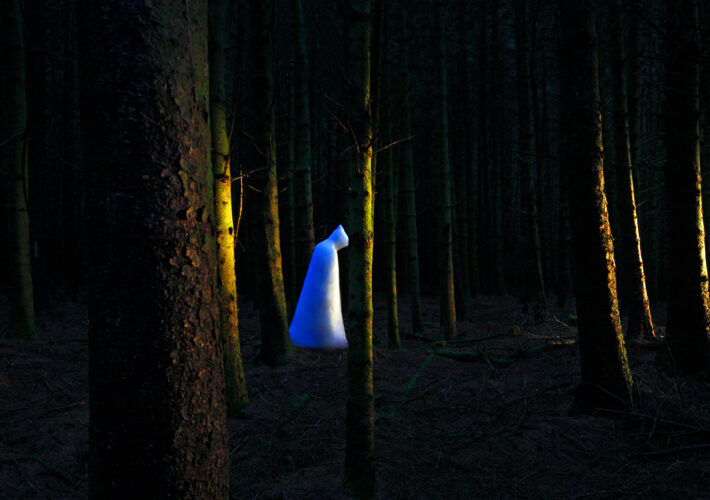
Novel EDR-Killing 'GhostEngine' Malware Is Built for Stealth – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Jack Maguire via Alamy Stock Photo A novel malware that targets vulnerable drivers to terminate and thus...
Preparing Your Organization for Upcoming Cybersecurity Deadlines – Source: www.darkreading.com
Source: www.darkreading.com – Author: Karl Mattson 5 Min Read Source: vska via Alamy Stock Vector COMMENTARY As our world becomes increasingly digitized, malicious actors have more...
Chinese 'ORB' Networks Conceal APTs, Render Static IoCs Irrelevant – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Porntep Lueangon via Alamy Stock Photo Chinese threat actors have been quietly and gradually revolutionizing anti-analysis techniques...
Critical Netflix Genie Bug Opens Big Data Orchestration to RCE – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: batjaket via Shutterstock A critical vulnerability in the open source version of Netflix’ Genie job orchestration engine...