Source: www.schneier.com – Author: Bruce Schneier The lawsuit has been settled: Google has agreed to delete “billions of data records” the company collected while users browsed...
Month: April 2024
SOC Audit Report Type1 Type2
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Secure Cloud Business Applications
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Basics for ProtectingCritical Infrastructure fromCyber Threats
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
TIPS TOAVOID ROMANCE SCAMS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Securityto go: A Risk Management Toolkit for Humanitarianaid Agencies
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SEXi Ransomware Desires VMware Hypervisors in Ongoing Campaign – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Don McBailey/Stockimo via Alamy Stock Photo What appears to be a fresh variant of...
Ivanti Pledges Security Overhaul the Day After 4 More Vulns Disclosed – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: garagestock via Shutterstock Ivanti CEO Jeff Abbott this week said his company will completely revamp its security...
Malicious Latrodectus Downloader Picks Up Where QBot Left Off – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading Source: Yuri Arcurs via Alamy Stock Photo At first, analysts thought the downloader was a variant...
Thousands of Australian Businesses Targeted With ‘Reliable’ Agent Tesla RAT – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Leyden, Contributing Writer Source: David Chapman via Alamy More than 11,000 Australian companies were targeted in a recent wave of cyberattacks...
Action1 Unveils ‘School Defense’ Program To Help Small Educational Institutions Thwart Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Houston, Texas, April 04, 2024 (GLOBE NEWSWIRE) — Action1 Corporation, a provider of the integrated real-time vulnerability discovery and patch...
‘Unfaking’ News: How to Counter Disinformation Campaigns in Global Elections – Source: www.darkreading.com
Source: www.darkreading.com – Author: Shamla Naidoo Shamla Naidoo, Head of Cloud Strategy & Innovation, Netskope April 3, 2024 5 Min Read Source: Feng Yu via Alamy...
Senior Tory ‘mortified’ after reportedly passing MPs’ data to dating app contact – Source: www.theguardian.com
Source: www.theguardian.com – Author: Nadeem Badshah A senior Conservative MP has reportedly admitted to giving out the personal phone numbers of colleagues to a person he...
Police launch inquiry after MPs targeted in apparent ‘spear-phishing’ attack – Source: www.theguardian.com
Source: www.theguardian.com – Author: Ben Quinn and Eleni Courea A police investigation has been launched after MPs were apparently targeted in a “spear-phishing” attack, in what...
A 5-Minute Refresher to Cryptography – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Gary (featuring Alice and Bob) by Rajvi Shroff It’s an age-old question. Alice wants to send a message to Bob. But how...
Smart Traffic Signals Security in the Era of AI and Smart Cars – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Gary Analyzing the Trade-off Between Efficiency and Security in Smart Traffic Signal Technology Integration. by Samridhi Agarwal, Masters Student, CMU Once a...
Impact of IoT Security for 5G Technology – Source: securityboulevard.com
Source: securityboulevard.com – Author: Riddika Grover 5G technology impacts not just our daily lifestyle but the Internet of Things (IoT) as well. The world of 5G...
HTTP/2 CONTINUATION Flood Vulnerability – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nadav Avital HTTP/2, a widely adopted web communication protocol, organizes data transmission through a binary framing layer, wherein all communication is divided...
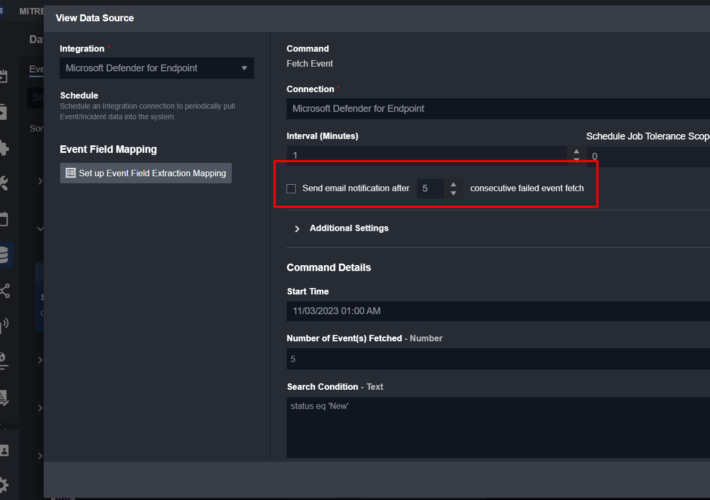
Smart SOAR’s Innovative Approach to Error-Handling Explained – Source: securityboulevard.com
Source: securityboulevard.com – Author: Shriram Sharma Our commitment to innovation is deeply rooted in the feedback we receive from those who use our Smart SOAR platform...
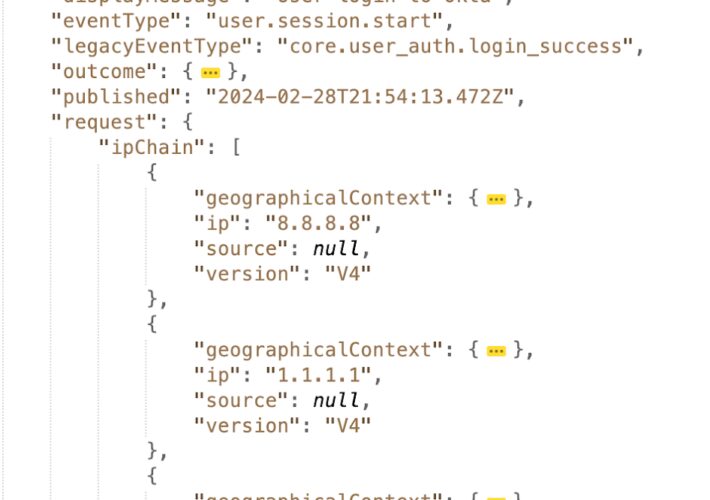
How to Correctly Use Client IP Addresses in Okta Audit Logs to Improve Identity Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Farah Iyer Being able to identify client IP addresses is essential for detecting and preventing identity-related threats. These IP addresses help establish...
Testing in Detection Engineering (Part 8) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Anton Chuvakin This blog series was written jointly with Amine Besson, Principal Cyber Engineer, Behemoth CyberDefence and one more anonymous collaborator. This...
Google Chrome Enlists Emerging DBSC Standard to Fight Cookie Theft – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Google is prototyping a new technology in Chrome that is designed to thwart the growing trend among cybercriminals of stealing...
Mastering MITRE: Enhancing Cybersecurity with Device Log Mapping – Source: securityboulevard.com
Source: securityboulevard.com – Author: Team Nuspire In the dynamic realm of cybersecurity, the MITRE ATT&CK framework has become a pivotal tool for organizations striving to fortify...
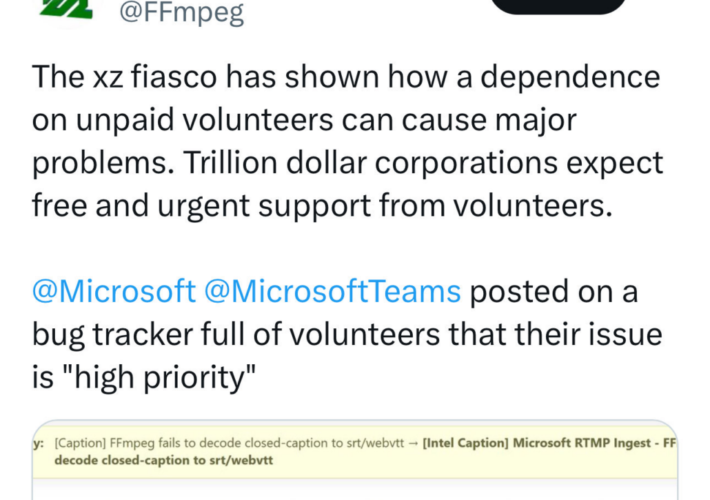
XZ and the Threats to the Digital Supply Chain – Source: securityboulevard.com
Source: securityboulevard.com – Author: Chris Garland The discovery of the backdoor in xz utils compression software last week has shone a spotlight on the threats to...
Safeguarding Data Security and Privacy on IBM Mainframe: A Comprehensive Approach – Source: securityboulevard.com
Source: securityboulevard.com – Author: Thomas Gloerfeld In today’s digitally driven world, data security and privacy are paramount concerns for organizations across all industries. With the increasing...
Google Fixes Two Pixel Zero-Days Exploited by Forensic Firms – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Bugs Allowed Device Unlocking and Memory Access Mihir Bagwe (MihirBagwe) • April 4, 2024 Google addressed two zero-day vulnerabilities...
Phishing Attacks Targeting Political Parties, Germany Warns – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Social Engineering Escalation of Cyberespionage Likely Tied to Upcoming European Elections Akshaya Asokan (asokan_akshaya) • April...
Code to Cloud Roadshow – Minneapolis In-Person Event hosted by Palo Alto Networks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cloud Data Security & Resilience , Cloud Security , Cloud-Native Application Protection Platform (CNAPP) In-Person Event Join...
Breach Roundup: Omni Hotels Acknowledges Cyber Incident – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Incident & Breach Response Also: Insurer Predicts Ransomware for Cars, Offers to Cover Towing...
AI Deepfakes Rising as Risk for APAC Organisations – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Ben Abbott AI deepfakes were not on the risk radar of organisations just a short time ago, but in 2024, they are...