Source: www.cyberdefensemagazine.com – Author: Stevin By Shirley Salzman, CEO and Co-Founder, SeeMetrics As all eyes are towards the updated NIST CSF 2.0 publication, some of the...
Day: May 20, 2024
How platformization is transforming cyber security – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau With more than 15 years of experience in cyber security, Manuel Rodriguez is currently the Security Engineering Manager for the North...
What American Enterprises Can Learn From Europe's GDPR Mistakes – Source: www.darkreading.com
Source: www.darkreading.com – Author: Apu Pavithran 4 Min Read Source: Egor Kotenko via Alamy Stock Photo After almost a decade of “will they or won’t they,”...
Android Banking Trojan Antidot Disguised as Google Play Update – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer Source: the lightwriter via Alamy Stock Photo A banking Trojan impacting Google Android devices, dubbed “Antidot” by the...
IBM Sells Cybersecurity Group – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier IBM is selling its QRadar product suite to Palo Alto Networks, for an undisclosed—but probably surprisingly small—sum. I have a...
Strata’s Maverics Platform Provides Zero Downtime for Cloud-based Identity – Source: securityboulevard.com
Source: securityboulevard.com – Author: Heidi King Multi-cloud Identity Orchestration platform ensures continuous access to applications even when a primary identity provider (IDP) is unavailable BOULDER, Colo.,...
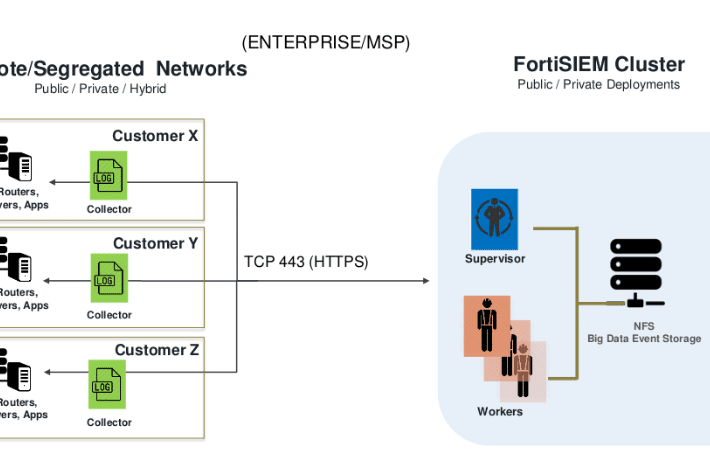
CVE-2023-34992: Fortinet FortiSIEM Command Injection Deep-Dive – Source: securityboulevard.com
Source: securityboulevard.com – Author: Zach Hanley In early 2023, given some early success in auditing Fortinet appliances, I continued the effort and landed upon the Fortinet...
How to Manage IAM Compliance and Audits – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rebecca Kappel Did you know that 80% of breaches exploit legitimate identities and are difficult to detect? It’s hard to tell a...
AlmaLinux 9.4 Released: Security and Legacy Hardware Support – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rohan Timalsina AlmaLinux 9.4, codenamed “Seafoam Ocelot,” arrived on May 6, 2024. This exciting new release from the AlmaLinux OS Foundation closely...
RSAC Fireside Chat: SquareX introduces security-infused browser extension to stop threats in real time – Source: securityboulevard.com
Source: securityboulevard.com – Author: bacohido By Byron V. Acohido The open-source Chromium project seeded by Google more than a decade ago has triggered something of a...
Scytale to Support ISO 42001, Ensuring Companies Sail Smoothly into AI Compliance – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mor Avni, Product Manager, Scytale In an era marked by rapid advancements in artificial intelligence (AI), regulatory landscapes are evolving at a...
New Tracker Warning Features on iPhones & Androids, 2024 Verizon Data Breach Investigations Report – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tom Eston In episode 330 Tom, Scott, and Kevin discuss the new features for iPhones and Android phones designed to warn users...
USENIX Security ’23 – Guarding Serverless Applications with Kalium – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX Security ’23 – Guarding Serverless Applications with Kalium by Marc...
Antivirus Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Antivirus software is critical to ensure information security of organizational networks and resources. By establishing an antivirus policy, organizations can quickly identify...