Source: www.infosecurity-magazine.com – Author: 1 A threat actor has been distributing remote access Trojans (RATs) on Android and Windows operating systems using online meeting lures, according...
Month: March 2024
US Sanctions Predator Spyware Maker Intellexa – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The US government has announced further action against commercial spyware makers by sanctioning two people and five “entities” associated with the...
South Korean Police Develops Deepfake Detection Tool Ahead of April Elections – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Read more on deepfake policy changes ahead of the 2024 elections: OpenAI Announces Plans to Combat Misinformation Amid 2024 Elections Meta’s...
ALPHV/BlackCat Ransomware Servers Go Down – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The ALPHV/BlackCat ransomware group’s operations seem to have halted amid allegations of defrauding an affiliate involved in the Optum attack, which targeted...
American Express Warns Credit Card Data Exposed in Third-Party Breach – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 American Express (Amex) has alerted customers that their credit card details may have been compromised following a third-party data breach. In...
Network Perception Introduces Rapid Verification of Zone-to-Zone Segmentation – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE CHICAGO — (BUSINESS WIRE) — Network Perception, innovators of operational technology (OT) solutions that protect mission-critical assets, today introduced new...
From Prep to Pass, Scytale Launches Its Built-In Audit, Transforming It Into The Complete Compliance Hub for SaaS – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mor Avni, Product Manager, Scytale For SaaS companies, it’s hard not to hear the word ‘audit’, without your heart skipping a beat...
George Kurtz: There’s a Difference Between Price, Total Cost – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cloud-Native Application Protection Platform (CNAPP) , Security Information & Event Management (SIEM) , Security Operations Palo Alto Offering Free Products Won’t...
The Insecurity of Video Doorbells – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog The Insecurity of Video Doorbells Consumer Reports has analyzed a bunch of popular Internet-connected video doorbells. Their security is...
Interlinked Computingin 2040: Safety,Truth, Ownership, and Accountability
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Apple fixes two new iOS zero-days exploited in attacks on iPhones – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Apple released emergency security updates to fix two iOS zero-day vulnerabilities that were exploited in attacks on iPhones. “Apple is...
GhostLocker 2.0 Haunts Businesses Across Middle East, Africa & Asia – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Leyden, Contributing Writer Source: Zoonar GmbH via Alamy Cybercriminals have developed an enhanced version of the infamous GhostLocker ransomware that they...
Seoul Spies Say North Korea Hackers Stole Semiconductor Secrets – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Siource: Olekcii Mach via Alamy Stock Photo North Korean hackers have allegedly stolen South Korean microchip...
Critical TeamCity Bugs Endanger Software Supply Chain – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Source: Jatinder Kumar via Alamy Stock Photo Cloud versions of the JetBrains TeamCity software development platform manager...
Zero-Click GenAI Worm Spreads Malware, Poisoning Models – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Denis Crawford via Alamy Stock Photo A worm that uses clever prompt engineering and injection is able...
Amex Customer Data Exposed in Third-Party Breach – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Source: Ian Dagnall via Alamy Stock Photo American Express is notifying its customers that their credit...
Ukraine Claims it Hacked Russian MoD – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Hackers operating from Ukraine’s Main Intelligence Directorate (GUR) have claimed another scalp; the Russian Ministry of Defense (MoD). The GUR, part...
TeamCity Users Urged to Patch Critical Vulnerabilities – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Software developer JetBrains has warned users of its popular TeamCity CI/CD tool that they should prioritize patching of two new vulnerabilities...
Overview of AI Regulations and Regulatory Proposals of 2023 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michelle Ofir Geveye “AI is too important not to regulate—and too important not to regulate well,” asserts Google, capturing the sentiment resonating...
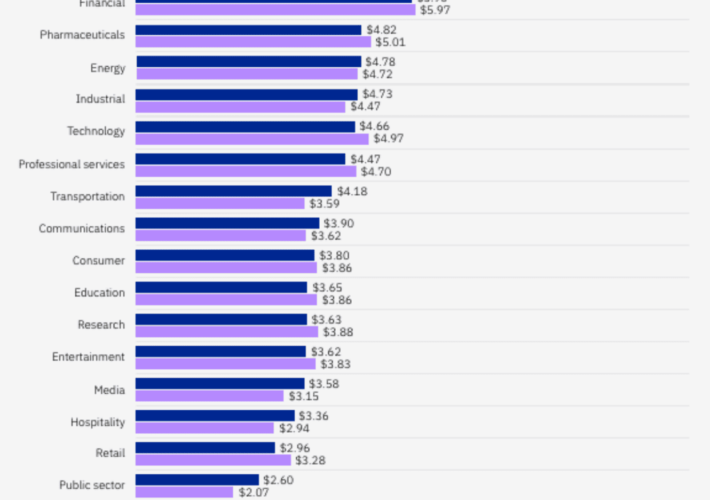
Prevention & Cure: Countermeasures Against Healthcare Cyberattacks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nicholas Tan A recent successful cyberattack on a large technology provider for hospitals and pharmacies in the US has left patients unable...
LogRhythm Promotes Joanne Wong to Interim Chief Marketing Officer – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nicholas Tan A pioneer of LogRhythm’s Asia Pacific operations, Joanne Wong’s appointment reinforces LogRhythm’s commitment to employee advancement through strategic internal promotions...
TrustCloud Welcomes Security and Compliance Expert Dixon Wright as VP GRC Transformation – Source: securityboulevard.com
Source: securityboulevard.com – Author: Erin Crapser Wright Joins TrustCloud as the company expands solutions for customers, partners and auditors, and invests in its own security program...
Data Security Posture Management Should Focus on Securing the Data – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ron Arden Organizations use and store many types of data. Some of it is high value containing business-critical information or regulated data,...
Entro Streamlines Machine Identity Life Cycle Management – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard Entro has added a life cycle management capability to its namesake platform for discovering and managing machine identities. In addition,...
USENIX Security ’23 – Shawn Shan, Jenna Cryan, Emily Wenger, Haitao Zheng, Rana Hanocka, Ben Y. Zhao – Glaze: Protecting Artists From Style Mimicry By Text-to-Image Models – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX Security ’23 – Shawn Shan, Jenna Cryan, Emily Wenger, Haitao...
Researchers Give Birth to the First GenAI Worm – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matthew Rosenquist It was bound to happen — researchers have created a 1st generation AI worm that can steal data, propagate malware, and spread...
Daniel Stori’s ‘Obfuscated Code’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the inimitable Daniel Stori at Turnoff.US. Permalink *** This is a Security Bloggers Network syndicated blog from Infosecurity.US authored...
CISA Warns Phobos Ransomware Groups Attacking Critical Infrastructure – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Phobos, a complex ransomware-as-a-service (RaaS) operation that has been around for five years and is includes multiple variants, continues to...
German Police Shut Underground Crimemarket Forum – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Government 3 Arrested and Domain Shuttered in the Investigation by Düsseldorf Police Akshaya Asokan...
Live Webinar | Cyber Resiliency: The Building Blocks for transforming Australia’s Enterprise Security and Risk Management – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Live Webinar | Cyber Resiliency: The Building Blocks for transforming Australia’s Enterprise Security and Risk Management Original Post url: https://www.databreachtoday.com/webinars/live-webinar-cyber-resiliency-building-blocks-for-transforming-w-5461 Category...