Source: securityboulevard.com – Author: Marc Handelman Photograph Courtesy of the United States Marine Corps, Photographer: Caitlin Brink, CPL, USMC Permalink *** This is a Security Bloggers...
Month: May 2024
Microsoft’s Copilot+ Recall Feature, Slack’s AI Training Controversy – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tom Eston Episode 331 of the Shared Security Podcast discusses privacy and security concerns related to two major technological developments: the introduction...
4 Reasons Why SaaS Security Must Change | Grip – Source: securityboulevard.com
Source: securityboulevard.com – Author: Grip Security Blog Innovation has always been a catalyst for transformation, driving significant changes across industries. Amazon introduced a new way of...
USENIX Security ’23 – ARGUS: Context-Based Detection of Stealthy IoT Infiltration Attacks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters:Phillip Rieger, Marco Chilese, Reham Mohamed, Markus Miettinen, Hossein Fereidooni, Ahmad-Reza Sadeghi Many thanks to USENIX for publishing their outstanding...
Navigating the AI Revolution: The Global Battle for Tech Supremacy – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lohrmann on Cybersecurity Artificial intelligence is yielding unprecedented benefits, battles, opportunities and fears — and advancing faster than ever. What is the...
What is Azure Identity Protection and 7 Steps to a Seamless Setup – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ofir Stein Protecting credentials has become increasingly critical in recent years, with everyday employees using more passwords, devices, and systems than ever...
Court Orders Optus to Release Data Breach Report to Lawyers – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Incident & Breach Response , Legislation & Litigation Class Action Law Firms Seek Access to Commissioned...
How Microsoft Secures Generative AI – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Enabling Safety in the Age of Generative AI Microsoft •...
A Strategic Approach to Stopping SIM Swap Fraud – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Finance & Banking , Fraud Management & Cybercrime , Fraud Risk Management The UAE No Longer Has Cases of SIM Swap...
Surveillance Risk: Apple’s WiFi-Based Positioning System – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Patch Management , Privacy Starlink Routers in Ukraine and Gaza Trackable via Apple WPS, Researchers Warn...
A Fireside Chat with CyberArk’s Incident Response & Red Teams – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development , Threat Detection Presented by CyberArk 60 minutes...
Bitsight, SecurityScorecard, Panorays Lead Risk Ratings Tech – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Risk Assessments Automation, Improved Data Validation Reduce False Positives for Cyber Risk Ratings Michael Novinson (MichaelNovinson)...
EU Commission and Microsoft Appeal EDPS Office 365 Decision – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Standards, Regulations & Compliance March Decision Mandated Commission to Stem Data Flows From Its Office 365 Use Akshaya Asokan (asokan_akshaya) •...
Almost all citizens of city of Eindhoven have their personal data exposed – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley A data breach involving the Dutch city of Eindhoven left the personal information related to almost all of its citizens...
UK Government ponders major changes to ransomware response – what you need to know – Source: www.exponential-e.com
Source: www.exponential-e.com – Author: Graham Cluley What’s happened? Recorded Future has reports that the British Government is proposing sweeping change in its approach to ransomware attacks....
CISO Cite Human Error as Top IT Security Risk – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nathan Eddy Human error is responsible for most cybersecurity risks, with nearly three-quarters (74%) of chief information security officers (CISOs) identifying it...
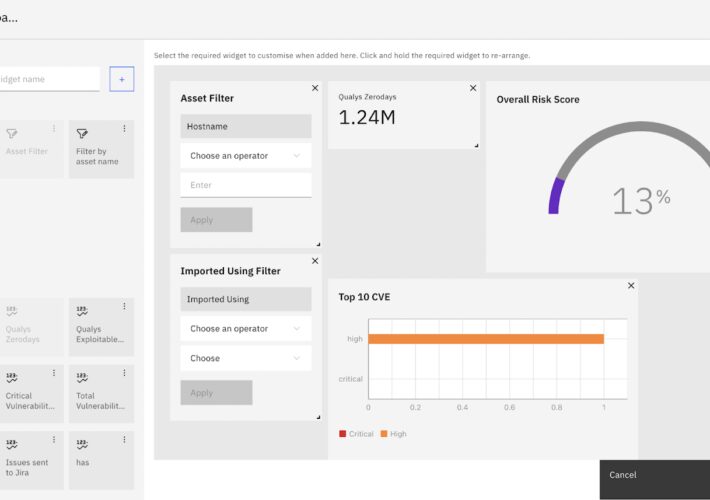
Customized Vulnerability Management Dashboard for CISOs – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alibha CISOs require a central hub for visualizing critical security data. Strobes RBVM empowers you to construct impactful CISO dashboards, transforming complex...
What are the Hallmarks of Strong Software Security? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ahona Rudra Reading Time: 4 min Why is software security so important? Simply put, there are more threats these days and many...
Ekran System Enhances Privileged Access Management: New Workforce Password Management Feature – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ani Khachatryan At Ekran System, we constantly enhance the capabilities of our platform, ensuring that organizations have effective and up-to-date tools to...
What is Cloud Penetration Testing? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Riddika Grover The digital era is constantly evolving, and businesses are rapidly migrating towards cloud-based solutions to leverage the agility, scalability, and...
Guide: What is FedRAMP Tailored and What is The Difference? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Max Aulakh In the past, we’ve talked a lot about the various FedRAMP guidelines required to reach either a single Authority to...
Optimizing CI/CD Security: Best Practices for a Robust Software Delivery Pipeline – Source: securityboulevard.com
Source: securityboulevard.com – Author: Apurva Dave Tools Workload IAM automatically manages access. Secrets management tools such as AWS Secrets Manager or Microsoft Azure Key Vault can...
Ad Protect: Mastering the Detection of Bot-Driven Ad Fraud – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lorenzo Vayno Digital ad fraud is taking billions out of marketing budgets, highlighting the need for precise detection tools that can identify...
Leading LLMs Insecure, Highly Vulnerable to Basic Jailbreaks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nathan Eddy There are significant security concerns in the deployment of leading large language models (LLMs), according to a study from U.K....
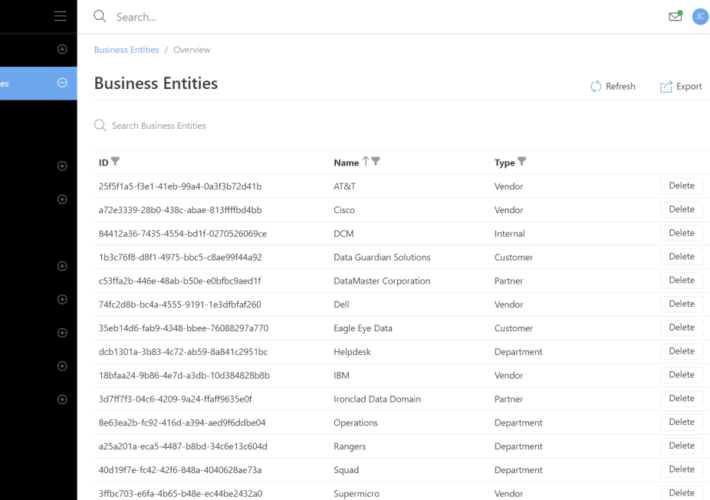
Business Entities – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rajan Sodhi We’ve introduced Business Entities, a game-changer for tracking customers, partners, and department associations with assets, connections, and circuits. Each entity...
Concentric AI to Unveil Data Security Remediation and Compliance Reporting Capabilities at Infosecurity Europe 2024 – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SAN MATEO, Calif., May 23, 2024 — Concentric AI, a leading vendor of intelligent AI-based solutions for autonomous data security posture management (DSPM), announced...
Seizing Control of the Cloud Security Cockpit – Source: www.darkreading.com
Source: www.darkreading.com – Author: Michael Bargury 3 Min Read Source: JLBvdWOLF via Alamy Stock Photo The image of a cockpit always struck me as overwhelming. So...
SOCRadar Secures $25.2M in Funding to Combat Multibillion-Dollar Cybersecurity Threats – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE NEWARK, Del., May 22, 2024 /PRNewswire/ — SOCRadar, a leading provider of enterprise-grade, end-to-end threat intelligence and brand protection, today announced the successful...
Bugcrowd Acquires Informer to Enhance Attack Surface Management, Penetration Testing – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SAN FRANCISCO, May 23, 2024 — Bugcrowd, a leading provider of crowdsourced security, today announced it has acquired Informer, a leading provider...
Courtroom Recording Platform JAVS Hijacked in Supply Chain Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading Source: David R. Frazier Photolibrary, Inc. via Alamy Stock Photo A Windows version of the RustDoor...