Source: securityboulevard.com – Author: Jeffrey Burt Dell is sending emails to as many as 49 million people about a data breach that exposed their names, physical...
Month: May 2024
Cybersecurity Salary: How Much Can You Earn? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kevin Smith Maybe you’ve heard there’s an interplanetary-sized gap in the amount of cybersecurity professionals available and the roles needed to be...
Daniel Stori’s ‘tar.gz’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the inimitable Daniel Stori at Turnoff.US! Permalink *** This is a Security Bloggers Network syndicated blog from Infosecurity.US authored...
10 ways generative AI drives stronger security outcomes – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Eighty-seven percent of cyber security professionals recognize the potential inherent in leveraging AI for security purposes. The growing volume...
ISMG Editors: RSA Conference 2024 Wrap-Up – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Events , RSA Conference , RSA Conference Videos Panels Unpack the Buzz Around AI, Future Trends for CISOs Anna Delaney (annamadeline)...
Hackers Steal Credit Card Data of Deal-Seeking Shoppers – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Card Not Present Fraud , Fraud Management & Cybercrime China-Linked Criminals Processed Orders Worth $50M: Security Research Labs Rashmi Ramesh (rashmiramesh_)...
Live Webinar | Correcting your Cyber Security Posture with the Board: Data, Metrics and Lessons from 2023 – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Tim Grieveson Senior Vice President – Global Cyber Security Risk Advisor, Bitsight Tim Grieveson is Senior Vice President – Global Cyber...
Solving the Fractured Data Problem in Exposure Management – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Events , Governance & Risk Management , RSA Conference Sevco Security’s J.J. Guy on Aggregating and Prioritizing Vulnerabilities Mathew J. Schwartz...
Ascension Diverts Emergency Patients, Postpones Care – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Healthcare Wednesday Cyber Incident Shakes America’s Largest Healthcare System Marianne Kolbasuk McGee (HealthInfoSec) •...
MoD contractor hacked by China failed to report breach for months – Source: www.theguardian.com
Source: www.theguardian.com – Author: Anna Isaac and Dan Sabbagh The IT company targeted in a Chinese hack that accessed the data of hundreds of thousands of...
Red Sea Crisis and the Risk of Cyber Fallout – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Stevin By Stan Vitek, Resident Geopolitical Analyst, Cyfirma Introduction As Israel’s military campaign in Gaza continues, the United States as a political...
How Can Businesses Defend Themselves Against Common Cyberthreats? – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Fiona Jackson TechRepublic consolidated expert advice on how businesses can defend themselves against the most common cyberthreats, including zero-days, ransomware and deepfakes....
CISO as a CTO: When and Why It Makes Sense – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ericka Chickowski, Contributing Writer Source: designer491 via Alamy Stock Photo As the CISO role matures in enterprise settings and security executives level...
Is CISA’s Secure by Design Pledge Toothless? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer At 2024’s RSA Conference this week, brand names like Microsoft, Amazon Web Service (AWS), International Business Machines (IBM),...
Reality Defender Wins RSAC Innovation Sandbox Competition – Source: www.darkreading.com
Source: www.darkreading.com – Author: Karen Spiegelman, Features Editor Reality Defender co-founder and CEO Ben Colman (left) onstage with host Hugh ThompsonSource: RSA Conference For the second...
Ascension Healthcare Suffers Major Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer Source: MBI via Alamy Stock Photo Healthcare provider Ascension, which operates 140 hospitals across 19 states, fell victim...
Dark Reading Confidential: The CISO and the SEC – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Transcript of Dark Reading Confidential, Episode 1: The CISO and the SEC Becky Bracken, Senior Editor, Dark Reading: Hello...
You’ve Been Breached: What Now? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jackson Shaw Jackson Shaw, Chief Security Officer, Clear Skye May 10, 2024 4 Min Read Source: Brain light via Alamy Stock Photo...
Dark Reading ‘Drops’ Its First Podcast – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kelly Jackson Higgins, Editor-in-Chief, Dark Reading Source: aleksandr Lychagin via Alamy Stock Photo At one of the first meetings Dark Reading held...
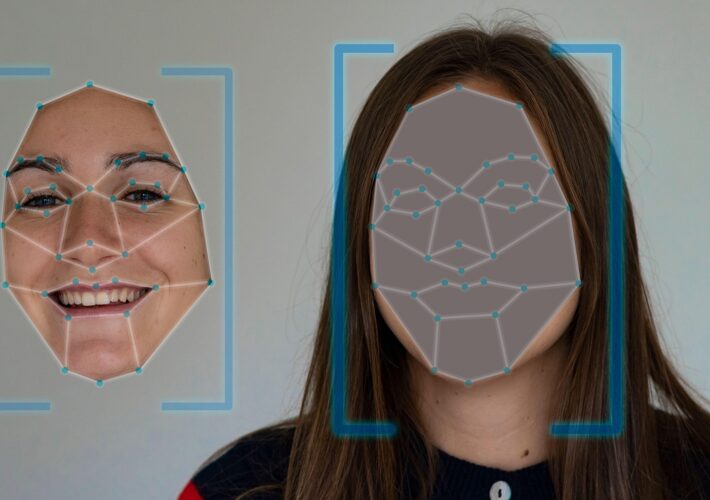
Cybersecurity in a Race to Unmask a New Wave of AI-Borne Deepfakes – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kelly Jackson Higgins, Editor-in-Chief, Dark Reading Source: Alfonso Fabiio Iozzino via Alamy Stock Photo RSA CONFERENCE 2024 – San Francisco – Everyone’s...
Token Security Launches Machine-Centric IAM Platform – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Poptika via Shutterstock The shift to cloud technologies and microservices means organizations are now managing...
Boeing refused to pay $200 million LockBit ransomware demand – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley Boeing has confirmed that it received a demand for a massive $200 million after a ransomware attack by the notorious...
$10 million reward offer for apprehension of unmasked LockBit ransomware leader – Source: www.exponential-e.com
Source: www.exponential-e.com – Author: Graham Cluley Do you know Dmitry Yuryevich Khoroshev? If you do, there’s a chance that you might well on the way to...
FBI warns US retailers that hackers are targeting their gift card systems – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley The FBI has issued a warning to US retailers about a financially-motivated malicious hacking ring that has been targeting employees...
BSidesSF 2024: A Community Event Anchored To Hope For The Future Of Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dwayne McDaniel You can’t see The Golden Gate Bridge from downtown San Francisco, but if you stand at the right intersections, you...
A Practical Approach to FAIR Cyber Risk Quantification – Source: securityboulevard.com
Source: securityboulevard.com – Author: Maahnoor Siddiqui In the ever-evolving world of cybersecurity, managing risk is no longer about simply setting up firewalls and antivirus software. As...
NASA Must Improve Spacecraft Cybersecurity, GAO Report Finds – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nathan Eddy Houston, we may have a problem. NASA’s cybersecurity framework for spacecraft development is inconsistent and must be improved, according to...
Getting Started with Software Dependency Management – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rhys Arkins Dependency management is a broad topic encompassing, among other things, keeping an inventory of dependencies, removing unused dependencies, and fixing...
Make WAAP Interesting Again by Quantifying Operational Efficiency and Secure by Design. – Source: securityboulevard.com
Source: securityboulevard.com – Author: SecureIQLab The adoption of the cloud is the biggest driver of the DevOps development process. Before cloud, waterfall (80’s to late 90’s)...
Recent Breaches in Israel and Iran: A Closer Look at Cybersecurity Vulnerabilities – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alberto Casares In recent times, Israel and Iran have been caught up in a series of conflicts and tensions, both on the...