Source: www.darkreading.com – Author: Dark Reading Staff Source: Gregg Vignal via Alamy Stock Photo Henry Onyedikachi Echefu, one of the three Nigerian men who were involved...
Month: March 2024
How to Ensure Open-Source Packages Are Not Mines – Source: www.darkreading.com
Source: www.darkreading.com – Author: Agam Shah, Contributing Writer Source: Steven Morris via Alamy Stock Photo Open-source repositories are critical to running and writing modern applications, but...
JetBrains TeamCity Mass Exploitation Underway, Rogue Accounts Thrive – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Valeriy Kachaev via Alamy Stock Vector Attacks targeting two security vulnerabilities in the TeamCity CI/CD platform have...
Silence Laboratories Raises $4.1M Funding to Enable Privacy Preserving Collaborative Computing – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SINGAPORE – 29th February 2024 — In the modern age, large companies are wrestling to leverage their customers’ data to...
Enjoy 2 Years of Unrestricted Access to Your Favorite Content for Only $40 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Academy Published March 8, 2024 We may earn from vendors via affiliate links or sponsorships. This might affect product placement on...
Dropbox Used to Steal Credentials and Bypass MFA in Novel Phishing Campaign – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A novel phishing campaign leveraged legitimate Dropbox infrastructure and successfully bypassed multifactor authentication (MFA) protocols, new research from Darktrace has revealed....
UnitedHealth Sets Timeline to Restore Change Healthcare Systems After BlackCat Hit – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 UnitedHealth Group has published a timeline to restore Change Healthcare’s systems following the BlackCat/ALPHV ransomware attack, which has led to delays...
A Taxonomy of Prompt Injection Attacks – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Researchers ran a global prompt hacking competition, and have documented the results in a paper that both gives a lot...
Do You Know Where Your Data Is? How Law Firms Can Protect Their Most Valuable Asset – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By John A. Smith, CSO, Conversant Group If data is the new oil, this holds especially true for law firms...
Building a Secure Data-Protection Infrastructure to Protect against the MOVEit Hack – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Carl Cadregari, Executive Vice President, FoxPointe Solutions Regardless of the industry in which they operate, organizations have likely witnessed...
AI and the Next Wave of Robocalls: Protecting Carriers and Consumers from Sophisticated Voice Fraud – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Tim Ward, Chief Strategy Officer, XConnect Robocalls are relentlessly targeting consumers and causing mistrust for the telecom industry as...
What Happened in Cybersecurity in 2023: A Summary of Security Incidents, Vulnerability Information, and Cybersecurity Trends – Source: securityboulevard.com
Source: securityboulevard.com – Author: NSFOCUS The year 2023 witnessed a dynamic and complex cybersecurity landscape, with various security incidents, vulnerabilities, and trends emerging and evolving. Today,...
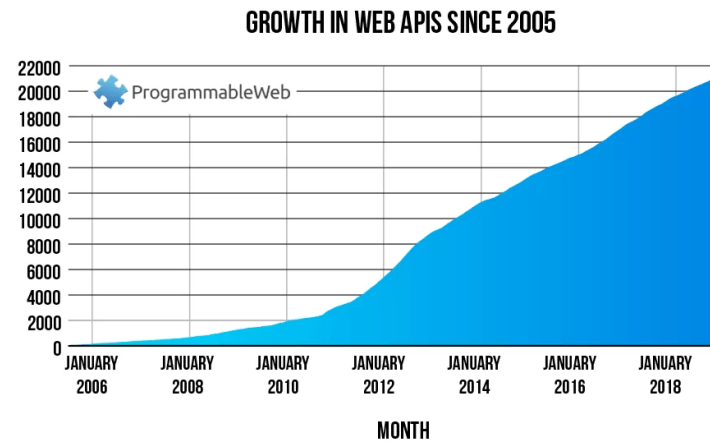
Top 4 Essential Strategies for Securing APIs To Block Compromised Tokens – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jaweed Metz Government bodies are clamping down heavily on institutions and organizations that handle sensitive customer data. For APIs, tokens are used...
News alert: Badge expands availability of ‘Enroll Once and Authenticate on Any Device’ software – Source: securityboulevard.com
Source: securityboulevard.com – Author: cyberwire San Francisco, Calif., Mar. 7, 2024 — Badge Inc., the award-winning privacy company enabling Identity without Secrets™, today launched a new Partner...
Annual State of Email Security by the Numbers – Source: securityboulevard.com
Source: securityboulevard.com – Author: Cofense Malicious email threats bypassing all secure email gateways (SEGs) on the market increased over 100% in the past year. How...
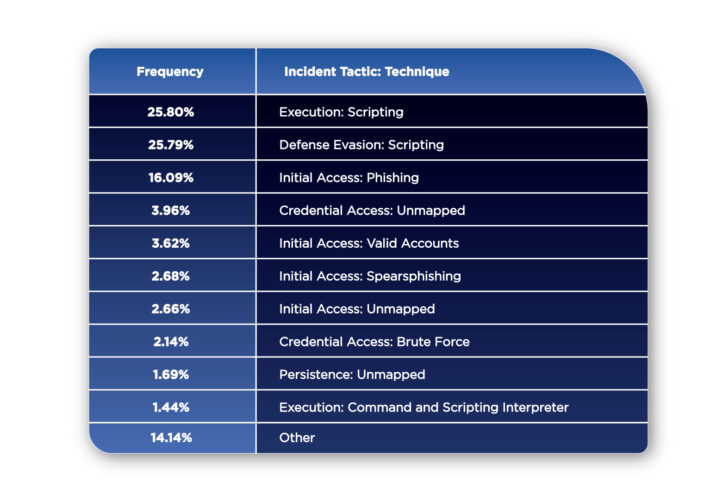
The 10 Most Common MITRE Tactics & Techniques of 2023 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Pierre Noujeim SOAR solutions create a centralized queue of all incidents going on in a security team’s environment. Endpoint, SIEM, email, behavior,...
USENIX Security ’23 – Daniel W. Woods, Rainer Böhme, Josephine Wolff, Daniel Schwarcz – Lessons Lost: Incident Response in the Age of Cyber Insurance and Breach Attorneys – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX Security ’23 – Daniel W. Woods, Rainer Böhme, Josephine Wolff,...
Response to the Revised CISA Advisory (AA23-353A): #StopRansomware: ALPHV BlackCat – Source: securityboulevard.com
Source: securityboulevard.com – Author: Francis Guibernau On February 27, 2024, the Cybersecurity and Infrastructure Security Agency (CISA) notified the revision of the Cybersecurity Advisory (AA23-353A) which...
LockBit Ransomware Affiliates Leverage Citrix Bleed Vulnerability (CVE-2023-4966) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Darren Williams Cybersecurity agencies have sounded alarm bells about active exploitation of a critical vulnerability in Citrix application delivery controllers (ADCs) and...
Randall Munroe’s XKCD ‘Ice Core’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
NSA Issues Guidance for Enterprises Adopting Zero Trust – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The National Security Agency (NSA) wants organizations adopt zero-trust framework principles to protect their enterprise networks and is releasing guidance...
CISA, NSA share best practices for securing cloud services – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams The NSA and the Cybersecurity and Infrastructure Security Agency (CISA) have released five joint cybersecurity bulletins containing on best practices...
Switzerland: Play ransomware leaked 65,000 government documents – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The National Cyber Security Centre (NCSC) of Switzerland has released a report on its analysis of a data breach following...
Windows 10 KB5001716 update fails with 0x80070643 errors, how to fix – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Microsoft is pushing out a Windows 10 KB5001716 update used to improve Windows Update that is ironically failing to install,...
MiTM phishing attack can let attackers unlock and steal a Tesla – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Update: Title and content updated to clarify this is MiTM phishing attack conducted using a Flipper Zero but it could...
AnyCubic fixes exploited 3D printer zero day flaw with new firmware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams AnyCubic has released new Kobra 2 firmware to fix a zero-day vulnerability exploited last month to print security warnings on...
Google engineer caught stealing AI tech secrets for Chinese firms – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The U.S. Department of Justice (DoJ) has announced the unsealing of an indictment against Linwei (Leon) Ding, 38, a former...
PetSmart warns of credential stuffing attacks trying to hack accounts – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Pet retail giant PetSmart is warning some customers their passwords were reset due to an ongoing credential stuffing attack attempting...
Critical TeamCity flaw now widely exploited to create admin accounts – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ionut Ilascu Hackers have started to exploit the critical-severity authentication bypass vulnerability (CVE-2024-27198) in TeamCity On-Premises, which JetBrains addressed in an update...
Hacked WordPress sites use visitors’ browsers to hack other sites – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Hackers are conducting widescale attacks on WordPress sites to inject scripts that force visitors’ browsers to bruteforce passwords for other...