Source: krebsonsecurity.com – Author: BrianKrebs Image: Shutterstock. Apple and the satellite-based broadband service Starlink each recently took steps to address new research into the potential security...
Day: May 21, 2024
5 ways to effectively communicate cyber security value to the board – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Historically, communicating the value of cyber security to the board has always been a challenge. Cyber security staff and...
News alert: Memcyco report reveals only 6% of brands can stop digital impersonation fraud – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: cybernewswire New York, NY, May 21, 2024, CyberNewsWire — Memcyco Inc., provider of digital trust technology designed to protect companies and their...
RSAC Fireside Chat: IRONSCALES utilizes LLM, superior intel to stay a step ahead of Deepfakes – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido There was a lot of buzz at RSAC 2024 about how GenAI and Large Language Models (LLM)...
RSAC Fireside Chat: SquareX introduces security-infused browser extension to stop threats in real time – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido The open-source Chromium project seeded by Google more than a decade ago has triggered something of a web browser renaissance. Related:...
Detecting Malicious Trackers – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier From Slashdot: Apple and Google have launched a new industry standard called “Detecting Unwanted Location Trackers” to combat the misuse...
Russia’s DoppelGänger Campaign Manipulates Social Media – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security researchers have observed a new DoppelGänger campaign dubbed Operation Matriochka aimed at challenging the credibility of journalists and fact-checkers since...
70% of CISOs Expect Cyber-Attacks in Next Year, Report Finds – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Seventy percent of chief information security officers (CISOs) have said their businesses are at risk of a cyber-attack in the next...
News alert: Memcyco report reveals only 6% of brands can stop digital impersonation fraud – Source: securityboulevard.com
Source: securityboulevard.com – Author: cybernewswire New York, NY, May 21, 2024, CyberNewsWire — Memcyco Inc., provider of digital trust technology designed to protect companies and their...
Digital Impersonation Fraud: a Growing Challenge for Brands – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nathan Eddy Website impersonation scams are on the rise, and many companies are struggling to counter them effectively, according to a Memcyco...
The Role of Real-Time Incident Response in Mitigating Conversation Hijacking Attacks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Leigh Dow Communications hijacking, also known as “conversation hijacking,” has emerged as a significant threat to organizations worldwide. This form of cyberattack...
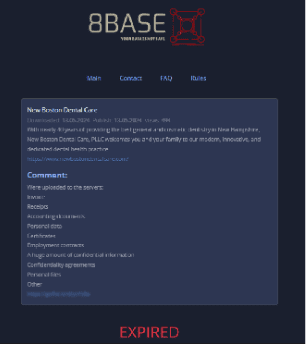
Recent Healthcare Ransomware Attacks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alberto Casares Healthcare ransomware attacks are one example of cyberattacks for the healthcare sector due to the sensitivity of its data. In...
Many Stumble Into Cybersecurity, But Leadership is By Design – Source: securityboulevard.com
Source: securityboulevard.com – Author: Elliot Volkman Today, while cybersecurity is a highly sought-after field, most of its current leaders and executives stumbled upon it. Their paths...
TuxCare and DOSIsoft Partner to Offer Ongoing Support and Cyber Protections for Radiation Oncology and Nuclear Medicine Software – Source: securityboulevard.com
Source: securityboulevard.com – Author: TuxCare Team Hospitals worldwide to be offered extended lifecycle support and security alongside five DOSIsoft solutions PALO ALTO, Calif. – May 21,...
What Is Risk Management in Cybersecurity | Kovrr – Source: securityboulevard.com
Source: securityboulevard.com – Author: Cyber Risk Quantification TL;DR Business leaders know that managing risk effectively is an essential part of running a successful business....
Latest Ubuntu Security Updates: Fixing Linux Kernel Vulnerabilities – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rohan Timalsina Several vulnerabilities have been discovered in the Linux kernel that could lead to privilege escalation, denial of service, or information...
Ask the Analyst: Nisos Events and Ticket Fraud Expert Kirk Maguire – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nisos Over fifteen million visitors, including 2 million international attendees, are expected to travel to the 2024 Paris Olympics. The opening ceremony...
How to Drive Down Skyrocketing Data Costs with the Only Cost-Optimized SIEM – Source: securityboulevard.com
Source: securityboulevard.com – Author: Blog Archives – Gurucul Harnessing and interpreting data insights for actionable solutions lies at the heart of a robust cybersecurity strategy. For...
DoJ Shakes Up North Korea's Widespread IT Freelance Scam Operation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Yogesh More via Alamy Stock Photo The North Korean government has dispatched thousands of tech-savvy workers to...
Google Pitches Workspace as Microsoft Email Alternative, Citing CSRB Report – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: monticello via Shutterstock Google is using a recent report from the US Cyber Safety Review Board (CSRB)...
CyberArk Picks Up Machine Identity Manager Venafi For $1.54B – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Lucap via Alamy Stock Photo Identity management provider CyberArk announced it will acquire Venafi from...
HP Catches Cybercriminals 'Cat-Phishing' Users – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE PALO ALTO, Calif., May 16, 2024 – HP Inc. (NYSE: HPQ) today issued its quarterly HP Wolf Security Threat Insights Report,...
Data Breach Response Provider, CyEx, Acquires Settlement Administrator, Simpluris Inc. – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE BOSTON, May 20, 2024 /PRNewswire/ — CyEx, a leading provider of cyber and data breach response solutions, has announced the acquisition of Simpluris Inc.,...
Deepfakes Rank As the Second Most Common Cybersecurity Incident for US Businesses – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE New York, NY – May 20, 2024 – Deepfakes are now the second most common cybersecurity incident encountered by businesses in...
ZeroRisk Cybersecurity Expands Global Presence With US Launch – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE ATLANTA, Ga., May 20, 2024 /PRNewswire-PRWeb/ — ZeroRisk Cybersecurity, a leading provider of innovative risk and compliance management solutions to the payment...
NRECA Receives $4M in DOE Funding to Boost Electric Co-op Cybersecurity Preparedness – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE ARLINGTON, Va. – The National Rural Electric Cooperative Association has been awarded $4 million from the Department of Energy to launch...
Sustaining Institutional Knowledge as ICT Landscapes Evolve – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Leadership & Executive Communication , Training & Security Leadership How CISOs and CIOs Can Help to Keep the Collective Wisdom of...
FCC Targets BGP Vulnerabilities with New Security Mandates – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Government FCC to Vote on Proposed Security Regulations for Leading Broadband Providers Chris Riotta...
HHS Funds $50M to Spot, Patch Hospital Vulnerabilities – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Healthcare , Industry Specific Research Agency Soliciting ‘UPGRADE’ Project Ideas to Help Boost Healthcare Cyber Marianne...
HHS Warns Health Sector of Business Email Compromise Scams – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Business Email Compromise (BEC) , Fraud Management & Cybercrime , Healthcare Agency Spells Out Measures to Avoid Falling Victim to Costly...