Source: securityboulevard.com – Author: Kayne McGladrey Last year, the Securities and Exchange Commission (SEC) announced new disclosure rules for publicly traded companies. Regulation S-K Item 106,...
Month: March 2024
How to Get the Most From Your Secrets Scanning – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dex Tovin Secret scanning is essential for unlocking next-level software supply chain security. Get tips & best practices for optimal secret scanning...
The Show Must Go On – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dave Lewis It has been a long time since I last posted on this site. Truth be told it was broken for...
Constella and Social Links Join Forces to Deliver Transformative OSINT Solutions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Laura Bruck March 25, 2024[1] — Social Links, a leading developer of open-source intelligence (OSINT) software, has announced a strategic partnership with...
USENIX Security ’23 – Lukas Lamster, Martin Unterguggenberger, David Schrammel, and Stefan Mangard – HashTag: Hash-based Integrity Protection for Tagged Architectures – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX Security ’23 – Lukas Lamster, Martin Unterguggenberger, David Schrammel, and...
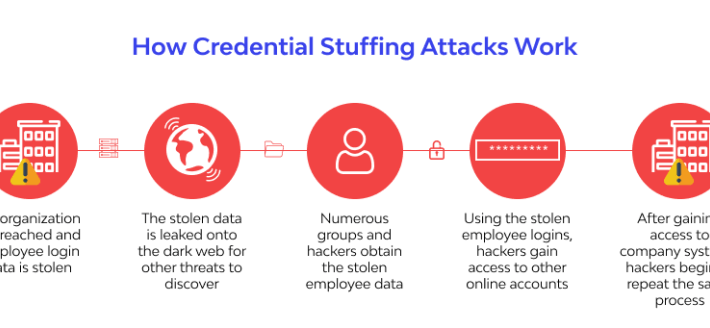
Top 4 Industries at Risk of Credential Stuffing and Account Takeover (ATO) attacks – Source: securityboulevard.com
Source: securityboulevard.com – Author: wlrmblog All industries are at risk of credential stuffing and account takeover (ATO) attacks. However, some industries are at a greater risk...
Log Formatting Best Practices for Improved Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kevin Smith In the event of a security breach, logs play a crucial role in understanding the scope and impact of the...
UK Blames China for 2021 Hack Targeting Millions of Voters’ Data – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The UK government has called out China state-affiliated threat actors for carrying out hacking campaigns against UK institutions and political figures...
Police Bust Multimillion-Dollar Holiday Fraud Gang – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Police in Romania and Spain have struck a blow against a sophisticated cyber-fraud gang that tricked victims out of millions of...
Russian Cozy Bear Group Targets German Politicians – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security researchers have warned Western political parties to be on their guard after uncovering a new cyber-espionage campaign from Russian actors...
European Commission to Investigate Meta Subscription Model – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Privacy , Standards, Regulations & Compliance ‘Pay or Consent’ May Violate the Digital Services Act, Say...
CISOs: Make Sure Your Team Members Fit Your Company Culture – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 CISO Trainings , Recruitment & Reskilling Strategy , Training & Security Leadership Why? Because ‘Culture Eats Strategy for Breakfast,’ as the...
The AI Revolution and White-Collar Workers – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development , Recruitment & Reskilling Strategy Will AI Be a Catalyst...
Hospitals Lobby Feds to Clarify Breach Duties in UHG Attack – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Breach Notification , Healthcare , Industry Specific AHA Wants Change Healthcare on Hook for Notification in Potential Breach Marianne Kolbasuk McGee...
Webinar | The Cost of Convenience: Exploring the Risks of Password Reuse – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 James Condon Director of Security Research, Lacework James Condon is Director of Security Research at Lacework, where he leads the Lacework...
UK Discloses Chinese Espionage Activities – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Deputy Prime Minister Says Violet Typhoon Is Behind Attacks on UK Politicians...
Report Urges Congress to Form an Armed Cyber Military Branch – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Research Shows Military Suffers From Disjointed Cyber Operations Amid New Threats Chris...
CISA Seeks to Curtail ‘Unforgivable’ SQL Injection Defects – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Andrey Popov via Alamy Stock Photo SQL injection vulnerabilities continue to plague supply chains, prompting...
Mitigating Third-Party Risk Requires a Collaborative, Thorough Approach – Source: www.darkreading.com
Source: www.darkreading.com – Author: Matt Mettenheimer Matt Mettenheimer, Associate Director of Cyber Advisory, Cybersecurity Practice, S-RM March 25, 2024 5 Min Read Source: Andriy Popov via...
Japan Runs Inaugural Cyber Defense Drills With Pacific Island Nations – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Stocktrek Images Inc. via Alamy Stock Photo Japan held cyber defense exercises with five Pacific...
GitHub Developers Hit in Complex Supply Chain Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer Source: Monticello via Shutterstock An unidentified group of threat actors orchestrated a sophisticated supply chain cyberattack on members...
AWS CISO: Pay Attention to How AI Uses Your Data – Source: www.darkreading.com
Source: www.darkreading.com – Author: Grant Gross, Contributing Writer Source: Eric Muhamad Naris via Alamy Stock Photo Enterprises are increasingly adopting generative artificial intelligence (AI) to automate...
Apple Stingy With Details About Latest iOS Update – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: GK Images via Alamy Stock Photo Apple has released iOS 17.4.1, its latest security update,...
8 Strategies for Enhancing Code Signing Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Murali Palanisamy 4 Min Read Source: Andrea Danti via Alamy Stock Photo COMMENTARY The recent news that hackers had breached remote access...
Kenya to TikTok: Prove Compliance With Our Privacy Laws – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Aleksey Zotov via Alamy Stock Photo Kenya’s data protection agency has ordered TikTok to share...
Why AI Obituary Scams Are a Cyber-Risk for Businesses – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Delphotos via Alamy Stock Photo Two-bit scammers are generating near-instant obituaries for recently deceased strangers, taking advantage...
Strata Identity Releases New Authentication Recipes – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Poptika via Shutterstock Strata Identity has announced a Microsoft Identity Cookbook that aims to help...
Does Zero Trust Improve Productivity? – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Zac Amos, Features Editor, ReHack Zero trust has gained significant attention as an effective approach to secure digital assets....
Why Digital Trust Has Become More Critical Than Cybersecurity & Privacy – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team WHY DIGITAL TRUST MATTERS By Lalit Ahluwahli, CEO & Founder, DigitalXForce & iTrustXForce We all know that cybersecurity and privacy...
Cybersecurity Threats in Global Satellite Internet – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Gizem Yılmaz, Master Expert Data Analyst, Turkcell Technology Internet via satellite was first used for military purposes in the...