Source: securityboulevard.com – Author: Dave Ferguson Many software development shops deliver their product releases via virtual machine (VM) disk images. Whether deployed to a cloud environment,...
Year: 2024
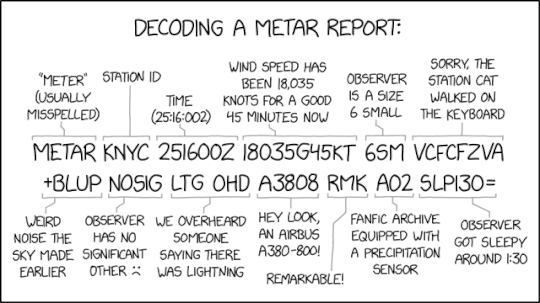
Randall Munroe’s XKCD ‘METAR’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Permalink *** This is a Security Bloggers Network syndicated blog from Infosecurity.US authored by Marc Handelman. Read the original post...
Is Your Website Leaking Sensitive Patient Information to Facebook? A disturbing story about HIPAA (and How to Avoid It) – Source: securityboulevard.com
Source: securityboulevard.com – Author: mykola myroniuk Picture this scenario: You’ve used every tool you have to secure your web pages and forms so patient information is...
Reflecting on a Year of Compromised Data – Source: securityboulevard.com
Source: securityboulevard.com – Author: Enzoic Updates from Enzoic’s Threat Research Team As the year’s end approaches, we’ve been taking a moment to review the changes and...
Balbix is recognized in Forrester’s CRQ Solutions Landscape, Q4 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Gaurav Banga Last week, Balbix was recognized in the Forrester Cyber Risk Quantification (CRQ) Solutions Landscape, Q4 2024. You can read the...
DEF CON 32 – Leveraging Private APNs For Mobile Network Traffic Analysis – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Tuesday, December 17, 2024 Home » Security Bloggers Network » DEF CON 32 – Leveraging Private APNs For Mobile Network...
This new cipher tech could break you out of your Gen AI woes – Source: www.csoonline.com
Source: www.csoonline.com – Author: As companies scramble for tougher shields against Gen AI risks, homomorphic encryption steps into the spotlight, bringing a unique superpower: it can...
Data Security Posture Management: Die besten DSPM-Tools – Source: www.csoonline.com
Source: www.csoonline.com – Author: Data-Security-Posture-Management-Tools können Sie dabei unterstützen, sensible Informationen zu identifizieren und das Risiko von Datenverlusten zu minimieren. Data Security Posture Management erfordert nicht...
Lesson from latest SEC fine for not completely disclosing data breach details: ‘Be truthful’ – Source: www.csoonline.com
Source: www.csoonline.com – Author: After a Michigan financial institution agrees to pay US$7 million in regulatory fines, an expert says CISOs and boards should realize proper...
That cheap webcam? HiatusRAT may be targeting it, FBI warns – Source: www.csoonline.com
Source: www.csoonline.com – Author: Cyberattackers are scanning for vulnerable web cameras and DVRs to install a remote access Trojan previously used against the DoD and over...
Next-gen cybercrime: The need for collaboration in 2025 – Source: www.csoonline.com
Source: www.csoonline.com – Author: FortiGuard Labs’ Cyberthreat Predictions for 2025 report identifies emerging threat trends for the coming year and offers actionable guidance on how organizations...
“Ratten”-Malware greift Kameras und DVR an – Source: www.csoonline.com
Source: www.csoonline.com – Author: News 17 Dezember 20243 Minuten FBI warnt vor HiatusRAT-Malware, die auf Webcams und Digitale Videorekorder (DVRs) abzielt. Digitale Nager machen sich laut...
US moves to tighten restrictions on China Telecom amid security fears – Source: www.networkworld.com
Source: www.networkworld.com – Author: Last week, the government issued a preliminary ruling deeming China Telecom Americas’ US network and cloud operations a national security risk. The...
CrowdStrike Survey Highlights Security Challenges in AI Adoption – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse Do the security benefits of generative AI outweigh the harms? Just 39% of security professionals say the rewards outweigh the...
Astrill VPN Review: Features, Performance, and Insights – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Drew Robb We may earn from vendors via affiliate links or sponsorships. This might affect product placement on our site, but not...
Texas Tech Fumbles Medical Data in Massive Breach – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Kirby Lee via Alamy Stock Photo NEWS BRIEF Texas Tech University’s Health Sciences Centers...
CISA Directs Federal Agencies to Secure Cloud Environments – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE WASHINGTON – The Cybersecurity and Infrastructure Security Agency (CISA) today issued Binding Operational Directive (BOD) 25-01, Implementing Secure Practices for Cloud Services to...
Delinea Joins CVE Numbering Authority Program – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SAN FRANCISCO–(BUSINESS WIRE)– Delinea, a pioneering provider of solutions for securing identities through centralized authorization, today announced it has been...
Azure Data Factory Bugs Expose Cloud Infrastructure – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Aleksia via Alamy Stock Photo Three flaws discovered in the way Microsoft’s Azure-based data integration service leverages...
CompTIA Xpert Series Expands With SecurityX Professional Certification – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE DOWNERS GROVE, Ill., Dec. 17, 2024 /PRNewswire/ — A new vendor-neutral expert-level cybersecurity certification for cybersecurity professionals continues the comprehensive efforts to...
To Defeat Cybercriminals, Understand How They Think – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ben Barrontine Ben Barrontine, Vice President of Executive Services & Partnerships, 360 Privacy December 17, 2024 4 Min Read Source: Igor Stevanovic...
Wald.ai Launches Data Loss Protection for AI Platforms – Source: www.darkreading.com
Source: www.darkreading.com – Author: Fahmida Y. Rashid Source: f:nalinframe via Alamy Stock Photo NEWS BRIEF As more organizations explore ways to use AI tools such as...
BlackBerry to Sell Cylance to Arctic Wolf – Source: www.darkreading.com
Source: www.darkreading.com – Author: Fahmida Y. Rashid Source: DigtialStorm via iStock NEWS BRIEF Arctic Wolf has announced plans to acquire Cylance from its owner, BlackBerry, to...
Sophisticated TA397 Malware Targets Turkish Defense Sector – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: A sophisticated phishing attack targeting a Turkish defense sector organization was recently uncovered by security researchers, shedding light on the evolving tactics...
Texas Tech University Data Breach Impacts 1.4 Million – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: A ransomware attack targeting the Texas Tech University Health Sciences Center (TTUHSC) has compromised the personal and medical information of 1.4 million...
Cybercriminals Exploit Google Calendar to Spread Malicious Links – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: New research from Check Point has revealed how cybercriminals are bypassing email security measures by using Google Calendar and Drawings to send...
GenAI: Security Teams Demand Expertise-Driven Solutions – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: Generative AI (GenAI) integration continues to be at the top of many cybersecurity leaders’ minds, but not at all costs, according to...
EU Sanctions Russian Cyber Actors for “Destabilizing Actions” – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: The European Union (EU) has announced sanctions against Russian cyber actors for carrying out attacks and disinformation campaigns abroad. The European Council...
New APIs Discovered by Attackers in Just 29 Seconds – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: Newly deployed and potentially unprotected APIs are being discovered in under half a minute, at extremely low cost to threat actors, according...
US Unveils New National Cyber Incident Response Plan – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: The US government has published a new draft National Cyber Incident Response Plan (NCIRP), setting out the roles and responsibilities for public...