Source: www.bleepingcomputer.com – Author: Mayank Parmar Windows 11 24H2 is set to arrive on existing devices this fall with several new features, mostly Copilot-related improvements. Additionally,...
Month: April 2024
Home Depot confirms third-party data breach exposed employee info – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Home Depot has confirmed that it suffered a data breach after one of its SaaS vendors mistakenly exposed a small...
New Windows driver blocks software from changing default web browser – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Microsoft is now using a Windows driver to prevent users from changing the configured Windows 10 and Windows 11 default...
The Case Study: The Exploitation of Mechatronics Systems – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Milica D. Djekic The mechatronics systems are a common part of the industrial control systems (ICS) or – in...
Strengthening Financial Services: Embracing the Digital Operational Resilience Act (DORA) for Cybersecurity Resilience – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Boris Khazin, Head of Governance, Risk & Compliance at EPAM Systems, Inc. While concerns about market volatility, liquidity management...
Speaking Cyber-Truth: The CISO’s Critical Role in Influencing Reluctant Leadership – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Craig Burland, CISO, Inversion6 In the C-Suites and boardrooms of modern enterprises, there’s an unwelcome guest that often disrupts...
US Health Dept warns hospitals of hackers targeting IT help desks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The U.S. Department of Health and Human Services (HHS) warns that hackers are now using social engineering tactics to target...
Over 92,000 exposed D-Link NAS devices have a backdoor account – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A threat researcher has disclosed a new arbitrary command injection and hardcoded backdoor flaw in multiple end-of-life D-Link Network Attached...
Data Privacy in Email Communication: Compliance, Risks, and Best Practices – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ahona Rudra Reading Time: 5 min Since the EU adopted the General Data Protection Regulation (GDRP) in 2018, businesses have been forced...
When Man Pages Go Weird – Source: securityboulevard.com
Source: securityboulevard.com – Author: Branden Williams You may not realize that I got my start in the technology world in the early 1990s learning Unix. From...
Malicious Latrodectus Downloader Picks Up Where QBot Left Off – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Source: Yuri Arcurs via Alamy Stock Photo At first, analysts thought the downloader was a variant of well-known malware IcedID —...
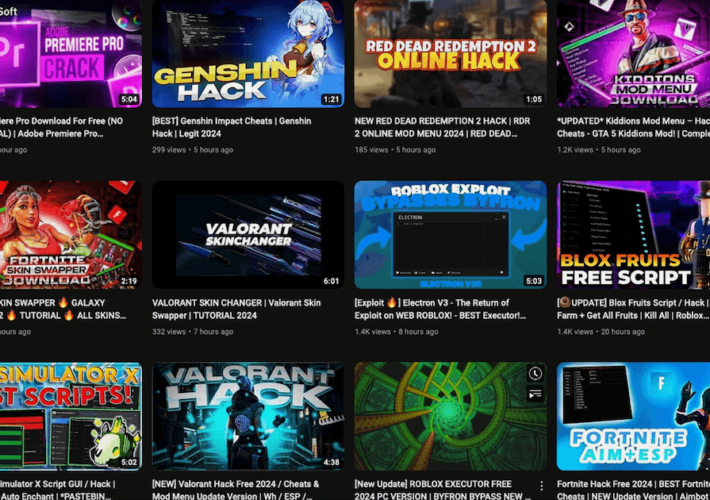
YouTube channels found using pirated video games as bait for malware campaign – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Hackers are distributing malware through multiple YouTube channels that promote cracked or pirated video games, according to researchers at Proofpoint. In...
“Hope Is Not a Strategy”: Cyber Leaders on the Real Keys to Executing a Defense-in-Depth Strategy – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Jesse Fasolo, Director, Technology Infrastructure & Cyber Security, St. Joseph’s Health When it comes to cybersecurity — and by extension, patient...
Friday Squid Blogging: SqUID Bots – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments William • April 5, 2024 5:21 PM Could you imagine discovering that your identity had been used to...
Thread Hijacking: Phishes That Prey on Your Curiosity – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Thread hijacking attacks. They happen when someone you know has their email account compromised, and you are suddenly dropped into an...
Recent Windows updates break Microsoft Connected Cache delivery – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft says Windows 10 updates released since the start of the year are breaking Microsoft Connected Cache (MCC) node discovery...
The Week in Ransomware – April 5th 2024 – Virtual Machines under Attack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Ransomware attacks targeting VMware ESXi and other virtual machine platforms are wreaking havoc among the enterprise, causing widespread disruption and...
Salt Security Applies Generative AI to API Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard Salt Security this week revealed it has embedded a generative artificial intelligence (AI) assistant, dubbed Pepper, into its application programming...
Small business cyber security guide: What you should prioritize & where you should spend your budget – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ryan Healey-Ogden Think of it this way: The more your team is knowledgeable about cyber attacks, the more likely they will be...
Ghostwriter v4.1: The Custom Fields Update – Source: securityboulevard.com
Source: securityboulevard.com – Author: Christopher Maddalena Let’s dive into what makes this so exciting! There’s so much to cover that we won’t be offended if you...
FCC: Phone Network Bugs Must Be Fixed — But are SS7/Diameter Beyond Repair? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings The Federal Communications Commission is finally minded to address decades-old vulnerabilities. Dusty, moldy, prehistoric protocols from the 1980s and ’90s still...
Ivanti CEO Promises Stronger Security After a Year of Flaws – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The chief executive of vulnerability-plagued Ivanti said the management software maker is revamping its security practices after months of reports...
Automating and maintaining SBOMs – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mahesh Raj Mohan Hot Topics FCC: Phone Network Bugs Must Be Fixed — But are SS7/Diameter Beyond Repair? Ivanti CEO Promises Stronger...
xz backdoor Part 2: On the Importance of Runtime Security in the Age of OSS Backdoors – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mike Larkin It’s been a week since the xz backdoor dropped. I stand by my earlier conclusion that the community really dodged...
CISA Unveils Critical Infrastructure Reporting Rule – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nathan Eddy The Cybersecurity and Infrastructure Security Agency (CISA) issued a Notice of Proposed Rulemaking (NPRM) for the Cyber Incident Reporting for...
Update for KernelCare Live Patches for CVE-2024-1086 in AlmaLinux 8 & 9 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Joao Correia The KernelCare team is working on deploying a live patch for CVE-2024-1086 for AlmaLinux 8 and AlmaLinux 9 users. As...
What is Certificate Provisioning? – Source: securityboulevard.com
Source: securityboulevard.com – Author: AnneMarie Avalon Certificate provisioning refers to the process of obtaining, deploying, and managing digital certificates within an organization’s IT infrastructure. These certificates,...
Vietnamese Threat Actor Targeting Financial Data Across Asia – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime CoralRaider Looks for Social Media Accounts That Contain Payment Information Mihir Bagwe (MihirBagwe) • April...
Medical Device Cyberthreat Modeling: Top Considerations – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Healthcare , Industry Specific Threat Modeling Expert Adam Shostack on Critical Mistakes to Avoid Marianne Kolbasuk...
Cloudflare Enters Observability Space With Baselime Purchase – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Next-Generation Technologies & Secure Development , Observability Acquiring Baselime Will Give Developers Better Visibility Into Serverless Platforms Michael Novinson (MichaelNovinson) •...