The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Month: April 2024
A DETAILED GUIDE ON DIRBUSTER
The document provides an in-depth overview of DirBuster, a penetration testing tool. It covers various modes of usage such as default mode, GET request method, pure...
South Australian Cyber Security Framework
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CLOUD SECURITY ENGINEER ROADMAP
The Cloud Security Engineer Roadmap provides a comprehensive guide for individuals looking to pursue a career in cloud security. It emphasizes key areas such as Linux...
Audit and Risk Assurance Committee Effectiveness Tool
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Is open source under siege? – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: The recent discovery of a backdoor in XZ Utils, a core compression utility embedded in countless Linux systems, has...
MY TAKE: GenAI revolution — the transformative power of ordinary people conversing with AI – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido San Francisco, Calif. — The amazing digital services we have today wouldn’t have come to fruition without...
Five Key Takeaways from the 2024 Imperva Bad Bot Report – Source: securityboulevard.com
Source: securityboulevard.com – Author: Erez Hasson Bad bots continue to affect consumers and organizations across all sectors. For over eleven years, Imperva has been dedicated to...
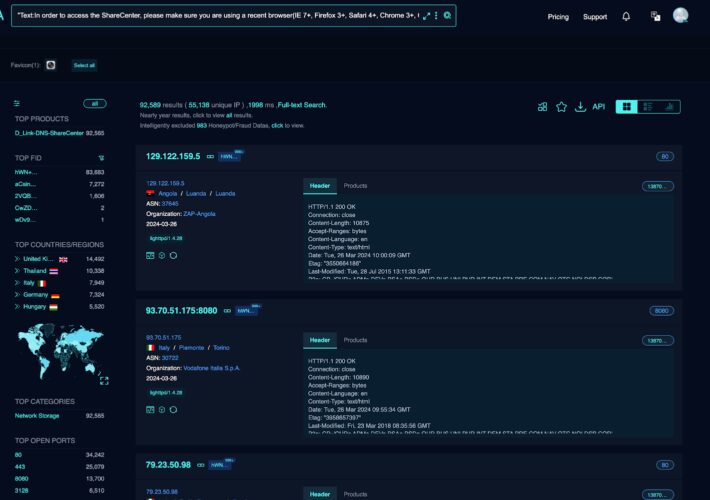
Critical RCE Vulnerability in 92,000 D-Link NAS Devices – Source: securityboulevard.com
Source: securityboulevard.com – Author: Riddika Grover Cyber attacks have become increasingly prevalent. This has caused significant adverse impacts on businesses of all sizes. According to the...
D3 Security at RSAC 2024: Streamline Your Security Operations with Smart SOAR – Source: securityboulevard.com
Source: securityboulevard.com – Author: Shriram Sharma RSA Conference 2024, taking place at San Francisco’s Moscone Center from May 6-9, is set to gather the world’s foremost...
MY TAKE: GenAI revolution — the transformative power of ordinary people conversing with AI – Source: securityboulevard.com
Source: securityboulevard.com – Author: bacohido By Byron V. Acohido San Francisco, Calif. — The amazing digital services we have today wouldn’t have come to fruition without...
Roku: Credential Stuffing Attacks Affect 591,000 Accounts – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Almost 600,000 Roku customers had their accounts hacked through two credential stuffing attacks several weeks apart, illustrating the ongoing risks...
MSP Guide: How to Safeguard Your Clients During a Ransomware Attack – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kevin Smith As a managed service provider (MSP), you are tasked with keeping clients from malicious software infections and ransomware attacks. Even...
USENIX Security ’23 – An Empirical Study & Evaluation of Modern CAPTCHAs – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters: *Andrew Searles, Yoshimichi Nakatsuka, Ercan Ozturk, Andrew Paverd, Gene Tsudik, Ai Enkoji* Many thanks to USENIX for publishing their...
Randall Munroe’s XKCD ‘Sitting in a Tree’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Zscaler to Acquire Airgap Networks to Segment Endpoint Traffic – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard Zscaler plans to acquire Airgap Networks to apply network segmentation in a way that improves security without requiring organizations to...
Likely State Hackers Exploiting Palo Alto Firewall Zero-Day – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Endpoint Security Company Released a Hotfix to the Command Injection Vulnerability Mihir Bagwe (MihirBagwe) • April 15, 2024 Likely...
FTC Bans Online Mental Health Firm From Sharing Certain Data – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Governance & Risk Management , Healthcare Proposed Action Also Orders Cerebral Inc. to Pay $7M Penalty...
Law Firm to Pay $8M to Settle Health Data Hack Lawsuit – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Healthcare , Industry Specific , Legislation & Litigation Orrick Herrington Cyberattack Compromised Clients’ Data, Affected Nearly 638,000 Marianne Kolbasuk McGee (HealthInfoSec)...
Sisense Breach Highlights Rise in Major Supply Chain Attacks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Governance & Risk Management Experts Warn of Growing Threat From Supply Chain Attacks After High-Profile Breach...
Defense Award Launches Purdue Project to Strengthen Cyber-Physical Systems – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE WEST LAFAYETTE, Ind. — Hiccups and failures of consumer cyber-physical systems like smart gadgets and appliances are inconvenient and annoying....
Cisco Duo’s Multifactor Authentication Service Breached – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading Source: olga Yastremska via Alamy Stock Photo A third-party provider that handles telephony for Cisco’s Duo...
Roku Mandates 2FA for Customers After Credential-Stuffing Compromise – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Marvin Tolentino via Alamy Stock Photo Roku is now making two-factor authentication (2FA) mandatory for...
Palo Alto Network Issues Hotfixes for Zero-Day Bug in Its Firewall OS – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Tada Images via Shutterstock Palo Alto Networks (PAN) on April 14 released hotfixes to address a maximum...
Iran-Backed Hackers Blast Out Threatening Texts to Israelis – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: BUSINESS, MONEY and IT via Alamy Stock Photo Israeli citizens received threatening text messages purportedly...
Web3 Game Developers Targeted in Crypto Theft Scheme – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Stockphoto Graph via Shutterstock A Russian threat actor is peppering game developers with fraudulent Web3 gaming projects...
Microsoft Wants You to Watch What It Says, Not What It Does – Source: www.darkreading.com
Source: www.darkreading.com – Author: Steve Weber Steve Weber, Professor of the Graduate School, UC Berkeley School of Information April 15, 2024 4 Min Read Source: Enigma...
Adapting to the Deluge of Cybersecurity Data – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Charlie Thomas, CEO, Deepwatch The ever-increasing volume of security data is becoming unmanageable through conventional data analysis, security tools...
When Security Collides with Customer Impatience – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Stevin How Biographic and Biometric Information Work as a Team to Solve the Problem By Raj Ananthanpillai, CEO, Trua Online customers don’t...
Attacking Docker
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...