Source: www.proofpoint.com – Author: 1 Chief information security officers around the globe “are nervously looking over the horizon,” according to a survey of 1,600 CISOs that...
Month: May 2024
Identity vulnerabilities a concern at Microsoft, outside researcher claims – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Top insights for IT pros From cybersecurity and big data to cloud computing, IT Brew covers the latest trends shaping business...
7 best practices for tackling dangerous emails – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Email is the #1 means of communication globally. It’s simple, affordable and easily available. However, email systems weren’t designed...
6 Facts About How Interpol Fights Cybercrime – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ericka Chickowski, Contributing Writer Source: Olena Bartienieva via Alamy Stock Photo It takes a complex coordination of law enforcement, judicial processes, and...
Microsoft’s ‘Recall’ Feature Draws Criticism From Privacy Advocates – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Mojahid Mottakin via Shutterstock Microsoft’s plans to introduce a “Recall” feature powered by artificial intelligence in its...
AI Voice Generator App Used to Drop Gipy Malware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: OleCNX via Alamy Stock Photo Gipy, a newly discovered campaign using a strain of infostealer...
Google Discovers Fourth Zero-Day in Less Than a Month – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: dpa picture alliance via Alamy Stock Photo Google has released an update from its Chrome...
When ‘No’ & ‘Good Enough’ Challenge Cybersecurity – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tyler Farrar 3 Min Read Source: Skorzewiak via Alamy Stock Photo COMMENTARY In the realm of cybersecurity, the path to securing necessary...
The SEC’s SolarWinds Case: What CISOs Should Do Now – Source: www.darkreading.com
Source: www.darkreading.com – Author: Scott H. Kimpel Source: Zhanna Hapanovich via Shutterstock COMMENTARY In October 2023, the Securities and Exchange Commission (SEC) dramatically altered the landscape...
Future-Proof Your Cybersecurity AI Strategy – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security 3 Min Read Source: Kittipong Jirasukhanont via Alamy Stock Photo With the constant onslaught of new attacks and emerging threats,...
CyberArk Goes All In on Machine Identity With Venafi Deal – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jeffrey Schwartz, Contributing Writer Source: Mopic via Alamy Stock Photo Identity-based attacks aren’t just limited to breached credentials of people with rights...
Russia’s Turla APT Abuses MSBuild to Deliver TinyTurla Backdoor – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Age Foto Stock via Alamy Stock Photo A Russia-linked advanced persistent threat (APT) group has been abusing...
Hacker defaces spyware app’s site, dumps database and source code – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan A hacker has defaced the website of the pcTattletale spyware application, found on the booking systems of several Wyndham hotels...
Get 9 Courses on Ethical Hacking for Just $50 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Academy Published May 27, 2024 We may earn from vendors via affiliate links or sponsorships. This might affect product placement on...
SentinelOne vs Palo Alto: Compare EDR software – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Devin Partida Perhaps you’re looking for an endpoint detection and response tool to enhance your cybersecurity efforts. SentinelOne and Palo Alto are...
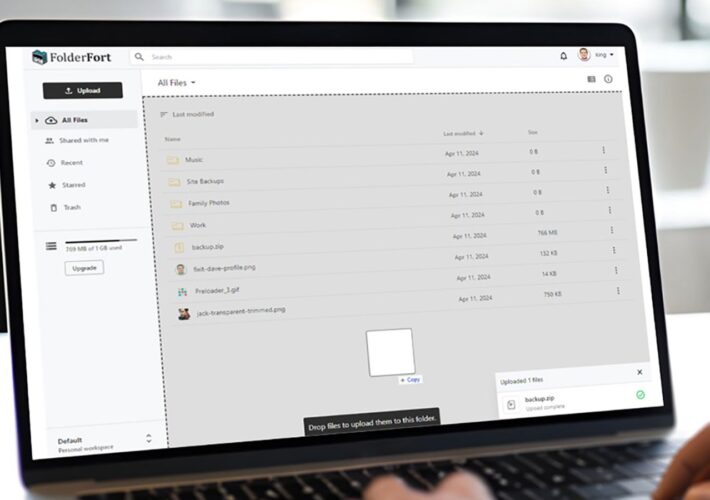
Get a Lifetime of 1TB Cloud Storage for Only $80 With FolderFort – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Academy Published May 24, 2024 We may earn from vendors via affiliate links or sponsorships. This might affect product placement on...
AI Seoul Summit: 4 Key Takeaways on AI Safety Standards and Regulations – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Fiona Jackson The AI Seoul Summit, co-hosted by the Republic of Korea and the U.K., saw international bodies come together to discuss...
CISOs in Australia Urged to Take a Closer Look at Data Breach Risks – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Ben Abbott Clayton Utz cyber partner Brenton Steenkamp has seen his fair share of cyber attacks. Returning to Australia in October after...
Friday Squid Blogging: Dana Squid Attacking Camera – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments vas pup • May 24, 2024 7:14 PM Ex-Google CEO says the US and China’s most powerful AI...
On the Zero-Day Market – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier On the Zero-Day Market New paper: “Zero Progress on Zero Days: How the Last Ten Years Created the Modern Spyware...
Beyond Code: Harnessing AI for Advanced Cybersecurity Solutions – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Angel Vossough, Co-Founder & CEO of BetterAI.io Cybersecurity defenses are shifting, aiming to predict and block cyber threats in...
Best Password Generators of 2024 to Secure Your Accounts – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Overview of best password generators to secure online accounts By Mia Naumoska, CMO at Internxt Despite the current advances in...
Becoming Resilient to The Cyber Incidents of Today And Tomorrow – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Theresa Le, Chief Claims Officer, Cowbell As cyber threats escalate and evolve worldwide, businesses must ensure their foundations are...
Anatomy Of an Endpoint Attack: How A Cyberattack Can Compromise an Enterprise Network – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Guillermo Gomez, Vice President of Endpoint Product, WatchGuard Technologies For truly effective network security posture, it’s crucial to protect...
The Critical Role of Training and Phishing Testing in Safeguarding Financial Data – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Empowering the Human Firewall: The Bedrock of Cyber Defense By Michael Cocanower, CEO, AdviserCyber The Evolving Cybersecurity Landscape for RIAs...
A Transformative Landscape in Legal Technology: From the Past to AI-Powered Future – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Rob Scott, Chief Innovator – Monjur The modern digital era, ripe with unparalleled technological evolutions, is remolding our perceptions...
An XSS flaw in GitLab allows attackers to take over accounts – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini An XSS flaw in GitLab allows attackers to take over accounts GitLab addressed a high-severity cross-site scripting (XSS) vulnerability that allows...
Rising Like A Phoenix, ShowMeCon 2024 Resurrects A Security Community In The Midwest – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dwayne McDaniel St. Charles, MO, is known as the launching point for a famous exploratory mission from U.S. history: the Lewis and...
AI Governance – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deborah Erlanger What is the Centraleyes AI Governance Framework? The AI Governance assessment, created by the Analyst Team at Centraleyes, is designed...
The Importance of Patching Vulnerabilities in Cybersecurity – Source: securityboulevard.com
Source: securityboulevard.com – Author: Joao Correia One of the most critical yet often overlooked aspects of cybersecurity is the timely patching of vulnerabilities. While much attention...